
Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

Occasionally, you get exposed to something so logical that you literally take pause and smile quizzically asking yourself "Why didn't I think of this before?"
I have had this reaction on several occasions. This happened when I read Sounil Yu's Cyber Defense Matrix and the logical way that it provided actionable insights on how to use the NIST Cybersecurity Framework across different asset classes (e.g., applications, data, networks, users, and devices). Sounil's approach just made sense and, as a CISO, we need things that make sense and are actionable. Ours is a noisy profession and CISOs suffer from information overload. We benefit from clear, practical, and actionable insights that can drive our security programs forward and reduce both noise and risk.
"Recently, I saw this graphic from Sysdig that provoked the same positive reaction I had while reading the Cyber Defense Matrix. This graphic produced a blinding flash of the obvious – our noisy environments can be calmed, and risk factors dramatically reduced, by focusing on the subset of material risks that occur at runtime."
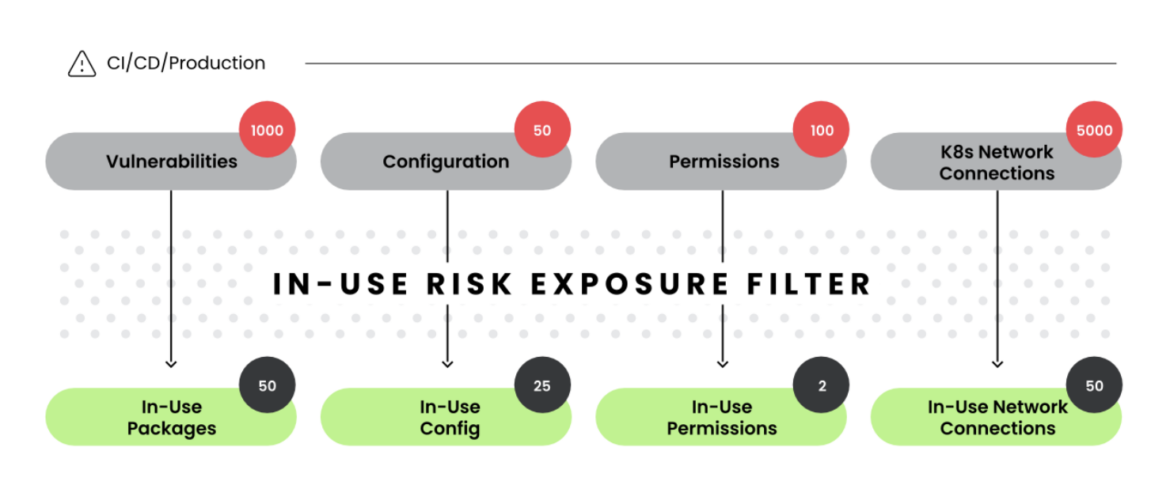
Take a moment and look at the graphic below. On the left, are the seemingly infinite number of variables at risk that we must manage to help our organizations reduce cyber risks (in this case with applications). These risks arise from major areas of system operation including packages deployed, permissions assigned, and configurations used. On the right, is the more manageable portfolio of risks that warrant our teams' attention. This graphic hit like a ton of bricks.
Like our vulnerability management programs, prioritization and filtering are essential. Large enterprises have thousands or tens of thousands of vulnerabilities that require mitigation. Best case, some of these may be patchable and some may require remediation in the form of code fixes. Worst case, some may require a system redesign and/or the implementation of new security controls. From this mountain of vulnerabilities, however, only a small subset are actually exploited – to wit the value of the Cybersecurity and Infrastructure Security Agency's Known Exploited Vulnerabilities Catalog. Most vulnerabilities are simply noise and largely mitigated with our current security applications and tools. Known exploited vulnerabilities, however, warrant our attention, validation of their status in our operating environments, and timely remediation. Focusing on exploited versus potential risks is commonsensical. This improves the signal to noise ratio that we confront in our complex operating environments.
One of the clear expectations of the CISO role is that we help our colleagues in the organization prioritize which digital risks warrant attention. At least for our applications, focusing on runtime security that provides deeper insight into how systems are being built and delivered is an elegant, simplified approach to help with this prioritization. When confronted with infinite risk and limited resources, it's imperative that our security programs focus on those areas that effectively move the needle and reduce actual risk. Again, pilfering from Sysdig's site, the value of this runtime approach becomes self-evident in the filtering graphic below.
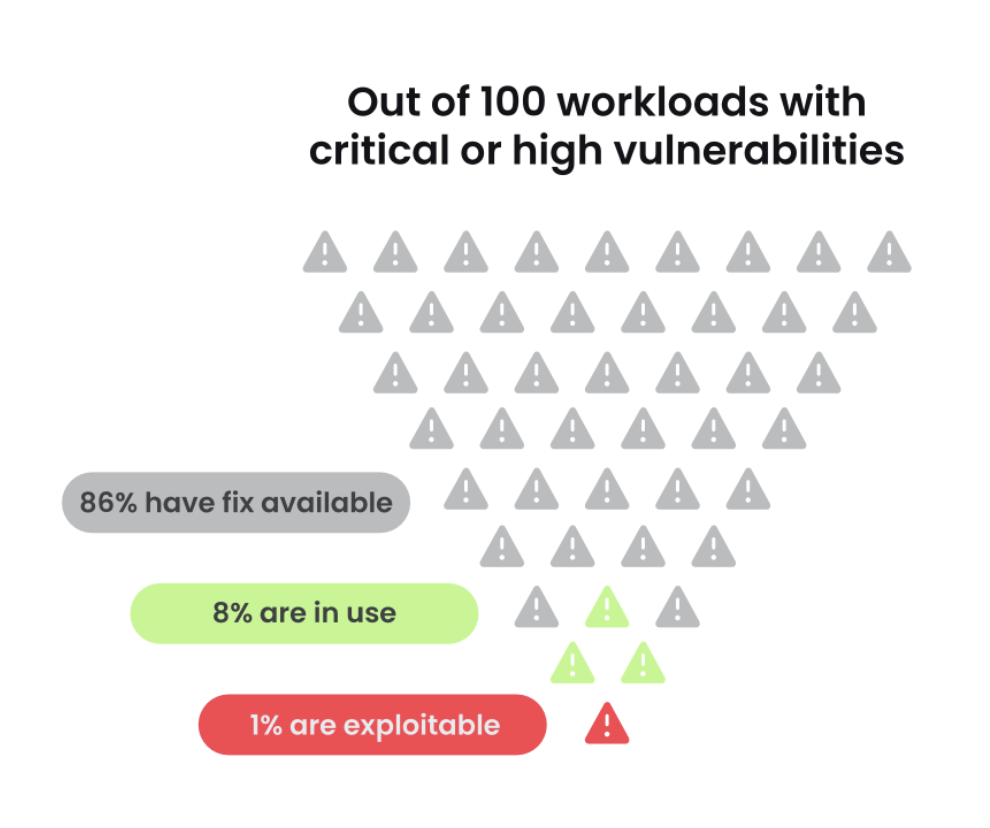
Runtime security is to application security what marginal economics is to the larger field of economics, it's where the action is. For economists, everything happens at the margin. As the two figures above show, the analog holds true for the security of our applications. Runtime is where it's at! This is also where business value is accrued, and the business of business happens. Every business process is supported by an application. Applications have complex operating environments that include code bases, entitlements & permissions, network & infrastructure settings, third-party libraries, microservices, and configuration settings that can and do present vulnerabilities. Application environments are noisy, ever-changing, and distracting from a risk management perspective. Focus on what happens during runtime. This effectively reduces noise while increasing the risk signals that warrant our attention.
Sometimes, elegant solutions catch our profession off guard. The OWASP® Foundation's Application Security Verification Standard (ASVS), as a case in point, does not adequately address runtime security and recommends protection only in the broadest sense. This is akin to the legacy endpoint protection vendors not focusing sufficiently on the living off the land attack techniques of threat actors that ultimately resulted in a new and clearly more effective form of endpoint protection, namely endpoint detection and response (EDR). My hope is that subsequent versions of the ASVS address runtime security techniques in more detail given their clear value to application security.
"My two cents…shifting left should not come at the expense of shield right. These are two sides of the same coin that help our organizations become more resilient when confronted with cyber and other forms of digital risk."
CISOs are well served by focusing on runtime security. Our colleagues within the organization care about their operations, which are supported by the organization's portfolio of applications. By reducing actual, material risks with runtime security, we help the organization become more resilient and secure. Ultimately, that is at the heart of the CISO's role.

About the author
Matt Stamper is a multi-time CISO and the CEO of Executive Advisors Group, where he helps companies build and refine security programs. A former research director and security analyst at Gartner, Matt is the co-author of the CISO Desk Reference Guide, the CISO Desk Reference Guide Executive Primer, and the Data Privacy Program Guide: How to Build a Privacy Program that Inspires Trust.
This post was previously published on LinkedIn.


