Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

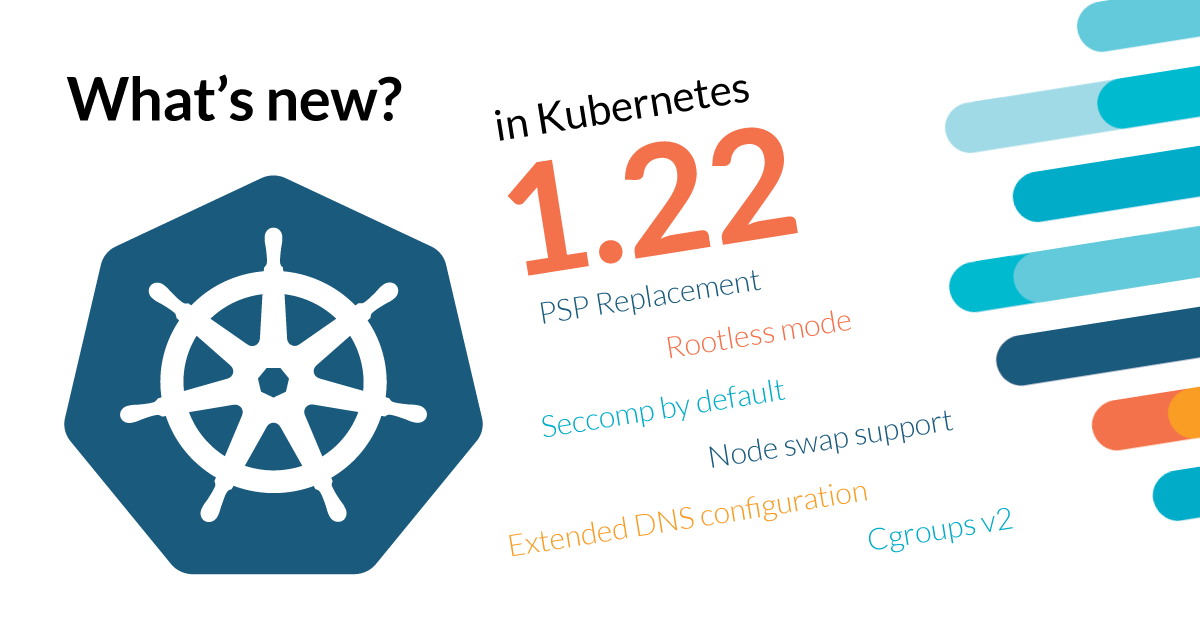
Kubernetes 1.22 is about to be released, and it comes packed with novelties! Where do we begin?\r\r
\rThis release brings 56 enhancements, an increase from 50 in Kubernetes 1.21 and 43 in Kubernetes 1.20. Of those 56 enhancements, 13 are graduating to Stable, a whopping 24 are existing features that keep improving, and 16 are coming with innovative changes. PodSecurityPolicy (PSP) is deprecated, replaced by Pod Security Standards (PSS). Cgroups v2 support is adding new ways to manage system resources. And there are many more. Read on!
So, which are the highlights?
RuntimeClass is now ready for production. It was graduated to stable in Kubernetes 1.14, and now it's allowing multiple runtime implementations on the same cluster.
Furthermore, with the new RuntimeClass, there is a chance to define cost and overhead properties to help ensure pod scheduling and resource metrics are accurate.
Pod Security Standards, in contrast to PSP, is built as a native Kubernetes module and doesn't require any plugin management. It simplifies security policies management across the cluster, without the complexity of PSP.
This is a relief for many DevSecOps and Kubernetes administrators since PSP was quite complex. It's a control mechanism that requires specific expertise and a thorough understanding of Kubernetes security.
Additionally, Cgroups v2 support brings improved resource management and is fully supported as a Stable feature. It means pods can better manage system resources like memory and CPU. This feature is especially important for resource-constrained environments.
What are the main topics discussed in this article?
We'll dive into the following topics:
– Pod Security Standards (PSS) and PSP deprecation
– RuntimeClass improvements
– Cgroups v2 support
– Kubelet Credential Provider and CSI Driver Node Publish Secrets
– Control Plane improvements
– API deprecations and removals
– Serverless Kubernetes
– And many more enhancements
Pod Security Standards (PSS) vs PSP, why should we care?
Pod Security Policy has been a Deprecated since Kubernetes 1.21, and it will be fully removed in Kubernetes 1.25. It's crucial to plan your strategy to transition from PSP to PSS before the removal date.
Kubernetes has announced that Pod Security Standards is the replacement for Pod Security Policies. It's simpler, easier to use, and less complex than its predecessor. Additionally, it is built and distributed as a native Kubernetes module.
Instead of using a plugin system, PSS is built into the Kubernetes core and uses labels and admission control to enforce pod security standards. It's a much cleaner and simpler approach than the plugin architecture of PSP.
PSS follows a tiered approach with three different levels of restrictions:
1- Restricted: Heavily restricted policy, following the most up-to-date best practices aimed at enforcing the current best practices for pod hardening.
2- Baseline: Minimal restrictions, preventing known privilege escalations.
3- Unrestricted: The default policy with no restrictions.
Check out our dedicated guide to Pod Security Standards if you want to learn more about this feature.
RuntimeClass – for those that seek customization
Runtime classes are a relatively new feature in Kubernetes that allow you to specify a container runtime implementation per pod.
Before RuntimeClass, you had only one runtime available for the entire cluster. Now, with RuntimeClass, you can specify which runtime to use for each pod. For example, you can have Kata Containers for high-security workloads and runc (the default) for less critical workloads.
In Kubernetes 1.22, RuntimeClass includes new fields for cost and overhead. The overhead field defines the resources reserved by the runtime, which is especially useful when using sandbox runtimes that require additional resources.
Cgroups v2 – resource control
Cgroups v2 is a new interface to the Linux kernel’s cgroup implementation. It’s a single unified hierarchy instead of the multiple hierarchies of Cgroups v1.
Cgroups v2 support in Kubernetes 1.22 is now stable and production-ready. The feature helps with improved resource management and provides a cleaner interface to resource control features.
A Cgroups v2 enabled system uses a single /sys/fs/cgroup mount point instead of the multiple mount points of Cgroups v1. This simplifies resource management and makes it easier to understand the resource usage of your pods.
API deprecations and removals
As Kubernetes continues to evolve, some APIs are deprecated and eventually removed. In Kubernetes 1.22, the following APIs are being removed:
API v1beta1 for most authorization resources have been removed:
- authorization.k8s.io/v1beta1
- autoscaling.k8s.io/v1beta1
- authentication.k8s.io/v1beta1
- batch.k8s.io/v1beta1
- certificates.k8s.io/v1beta1
- coordination.k8s.io/v1beta1
- discovery.k8s.io/v1beta1
- networking.k8s.io/v1beta1
- policy.k8s.io/v1beta1
- rbac.authorization.k8s.io/v1beta1
- scheduling.k8s.io/v1beta1
- storage.k8s.io/v1beta1
Control Plane improvements
1- Kubelet Credential Provider now can be used to rotate credentials dynamically. It was in alpha since Kubernetes 1.20 and is now in beta. The Credential Provider will manage image pull secrets, which can be rotated regularly.
2- CSI Driver Node Publish Secrets allows CSI drivers to receive secrets at mount time. This is useful for scenarios where the driver needs a secret to complete the mount operation, such as mounting NFS shares with credentials or iSCSI with authentication information.
3- Windows support for privileged containers is now supported as alpha in Kubernetes 1.22.
4- Reloader Improvements lets you define StatefulSets that can be updated with minimal disruption. The new feature allows the control plane to request nodes to reload the node-local kubelet configuration.
5- Job Tracking API allows for more efficient job tracking. It was in alpha since Kubernetes 1.20 and is now in beta.
Apiserver and kubelet changes
6- Deprecation of Legacy Service Account Fields suggests the use of the serviceAccountName and automountServiceAccountToken fields instead of using serviceAccount and automountServiceAccountToken fields.
7- Kubelet Config API version changes from kubelet.config.k8s.io/v1alpha1 to kubelet.config.k8s.io/v1beta1.
8- Preemption Improvements adds new fields to the PreemptionPolicy to configure pod preemption behavior. This allows fine-grained control over preemption in your cluster.
Serverless Kubernetes
The definition of Serverless Computing has become increasingly blurred over the last few years. Kubernetes is evolving rapidly to support new workload patterns and execution models.
For example, Knative is a popular open-source framework that simplifies the deployment of serverless workloads on Kubernetes. It abstracts away the complexity of managing pods and services, allowing developers to focus on writing code.
Storage improvements
1- CSI Migration is a major effort to move all in-tree storage plugins to out-of-tree CSI drivers. In Kubernetes 1.22, Azure and GCP providers are graduating the CSI drivers to stable, meaning that all in-tree drivers are being deprecated.
2- Volume Expansion for StatefulSets is now generally available, allowing StatefulSet volumes to be expanded without deleting the pods.
3- Cross Namespace Pod Disruption Budgets is a new feature that allows Pod Disruption Budgets to be defined per application and applied across namespaces.
Networking improvements
1- IPv6 support for Services and 2- DualStack support (both IPv4 and IPv6) on the same cluster. This allows you to run dual-stack cluster deployments to support both protocols.
3- Service topology is now generally available, which allows for improved traffic management across topology zones.
4- EndpointSlices improvements include support for a Service with thousands of endpoints.
Metrics and observability improvements
Finally, Kubernetes 1.22 brings enhancements for observability. For example, Kubernetes now supports Prometheus-style metrics instead of the older legacy custom metrics.
What's the catch? Is there any reason to worry?
API deprecations are one of the topics to take seriously. Kubernetes 1.22 removes many v1beta1 APIs that were still in use by applications and operators. Operators and developers will need to update their code to the stable v1 APIs.
Summary
Kubernetes 1.22 is a big release that moves several features to stable and adds many new capabilities. Let's recap the major points:
- Pod Security Standards (PSS) is the replacement for Pod Security Policy, and PSP is deprecated (will be removed in 1.25)
- RuntimeClass now includes cost and overhead fields to better represent the resource impact of sandboxed runtimes
- Cgroups v2 is now stable
- Kubelet Credential Provider is now in beta
- CSI Drivers for Azure and GCP are now stable, deprecating in-tree storage plugins
- IPv6 support is now generally available
- Service topology is now generally available
- Serverless computing support and frameworks like Knative are becoming production-ready
Kubernetes 1.22 is a solid release with many important updates and improvements. The transition from PSP to PSS is essential for all users running on Kubernetes 1.22 or later. Additionally, be sure to update your applications to use stable APIs to avoid deprecation and removal issues in future Kubernetes versions.
Are you getting ready to upgrade to Kubernetes 1.22? Would you like to learn more about Kubernetes RBAC to better understand how to secure your cluster? Check out our Kubernetes security learning center to find more insights about container and Kubernetes security.


