Fix Cloud Misconfigurations and Improve Security Posture
In the cloud, things move fast. You need to move even faster to eliminate blindspots and vulnerable entry points before attackers exploit them. 10 minutes is all it takes to initiate an attack in the cloud. When every moment counts, secure every second.
Stay secure, stay compliant.
Stay on top of your cloud security posture. Sysdig CSPM continuously monitors for misconfigurations, exposures and excessive granted privileges, aggregates the most impactful security and compliance issues, and suggests remediations, saving you time and effort.
Prioritize risk based on impact
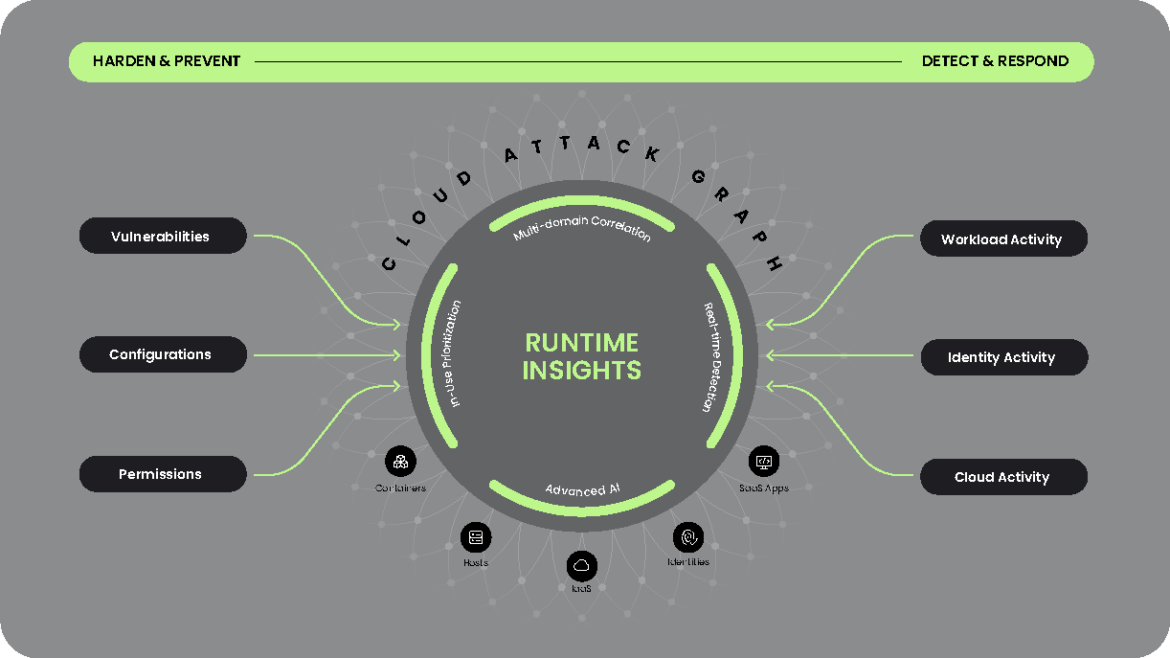
Runtime insights spotlights your most critical risks, such as in-use vulnerabilities and permissions, and runtime events. Don’t waste time trying to prioritize everything. Focus on fixing what matters and strengthening your cloud defense.
Eliminate identity misconfigurations
Get a full view of identities and permission policies across your cloud environment. Quickly see inactive users and excessive permissions, optimize policies to enforce least-privilege access, and mitigate the security risk of misused privilege. Meet specific IAM requirements for standards including PCI, SOC2, FedRamp and ISO 27001.
Fix security issues in seconds
Reduce cloud risk with minimal effort and maximum impact. Remediate issues with auto-generated suggestions to Infrastructure-as-Code artifacts that fix cloud and Kubernetes resource misconfigurations with a single click – freeing up your developers to get back to revenue-generating work.
Take control of risk with a Cloud-Native Application Protection Platform
Cloud Security Posture and Permission Management
Flag misconfigurations and automate their remediation. Continuously track security and compliance progress.
Take the Next Step!
See how you can secure every second in the cloud.