Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

Last year, Sysdig outlined our vision for an AI-driven cloud security assistant. Today, we are excited to announce Sysdig Sage™ for cloud detection and response (CDR), our new release that embodies our vision. Built upon the core principles we introduced, Sysdig Sage offers actionable insights for cloud environments, with a focus on CDR. Sysdig Sage for CDR is the first milestone on the road to making AI assistance pervasive across our CNAPP platform, enabling customers to secure their cloud environments faster.
The 555 Benchmark for Cloud Detection and Response – 5 seconds to detect, 5 minutes to triage, and 5 minutes to respond – sets the standard for operating securely in the cloud. Achieving 555 means being able to detect and respond to cloud attacks faster than attackers can complete them.
With only 5 minutes to perform cloud investigations and block attacks before they are executed, Sysdig Sage for CDR accelerates analysis and investigation, allowing users to prioritize what matters. With Sysdig Sage, users can focus on attack responses rather than spending time connecting the dots or retrieving key information to understand the attack's big picture and impact.
What is Sysdig Sage for CDR?
Sysdig Sage is a generative AI cloud security analyst – an expert that empowers users, letting them ask questions about their runtime events in natural language within Sysdig Secure's Events Feed.
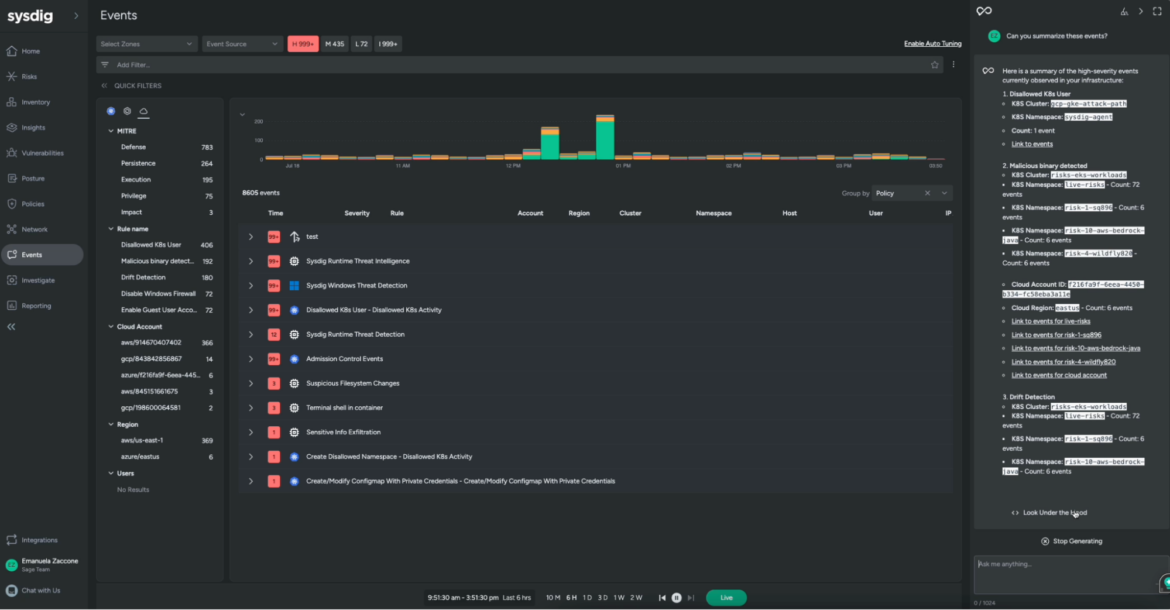
The Events page provides an overview of security events occurring across your infrastructure, allowing you to dive deep into specific details, distinguish false positives, and configure policies – based on open source Falco – to enhance security.
Sysdig Sage elevates these capabilities infusing AI into security analysis operations, delivering:
- Statistics of security events: Review top statistics for runtime security events based on various groupings such as policy name, rule (event type), severity, and more. This will help users streamline the analysis and quickly identify and focus on events that are relevant to the investigation
- Explanation of security events: Sysdig Sage can provide details about runtime events to users and dig deeper into them – for example, to explain the command lines that generated them.
- Suggested next steps: Sysdig Sage for CDR can get behavioral details from sample runtime events to summarize what happened at a broader level and suggest some next steps to fix and remediate the issues. This will help users move faster and immediately take action.
- Context awareness: Sysdig Sage for CDR provides a fully integrated experience. It understands what users are navigating in the Secure UI and can control it, allowing users to quickly jump to the events and information relevant to their investigation.
See Sysdig Sage in action
As someone working in security operations, you might want to easily navigate, filter, and focus on relevant events. When viewing the Sysdig Events feed, you want to be able to understand the events you need to focus on.
You might filter out low and medium-severity events but still have tons of events to process. This is when Sysdig Sage can speed up your work. You are one click away from asking "Can you summarize these events?" Sysdig Sage will understand that you activated these filters in the UI and only focus on high-severity events that occurred in the last 6 hours:
You can then click on "Link to events" to quickly reach the events you want to analyze in the UI and keep the conversation going with a focus on the event you want to look at more closely:
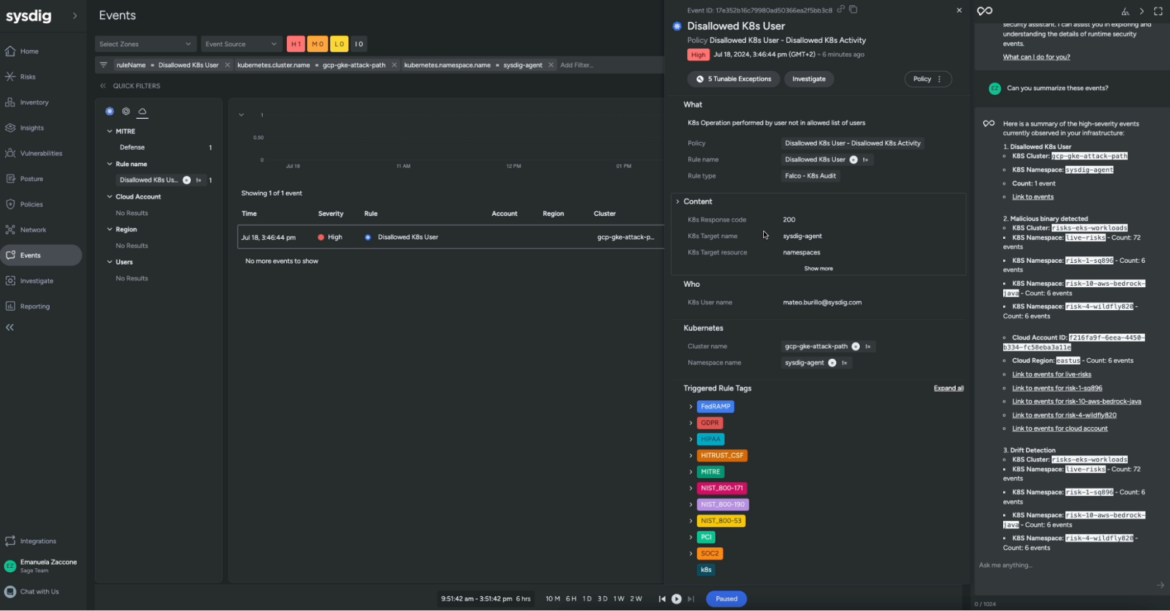
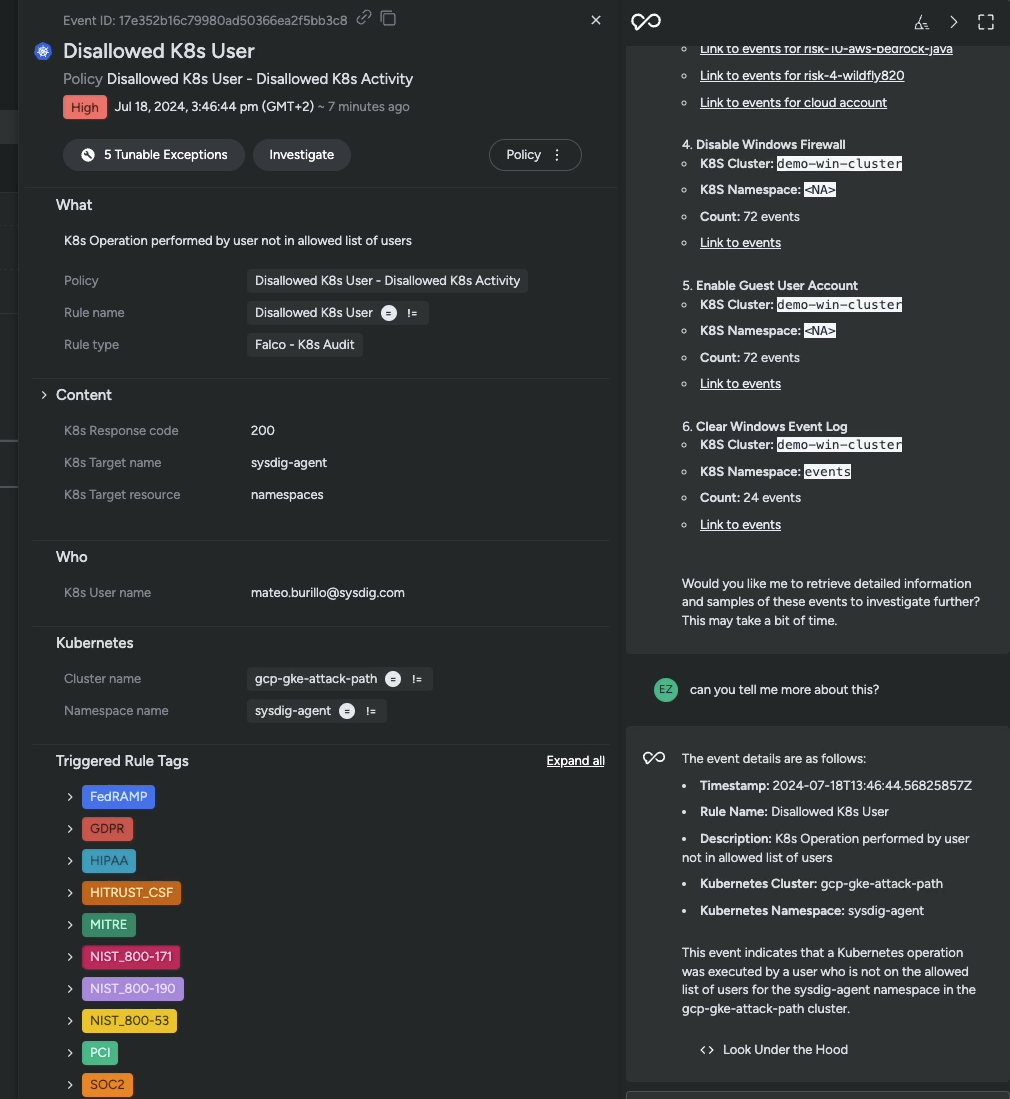
At this point, you might want to better understand why the user was allowed to perform that action and if it represents a threat:
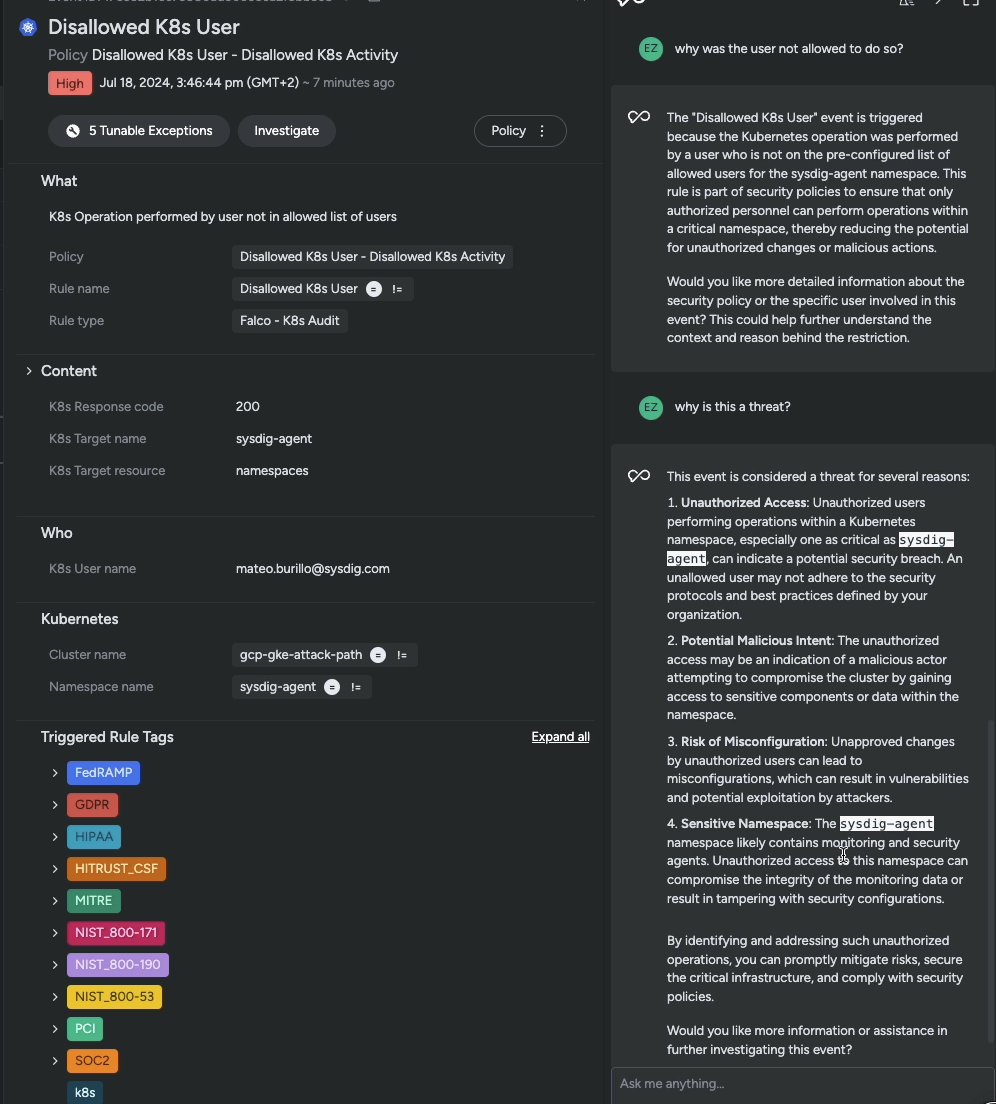
Now that you connected the dots, you will be able to start crafting your remediation strategy:
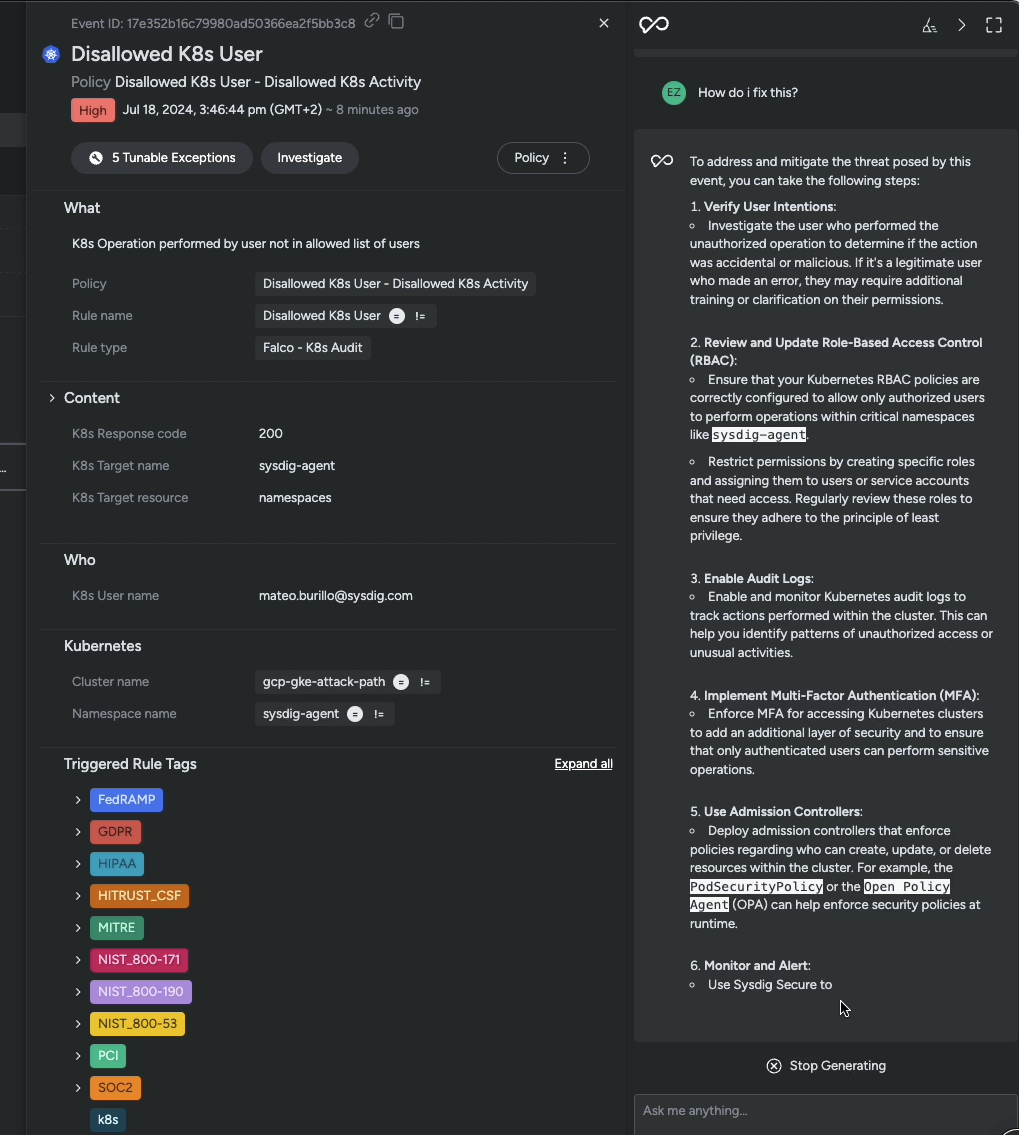
And finally: the big picture. Is the threat you analyzed part of a broader security incident? Let's ask Sysdig Sage!
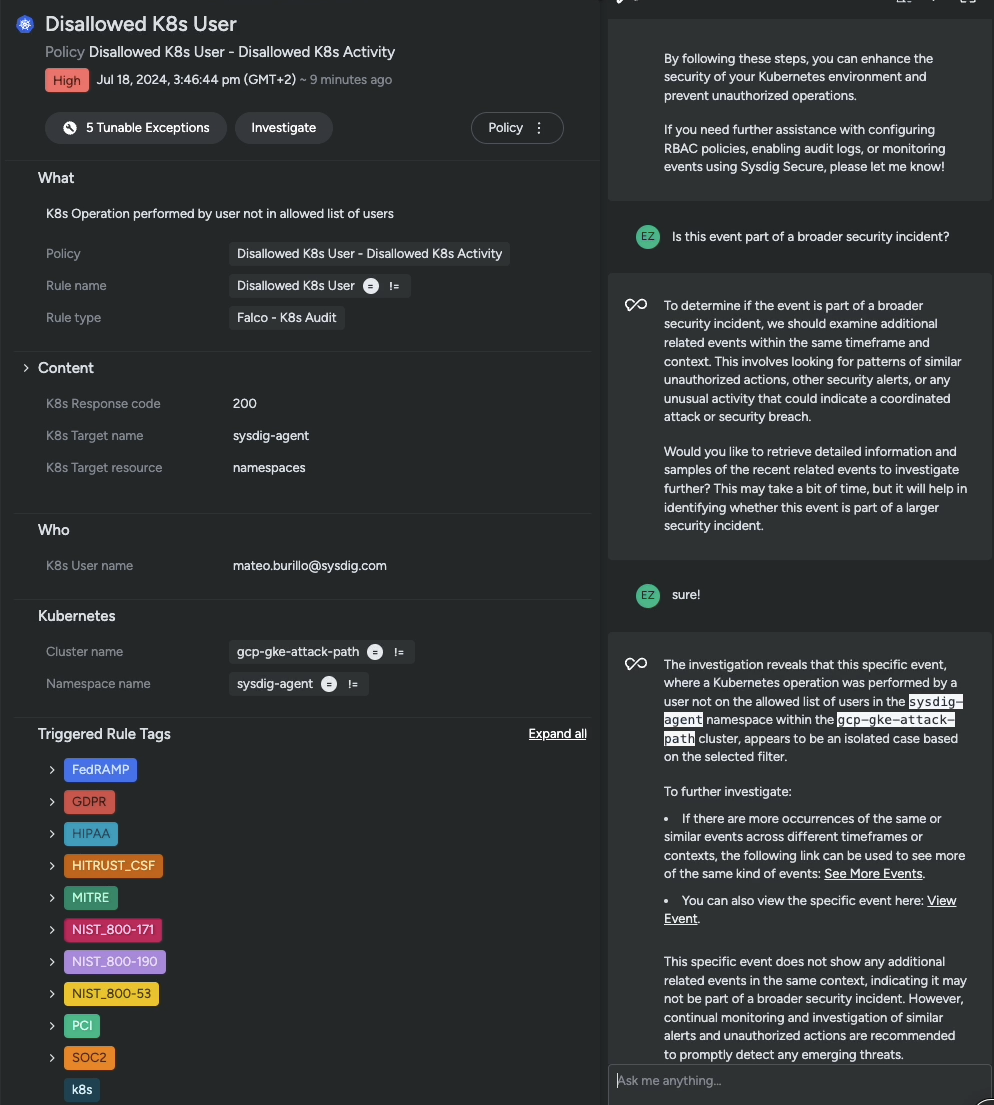
In just a few questions, you were able to refine your analysis, get all the needed information without leaving Sysdig Secure, and get guidance on what steps to take.
Unlock the power of AI for cloud security
Cloud attacks happen fast. Sysdig Sage for CDR is the ultimate secret weapon to equip security teams to achieve the 555 Benchmark for Cloud Detection and Response, quickly make informed decisions, rapidly respond to threats, and save time on the most complex tasks.
With Sysdig Sage you can:
- Supercharge skills: Whether a novice or expert, Sysdig Sage for CDR will help you understand your runtime events.
- Save time: Focus on outcomes, not the analysis.
- Get actionable insights: Know where to start and reduce time to respond – from hours to seconds.
- Collaborate better: Level set knowledge across teams.
By reducing analysis time to just seconds and seamlessly connecting the dots, Sysdig Sage for CDR impacts daily security operations, supercharging CNAPP capabilities with the power of AI.


