Cloud Workload Protection Platform
Prioritize vulnerabilities and detect container threats in seconds
Traditional security tools fail to provide visibility of containerized workloads and create an endless list of alerts. To secure the cloud, you must be able to prioritize vulnerabilities and instantly detect threats.
How Sysdig helps
Container security needs cloud context
Take container security to the next level. Enrich your workload protection with findings across the cloud to prioritize the most significant risks. Get complete visibility and context of threats and vulnerabilities across containers and Kubernetes.
-
Identify the riskiest combinations
It’s not enough to view container threats in isolation. Approach workload security from a risk-centric perspective with multi-domain correlation between containers and cloud to prioritize the most important risks. Uncover hidden attack paths and stop attackers in their tracks.
-
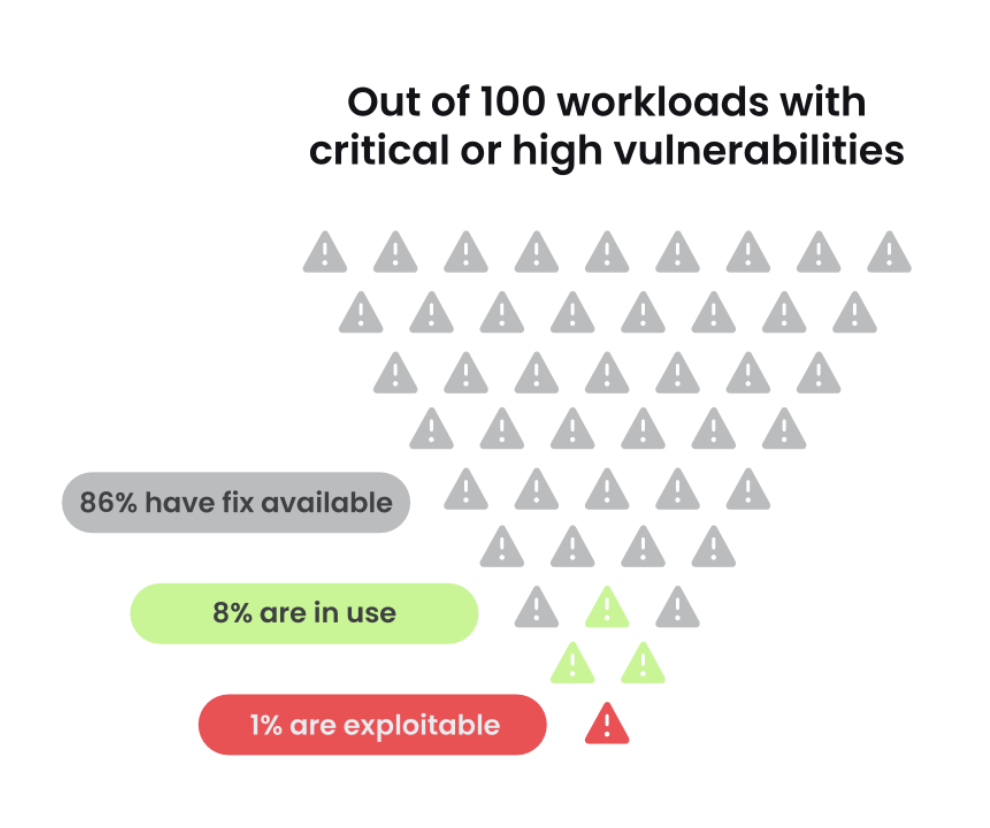
Save time and reduce vulnerability noise
Get the best of both worlds with agent-based and agentless vulnerability scanning. Filter 95% of vulnerability noise by using runtime insights to prioritize vulnerabilities tied to in-use packages. Simplify setup and scanning using an agentless approach to find vulnerabilities across your cloud environment.
-
Detect workload threats in seconds
It only takes 10 minutes to execute an attack in the cloud. With Sysdig, you can detect threats in real time across containers, Kubernetes, and servers. Capture relevant context including interactive commands, system calls, and audit logs to investigate and respond to threats in minutes.

Free resource
Best practices for securing Kubernetes
Kubernetes facilitates the shift to microservices by developers, but introduces complex security challenges often left unaddressed until deployment. Get best practices to ensure that you are taking a proactive approach to cloud-native security.
Numbers don't lie
How CWPP can helpFAQs
A cloud workload protection platform (CWPP) is a cloud security solution that focuses on securing cloud-based workloads across physical servers, virtual machines, containers, and serverless functions. CWPPs primarily focus on what is running on the cloud and protecting those workloads from threats. Some things that a CWPP can help you with: vulnerability management, detection and response, and runtime visibility for containers, Kubernetes, and servers.
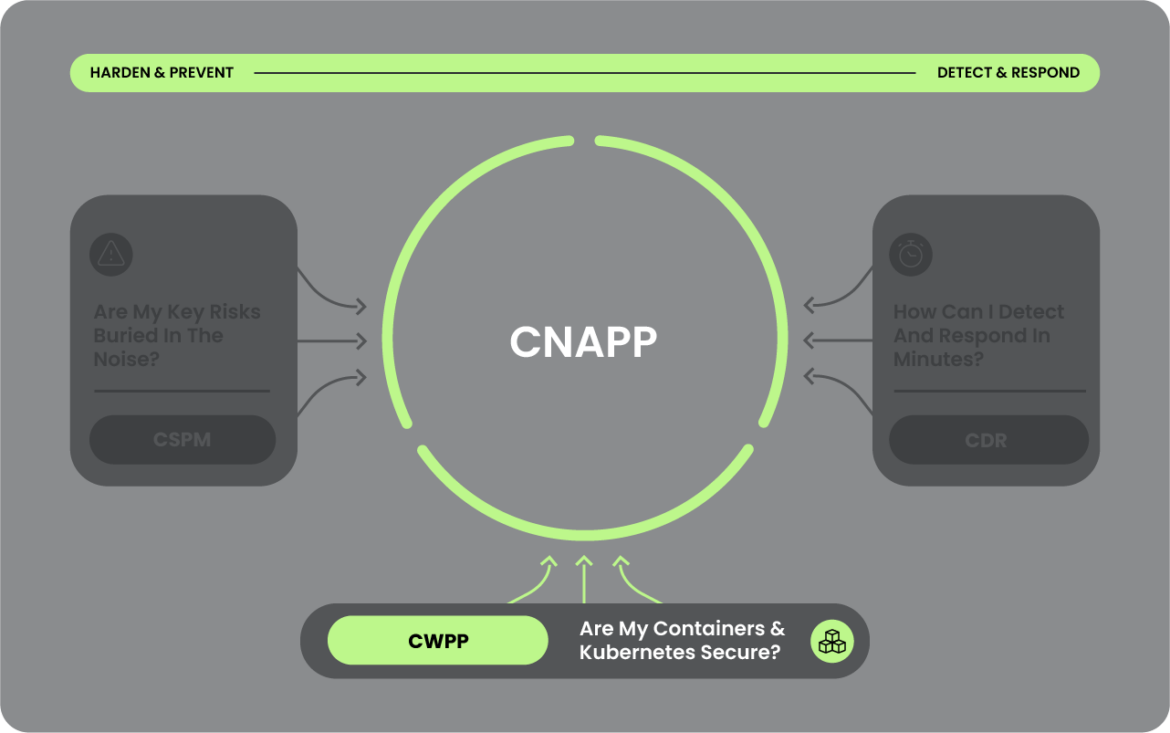
Traditional CSPM solutions focus on preventing attacks to your cloud infrastructure by shoring up weaknesses in security posture. CWPP solutions incorporate both prevention and detection for the workloads running on that infrastructure.
CSPM and CWPP should be consolidated within a cloud-native application protection platform (CNAPP), which eliminates the need for multiple, disparate solutions. By consolidating these capabilities within a single platform, you can bridge the gap between infrastructure security and workload protection. An ideal CNAPP solution should offer correlation of findings and context across workloads and the broader cloud environment.
Prioritize vulnerabilities and detect container threats
Secure containers, Kubernetes and hosts, prioritize vulnerabilities, and protect your AWS Fargate workloads.
Take the Next Step!
See how you can secure every second in the cloud.