
Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

It’s been just over a year since open source Falco graduated from the Cloud Native Computing Foundation® (CNCF) during KubeCon EU 2024, and the momentum hasn’t slowed down. From advancements in real-time threat response and expanded audit event collection across cloud-native environments, to reaching 150 million downloads and even new open-source technologies like Stratoshark being built on Falco’s libraries, the project continues to evolve rapidly.
Let’s explore some of the key Falco developments since CNCF graduation and a look at what’s to come – but first, here’s a quick look at some of the highlights:
- The creation and donation of Falco Talon to falcosecurity Github.
- Sysdig Agent for Windows (based on Falco): Neat!
- Widespread advancements and 40% growth across the Falco Plugins landscape.
- Falco Feeds…and what that means for you.
- The evolution of Wireshark and Falco’s legacy with the introduction of Stratoshark!
From Falco to Sysdig: How Syfe simplified compliance and threat detection
With Sysdig, the financial firm got best-in-class cloud threat detection – without constant upkeep.

Falco Talon
Developed by Falco maintainer Thomas Labarussias, Falco Talon is a dedicated response engine designed specifically for Falco events. On September 6, 2024, a pull request was submitted to donate this newly developed engine to the official falcosecurity GitHub repo.
Talon is a no-code solution that provides a user-friendly experience similar to Falco rules and uses familiar .yaml files with append and override mechanisms. This allows security teams to define sequential response actions while receiving structured log outputs with an associated Trace ID.
Installing Falco Talon is seamless through the official falcosecurity Helm charts for Kubernetes deployments. Response actions can be mapped to Falco detection rules based on rule name, priority, tags, or even specific output fields. This significantly enhances the detection and response workflow by ensuring real-time, in-line response actions while giving DevOps teams the flexibility to fine-tune event matching and override default rules as needed.
Sysdig Agent for Windows based on Falco technology
Building on the same YAML-based detection rule logic beloved by the open-source Falco community, the Sysdig team developed an agent for Windows based on Falco; it is an integral component of the Sysdig platform that detects real-time threats directly from the Windows kernel. Similar to how Falco operates on Linux – using system call collection via kernel modules or an eBPF probe – this Windows implementation maintains familiar abstractions like Macros and Lists, ensuring a seamless user experience.
The key difference lies in its approach to event collection. Instead of a kernel probe, the Windows agent leverages the Event Tracing for Windows (ETW) driver, providing an efficient and reliable method for monitoring Windows workload activity inside Kubernetes.
Below is an example of a detection rule in the Sysdig platform using the Sysdig Agent for Windows:
Falco plugins
Falco plugins have long been essential for integrating Falco and Sysdig with third-party event sources. Thanks to an active and creative community of cloud-native developers, the plugin ecosystem has grown by 40% since Falco’s CNCF graduation, driving improvements in cloud security for everyone. Check out and explore the full list of registered plugins here on GitHub.
The expanding list of Falco plugins provides additional capabilities such as extended visibility to monitor additional services like Microsoft Entra ID (formerly Microsoft Azure Active Directory). These plugins become increasingly impactful, as your cloud environment grows and more SaaS services integrate with your cloud-native systems.
Below is an example of a Falco detection rule based on the Azure Entra plugin in the Sysdig platform:
This cloud-based identity and access management (IAM) service enables authentication and authorization for Microsoft services, including Microsoft 365, MS Azure, and their managed Kubernetes service (AKS). Some organizations may not immediately recognize the value of Falco’s extensive plugin ecosystem. However, incidents like the Okta Cross-Tenant Impersonation attack on MGM and Caesars in late 2023 highlight its importance. The Falco team had already developed a plugin to monitor this behavior within Okta Identity Services, demonstrating the proactive security benefits of its ecosystem.
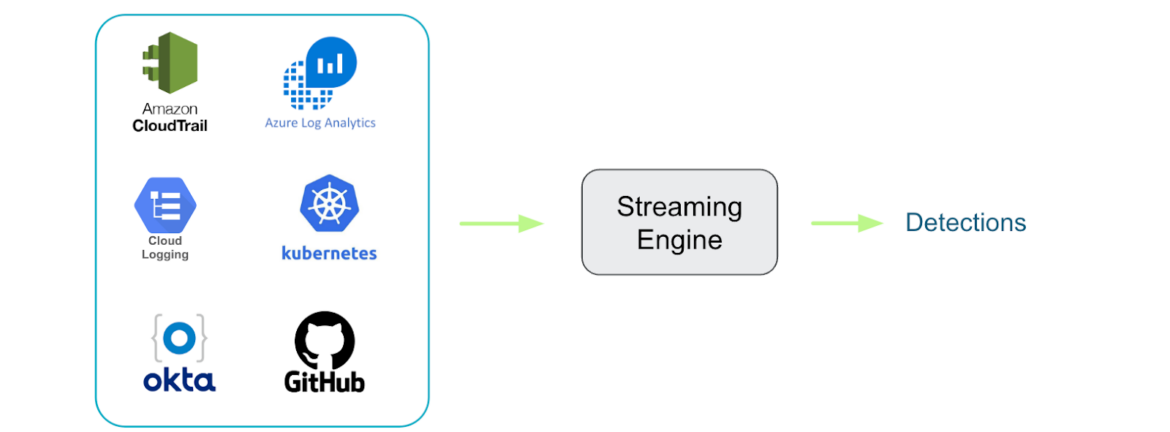
With Falco Plugins, stream events from just about any 3rd-party real-time event source
Falco Feeds
Falco’s plugin architecture and detection rules are highly customizable, offering powerful flexibility. However, as your systems scale – much like with Kubernetes – this flexibility can introduce complexity. While Falco provides a useful rules maturity matrix, its out-of-the-box rules still require tuning and validation to accurately detect security threats within the unique constraints of your Kubernetes clusters.
Many managed detection and response solutions trade off flexibility for convenience, limiting the control teams expect from an open-source project like Falco. Sysdig takes a different approach with Falco Feeds, a solution backed by the Sysdig Threat Research Team (TRT) that delivers enterprise-grade expert-written Falco rules via the falcoctl CLI tool. This allows teams to seamlessly adopt new rules without the burden of ongoing maintenance or production downtime.
With Falco Feeds, you get the best of both worlds: the open-source power of tools like falcosidekick and Falco Talon, combined with the ease of managed detection rules without needing to overhaul your existing infrastructure.
Falco libraries
Imagine combining the deep system introspection of sysdig CLI and Falco with the intuitive user experience of Wireshark – that’s exactly what Stratoshark delivers.
According to the official Wireshark documentation, falcodump allows users to capture log data using any Falco source plugins. Stratoshark builds on this by leveraging the same core libraries that power Falco: libsinsp (System Inspection Library) and libscap (System Capture Library).
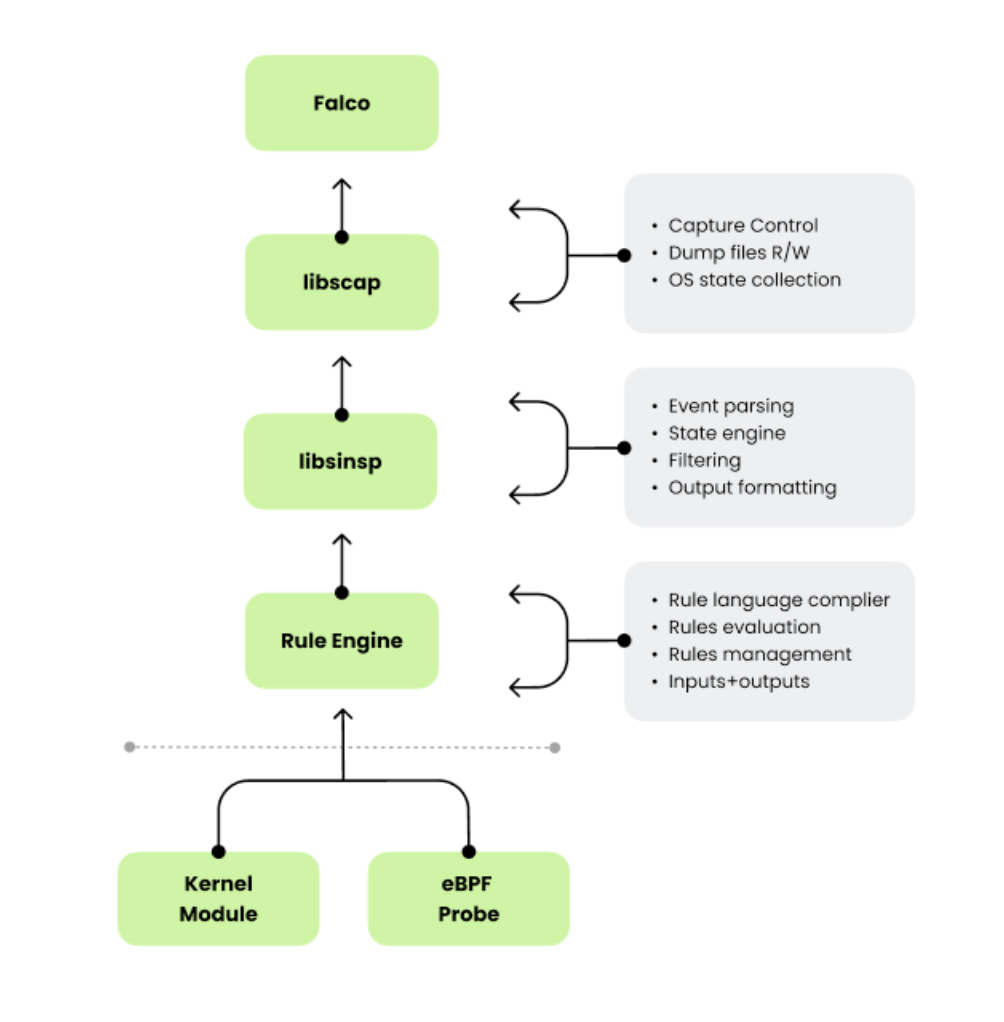
These libraries enable Falco and other tools to extract, enrich, and analyze system call events. Stratoshark utilizes them to allow users to read Syscall Capture (SCAP) files, much like how Wireshark users interact with Packet Capture (PCAP) files. Launched in January 2025, Stratoshark brings powerful system call analysis to a familiar Wireshark-style workflow. [Read more here.]
What’s next for Falco?
Falco’s journey is far from over. As cloud-native security threats grow in complexity, Falco is evolving to meet them head-on. The focus for the coming year is clear: deeper Kubernetes integration, a more sophisticated plugin system, and a shift toward automation in runtime security. Perhaps the most exciting development, though, is the growing synergy between Falco and Stratoshark. Together, they are setting the foundation for a new security paradigm – one where detection, investigation, and response are seamlessly unified.
Runtime security has always been about visibility, but as Kubernetes environments scale, visibility alone isn’t enough. Falco is tackling this by modernizing its stack, making security more automated and easier to deploy. In the future, Falco will simplify fleet-wide deployment, while enhancements to its plugin system will enable deeper integration with third-party security tools. Improved data capture and analysis will provide security teams with more actionable insights, reducing alert fatigue and drastically reducing response times.
While Falco has long been the go-to for runtime detection, the next step is closing the gap between detection, investigation, and response. That’s where Stratoshark comes in. Falco and Stratoshark will pioneer a Kubernetes Detection and Response (KDR) approach. Tighter integration between the tools, automated forensic workflows, and collaboration between the Falco and Wireshark communities will redefine open source runtime security.
Looking ahead, security in Kubernetes environments will shift from isolated detection tools to fully integrated security lifecycles. Over the next few years, KDR will become the standard. The collaboration between Falco and Stratoshark will create an open-source security framework that simplifies threat mitigation. Security teams in the near future will rely on fully automated systems capable of detecting, analyzing, and responding to threats in real time – eliminating today’s fragmented, heavily manual approaches.
In conclusion
Falco’s journey is just getting started. As cloud-native security threats become more sophisticated, Falco continues to evolve, staying ahead of the curve. As we look ahead, I expect that Falco’s ecosystem will increase by at least 50% in the coming year through plugins, ensuring deeper integrations with third-party services and giving users greater extensibility.
I also predict that the Wireshark and Falco communities will become more interconnected. Stratoshark brings an entirely new dimension to system introspection, making it easier than ever to analyze syscall capture data with a familiar Wireshark-like experience. As open source often leads the way, through Stratoshark, Wireshark, and Falco, the community will realize the security advantages of having deeply integrated threat detection and advanced introspection capabilities. As often happens, vendors will then move to add the same capabilities.
As businesses relying on open source security tools grow rapidly and cloud attacks continue to evolve, I predict more teams will look for additional support. That support can manifest itself in a few ways, including enterprise-ready solutions like Sysdig Secure and hybrid approaches like Falco Feeds. Take Syfe, for example. Syfe began its journey with Falco for its customization and visibility over two years ago, but as its cloud security needs evolved, they concluded that Sydig Secure, an enterprise-managed solution with Falco at its core, was better aligned with their business needs. Other organizations will choose a hybrid approach to scale their Falco environments, through Falco Feeds by Sysdig. Implementing Falco Feeds provides security teams with a fully managed advanced detection rule set curated by the elite Sysdig Threat Research Team. This ruleset also helps teams tackle complex regulatory requirements, streamline compliance audits, and maintain a strong security posture through effective classification and tagging specific frameworks, including MITRE ATT&CK, NIST, NIS2, DORA, SOC2, HIPAA, and FedRAMP.
With an active community, new enterprise-ready enhancements, and continued investment in open-source innovation, Falco will remain at the forefront of cloud-native Threat detection and response (TDR). Whether you’re leveraging Falco in its open-source form or adopting Sysdig enterprise offerings, one thing is clear: Falco’s momentum isn’t slowing down anytime soon.
From Falco to Sysdig: How Syfe simplified compliance and threat detection
With Sysdig, the financial firm got best-in-class cloud threat detection – without constant upkeep.



