Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

本文の内容は、2022年10月19日にAlessandro Brucatoが投稿したブログ(https://sysdig.com/blog/cve-2022-42889-text4shell/)を元に日本語に翻訳・再構成した内容となっております。
新しい重大な脆弱性
このペイロードは、"${prefix:name}"で構成されており、これがString Lookupのトリガーとなります。前述の通り、"script"、"dns"、"url "は、脆弱性を悪用するためのプレフィックスとして使用することができるキーです。
この脆弱性は、クリティカルな深刻度9.8と評価されており、常にリモートコード実行(RCE)となり、攻撃者はマシン上で任意のコードを実行し、ホスト全体を危険にさらすことが可能となります。
Apache Commons Text のバージョン 1.5 から 1.9 が影響を受け、バージョン 1.10 でパッチが適用されています。
予備知識
Apache Commons Textは、"文字列を操作するアルゴリズムに特化したライブラリ" と説明されているJavaのライブラリで、汎用のテキスト操作ツールキットと見なすことができます。
コーディングに慣れている方でも、Commons Textに依存するコードに遭遇したことがあるかもしれませんし、現在ラップトップや本番環境で動作させているアプリケーションで使用されている可能性があります。
CVE-2022-42889 の問題
この脆弱性は、Commons Text ライブラリに含まれる StringSubstitutor インターポレータークラスに影響を及ぼします。デフォルトのインターポレーターでは、リモートでコード実行される可能性のある文字列の検索が可能です。これは、StringLookupFactory クラスのドキュメントによると、"script", "dns", "url" ルックアップキーを、本来あるべきものとは逆にデフォルトで補間してしまうというロジックの欠陥に起因しています。これらのキーは、攻撃者がルックアップを経由して任意のコードを実行することを可能にします。
本脆弱性を悪用するためには、以下の要件を満たす必要があります:
- Apache Commons Text のバージョン 1.5 から 1.9 までのバージョンを使用する。
- StringSubstitutor インターポレーターを使用する。
StringSubstitutor インターポレーターは、Log4Shell につながった Log4j の文字列置換ほど広く使われていないことをお知らせしておきます。
CVE-2022-42889 を悪用する方法
攻撃を再現するために、脆弱性のあるコンポーネントをDockerコンテナにデプロイし、攻撃者がコントロールするEC2インスタンスからアクセスしました。netcat (nc) コマンドを使用し、脆弱性のあるアプリケーションとのリバースシェル接続を開くことができます。
脆弱なウェブアプリケーションは、検索APIを公開しており、クエリーはCommons TextのStringSubstitutorを介して挿入されます:
http://web.app/text4shell/attack?search=<query>
以下のペイロードを使用すると、脆弱性を悪用し、リバースシェルを開くことができます:

細工したリクエストを送信する前に、netcat (nc) コマンドを使用してリバースシェル接続をセットアップし、ポート 9090 でリッスンする必要があります。
nc -nlvp 9090
次に示すように、ペイロードをURLエンコードして、細工したリクエストを送信することができます。
Curlペイロード text4shell cve-2022-42889
攻撃者は、脆弱なアプリケーションとの接続を開くことに成功したことがわかります。
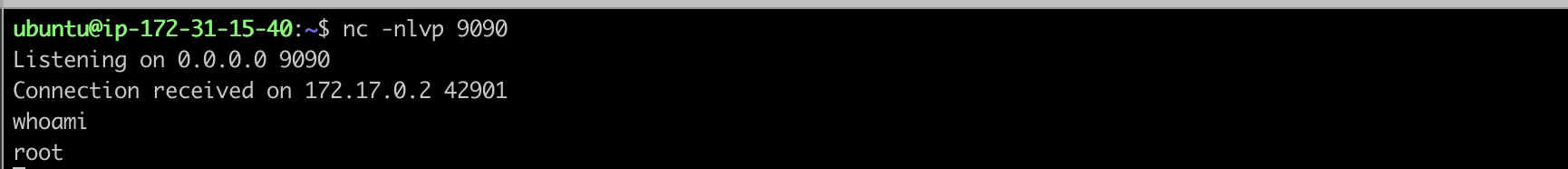
text4shell cve-2022-42889 nc 接続
これで、攻撃者はrootとして脆弱性のあるマシンと対話し、任意のコードを実行できるようになります。
CVE-2022-42889の影響について
CVSSv3 によると、深刻度は 9.8 で、CRITICAL です。
深刻度は、悪用が容易であることと、機密性、完全性、可用性の面で大きな影響を与える可能性があることから、Criticalとなりました。前のセクションで示したように、細工したリクエストで、脆弱なシステムを完全に制御することができます。
しかし、この脆弱性は、以前の log4shell や spring4shell のような影響を与えるとは思えません。
脆弱性のあるコンポーネントを見ると、悪用される可能性があるのは、Apache Commons Textライブラリの使用に関連しています。具体的には、StringSubstitutorオブジェクトを何らかのユーザー制御の入力で実装している場合のみ悪用が可能です。本番環境でのこの実装は、Log4jの脆弱な文字列置換ほど一般的ではありません。したがって、Text4Shellの大規模な影響は、Log4Shellとあまり比較になりません。
CVE-2022-42889の検出と緩和策
CVE-2022-42889の影響を受けている場合、アプリケーションをバージョン1.10に更新する必要があります。
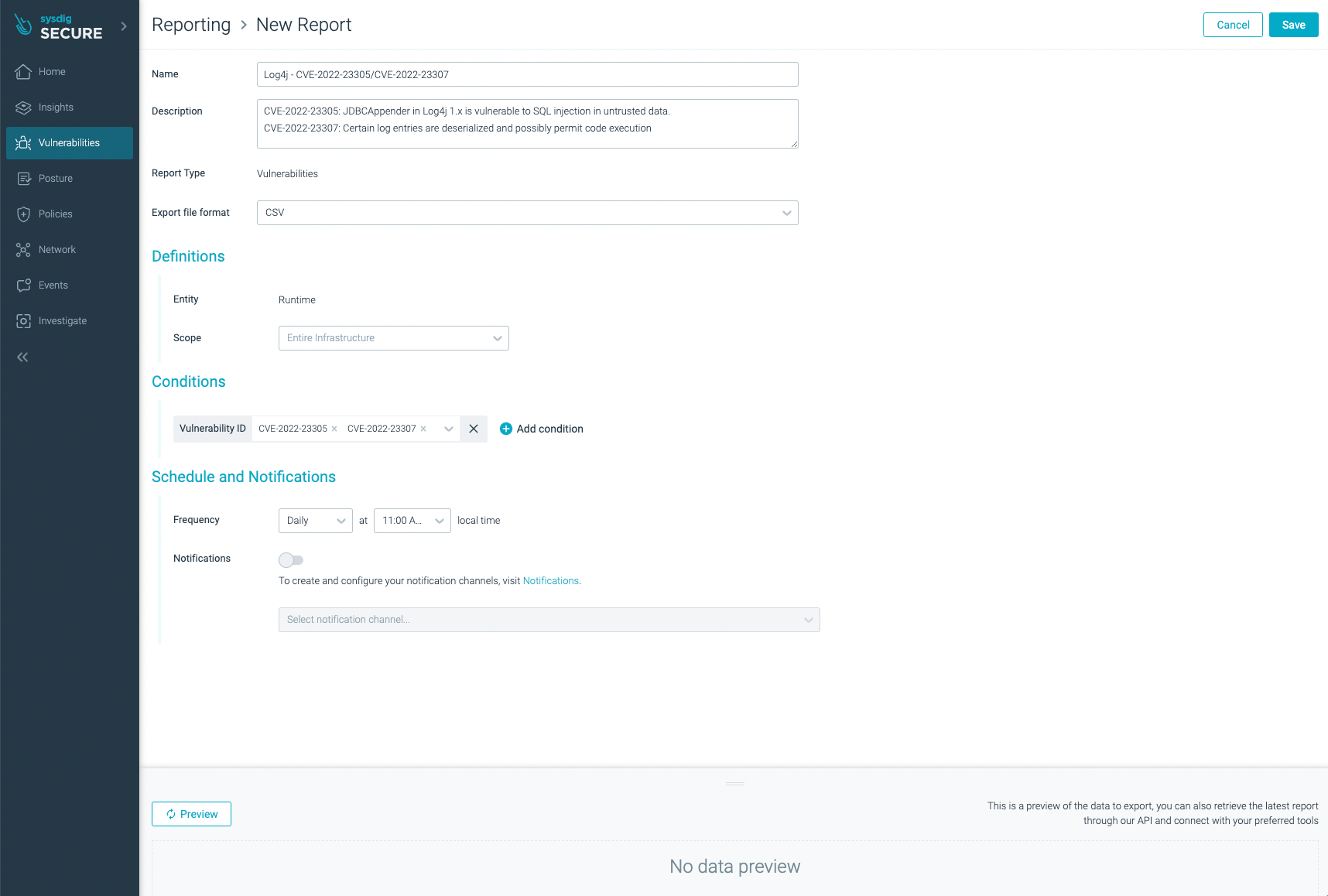
以前のCVE-2022-22963で見たように、この脆弱性はアプリケーションライフサイクルの3つの異なるフェーズで検出することができます。
- ビルドプロセス:イメージスキャナーを使用する。
- デプロイメントプロセス:アドミッションコントローラー上のイメージスキャナーを使用します。
- ランタイム検出エンジンを使用したランタイム検出フェーズ:Falcoを使って、すでにデプロイされたホストやPodの悪意のある動作を検出します。
Sysdigイメージスキャナーを利用することで、脆弱性のあるパッケージの検出が可能です。
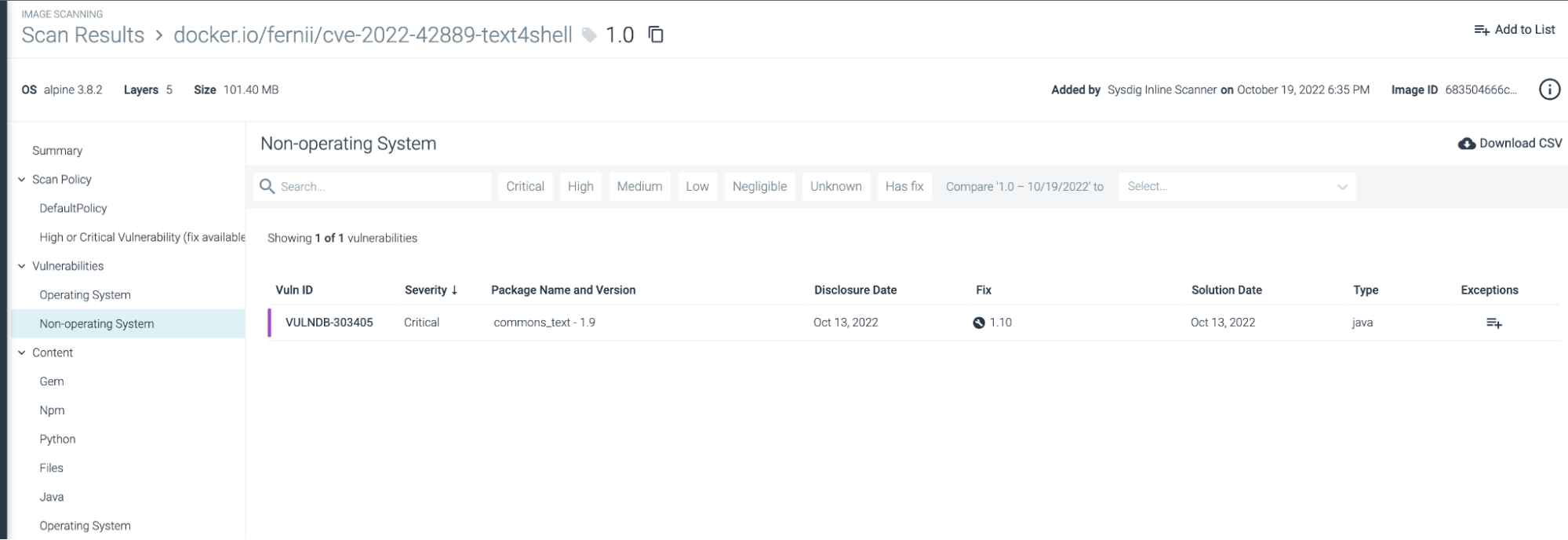
Sysdigでcve-2022-42889 text4shellを検出する。
まとめ
CVE-2022-42889は、特定の条件下で悪用される脆弱性であるため、今年に見られた他の脆弱性ほどは注目されていませんが、それでも早急に対応することが重要です。
安全のために、最新バージョンのパッチを適用して脆弱性を軽減し、スキャナーを使用して影響を受けているかどうかを確認します。また、脆弱性を緩和するために必要な対策を講じ、インフラストラクチャーやアプリケーションの実行時の監視を止めないことが重要です。
脆弱性とは何かについてもっと知りたい場合は、What is a Vulnerabilityでもっと掘り下げてみてください。
[embed]https://youtu.be/CRDhTFpfDog[/embed]


