Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

In September 2017, the National Institute of Standards and Technology (NIST) released Special Publication (SP) 800-190, Application Container Security Guide. NIST SP 800-190 explains the security concerns associated with container technologies and recommendations for the image details and container runtime security. It provides prescriptive details for various sections including image, registry, orchestrator, container and host OS countermeasures.Given the popularity of Kubernetes, our mission at Sysdig has been to help organizations mitigate security and compliance risks that inhibit their ability to drive Kubernetes and container deployments. Sysdig Secure provides container security and allows your images to adhere to the NIST 800-190 controls.
I. Container image scanning policies for NIST 800-190
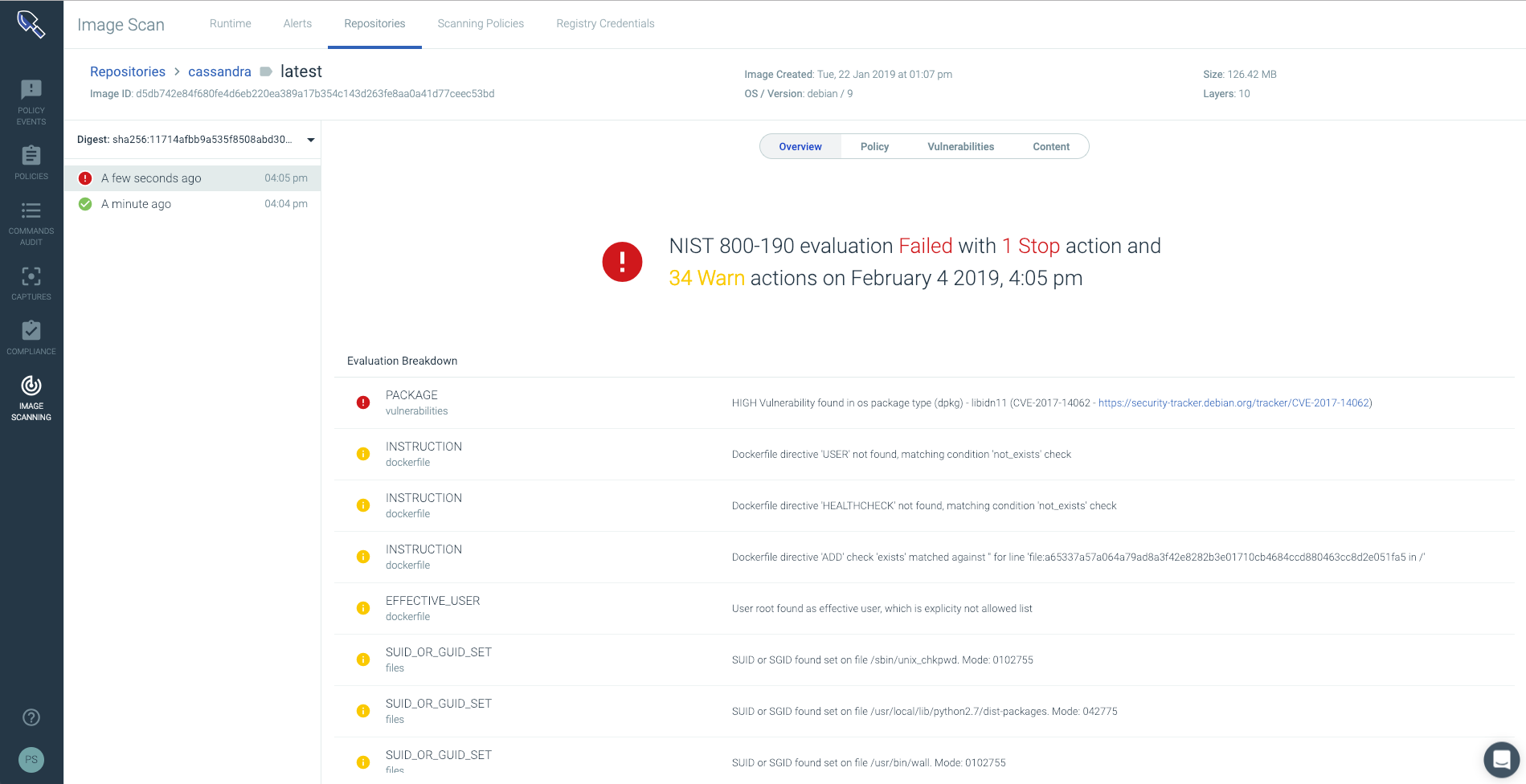
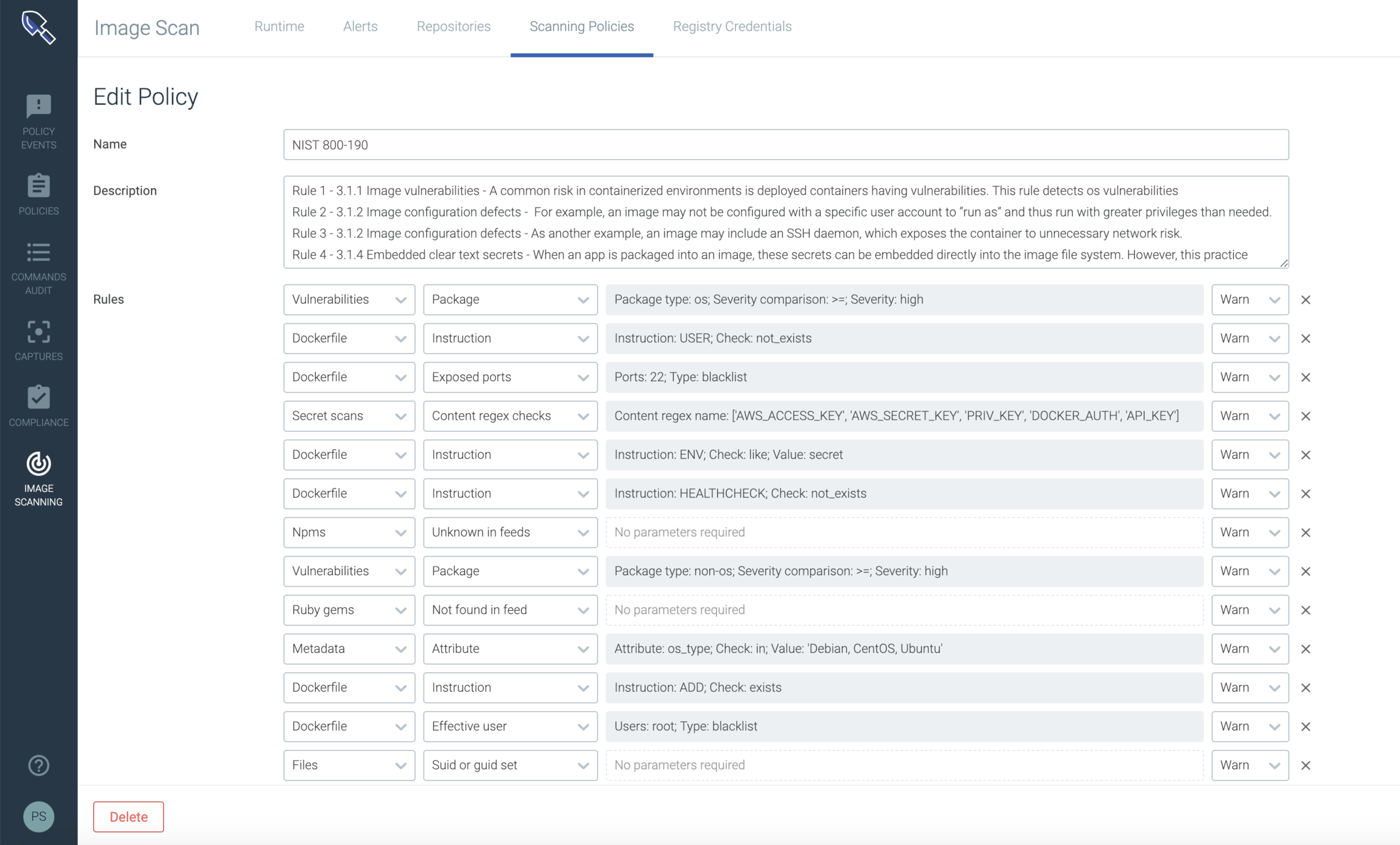
The integration of security into Devops is new to many enterprises but is imperative because the development agility Devops practices provides can make applications vulnerable to compliance violations. The out-of-the-box framework for NIST 800-190 in Sysdig Secure allows customers to enforce Kubernetes and container compliance in their container deployment lifecycle and provides additional checks for container images running in Kubernetes and OpenShift environments. These policies can also be customized to create either "Warn" or "Stop" actions.
II. NIST SP 800-190 compliance in CI/CD pipeline
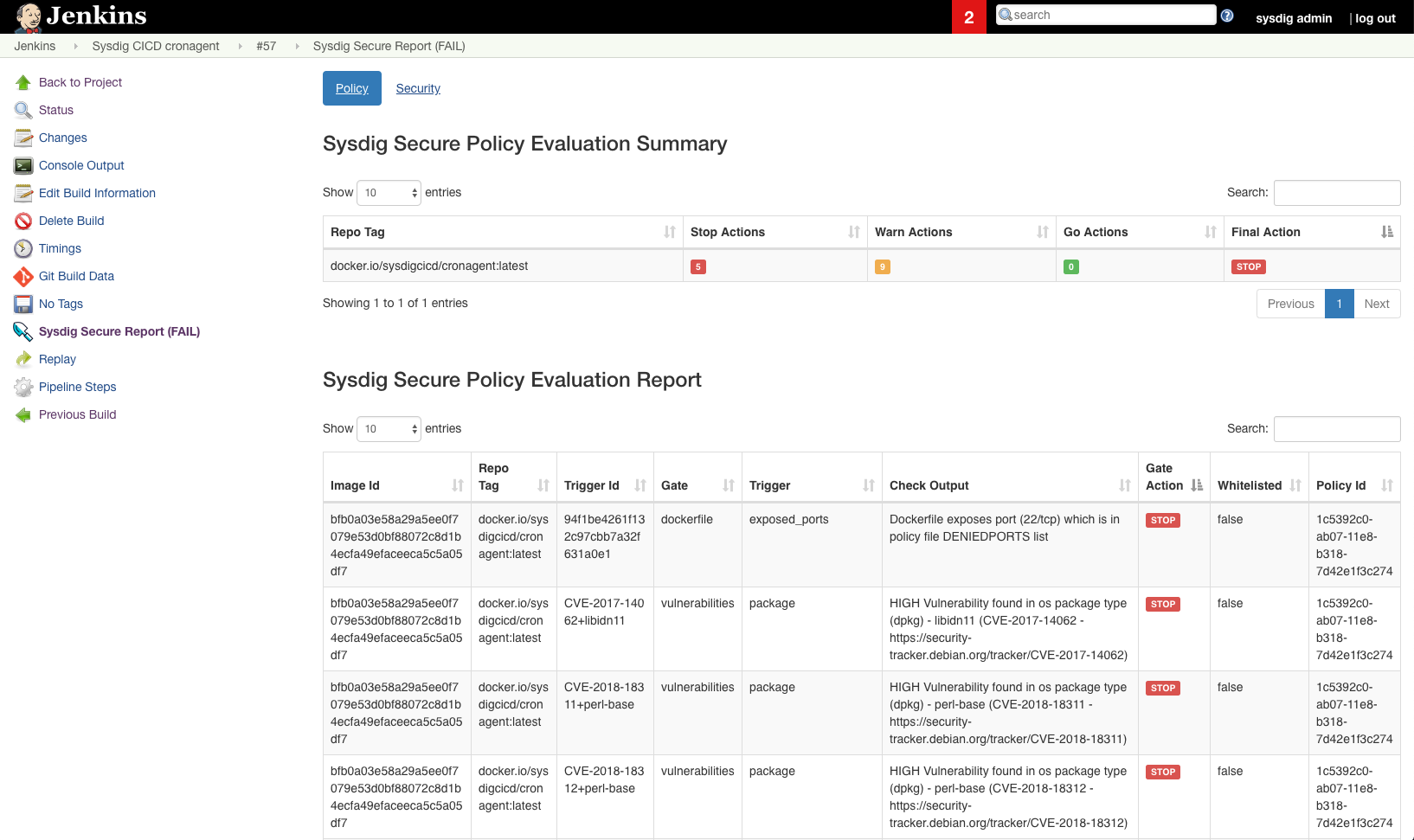
You can ensure compliance to NIST 800-190 by defining image security scanning policy checks prior to deployment. To help you achieve this, Sysdig Secure integrates with CI/CD pipeline tools like Jenkins, Bamboo and many others to scan images prior to being pushed to production or to the container registry.
III. NIST 800-190 compliance reports
In an audit, organizations are asked to prove compliance over a specific time frame. This poses significant challenges in Kubernetes and containerized environments where developers and application owners are constantly deploying new container images, often without a security review. Sysdig Secure enables you to report on your current compliance posture, and also maintains historical snapshots of policy assessments, enabling you to prove compliance assurance for any past time periods as well. Below you can see a NIST 800-190 compliance assurance report being generated:
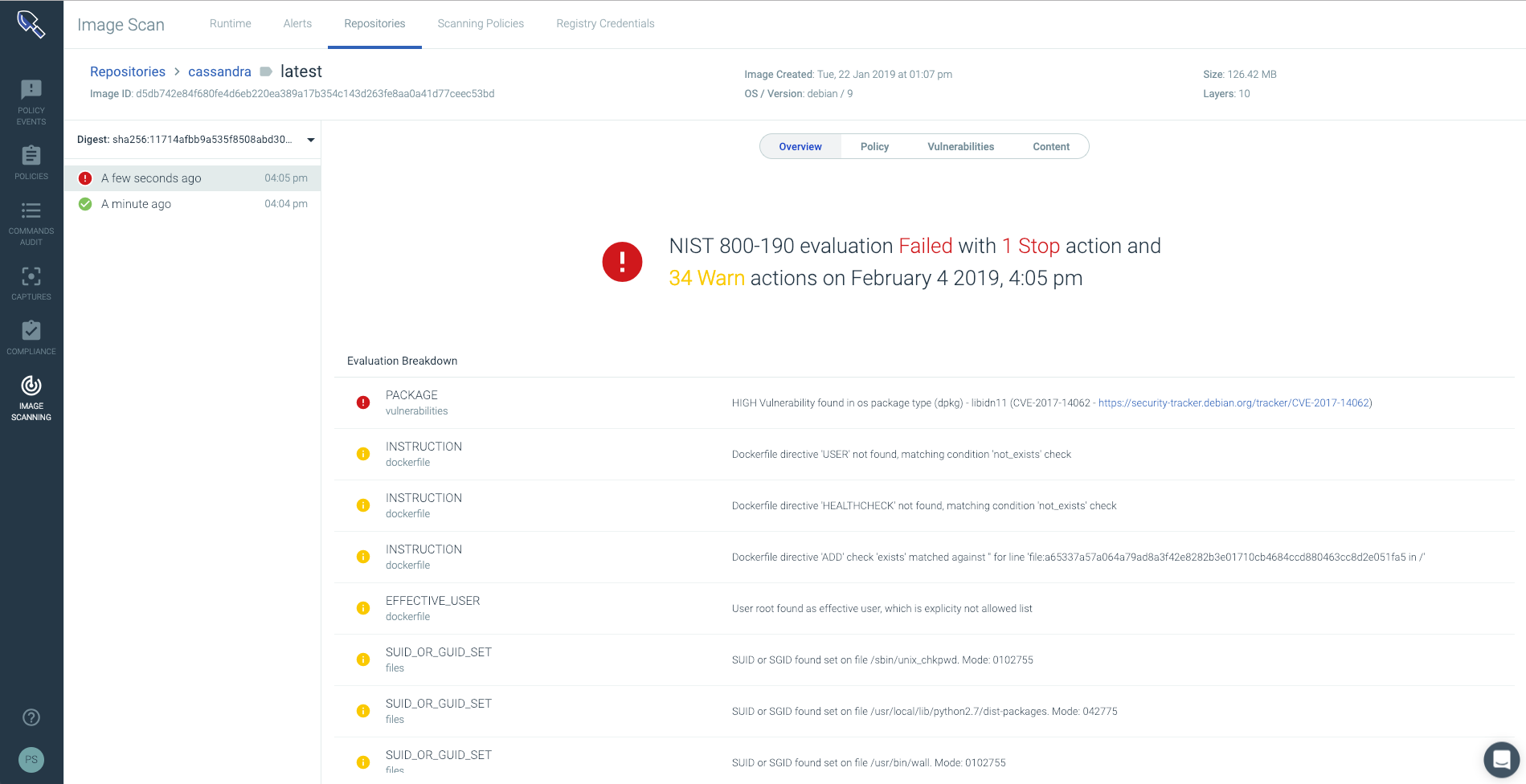
The compliance report provides:
- Visibility into the resources scanned within repositories and registries that you had specified.
- A high-level view of how many images passed and failed the NIST checks based on your user customized NIST scanning policy. This policy can also be leveraged natively in your CICD pipeline such as Jenkins, CircleCI, Bamboo, and others to prevent vulnerable images from ever entering production.
- The specific compliance controls that were violated. You can click on any of the violations to get more information about the vulnerabilities, packages, known CVEs, etc.
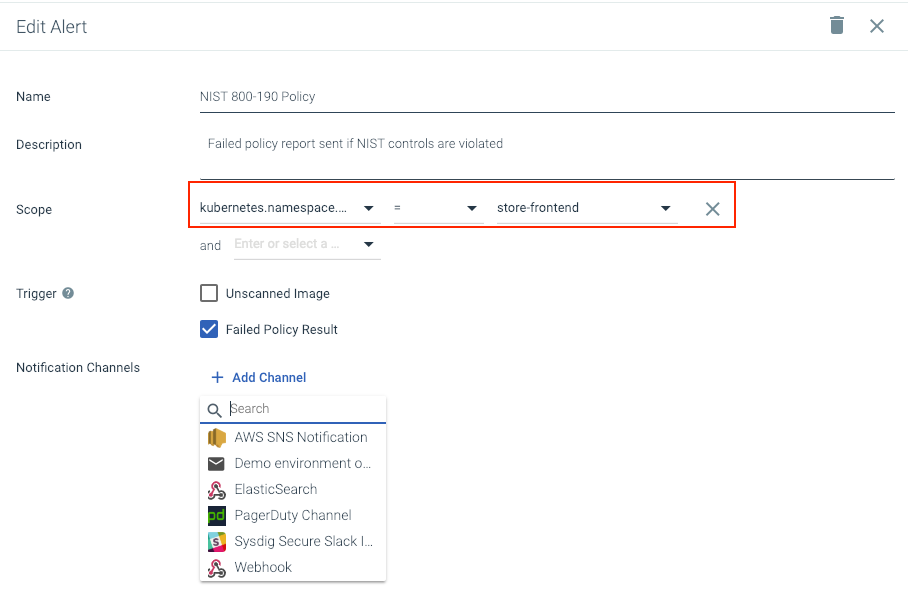
IV. Alert on NIST SP 800-190 policy violations
With Sysdig Secure you can configure flexible alerts to trigger when a NIST 800-190 compliance policy violation is detected. You can set up different notifications by application (scoped down to Kubernetes resources like clusters or namespaces) or by team, so the owner can quickly respond and address it.
Implementing NIST 800-190 application container security guide with Sysdig Secure
Sysdig Secure ensures continuous container compliance automation of the NIST 800-190 standard for images running in your Kubernetes and OpenShift environments across the container lifecycle. As a result, Sysdig Secure users can ensure compliance in their image scanning, Kubernetes and Docker containers, at runtime and during audit.
For more details on how Sysdig provides NIST 800-190 compliance assurance, check out our NIST 800-190 Application Security Checklist here.


