Security for Virtual Machines and Hosts
Get a single view of risk across VMs and Hosts
Trusted at Cloud Scale


Confidently Secure VMs and Hosts
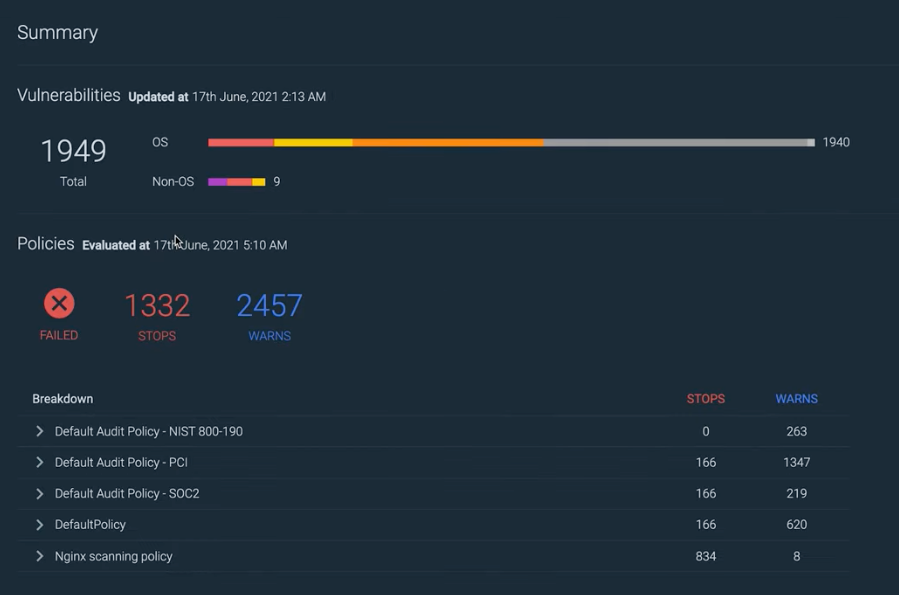
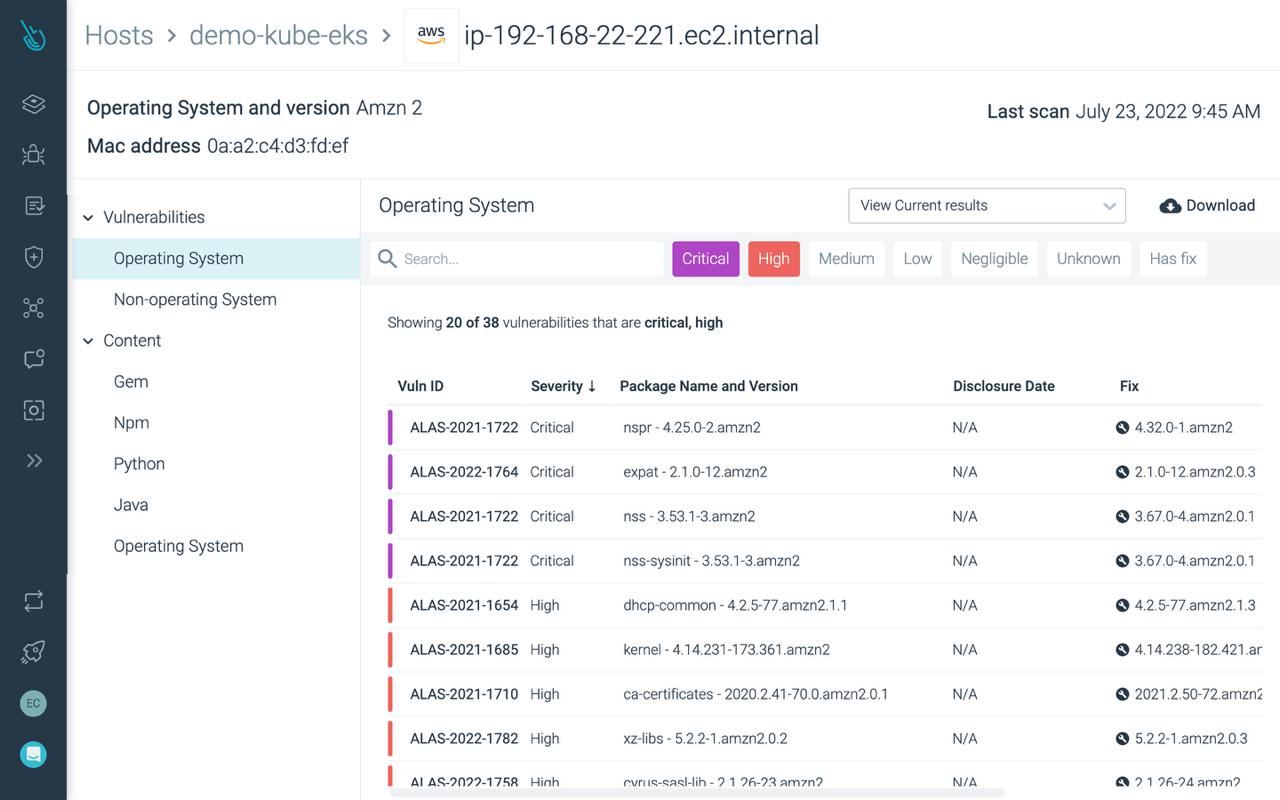
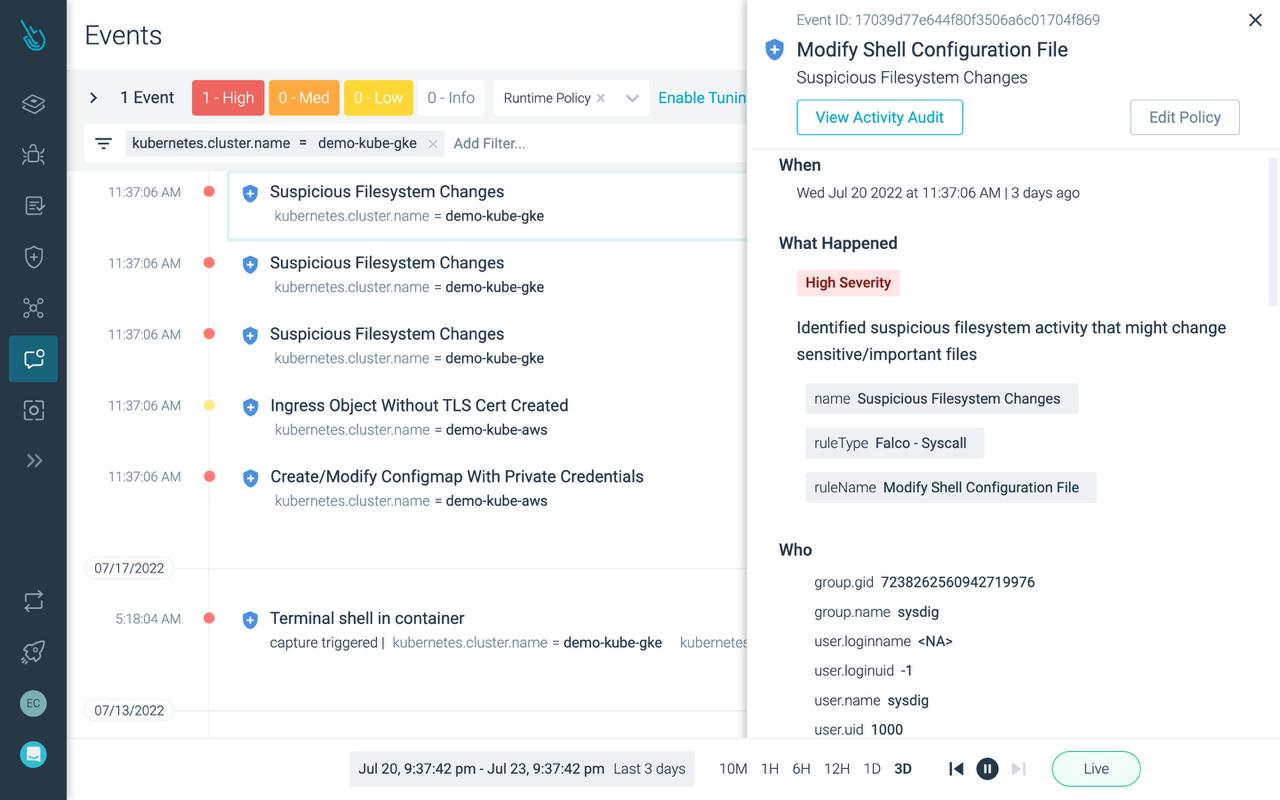
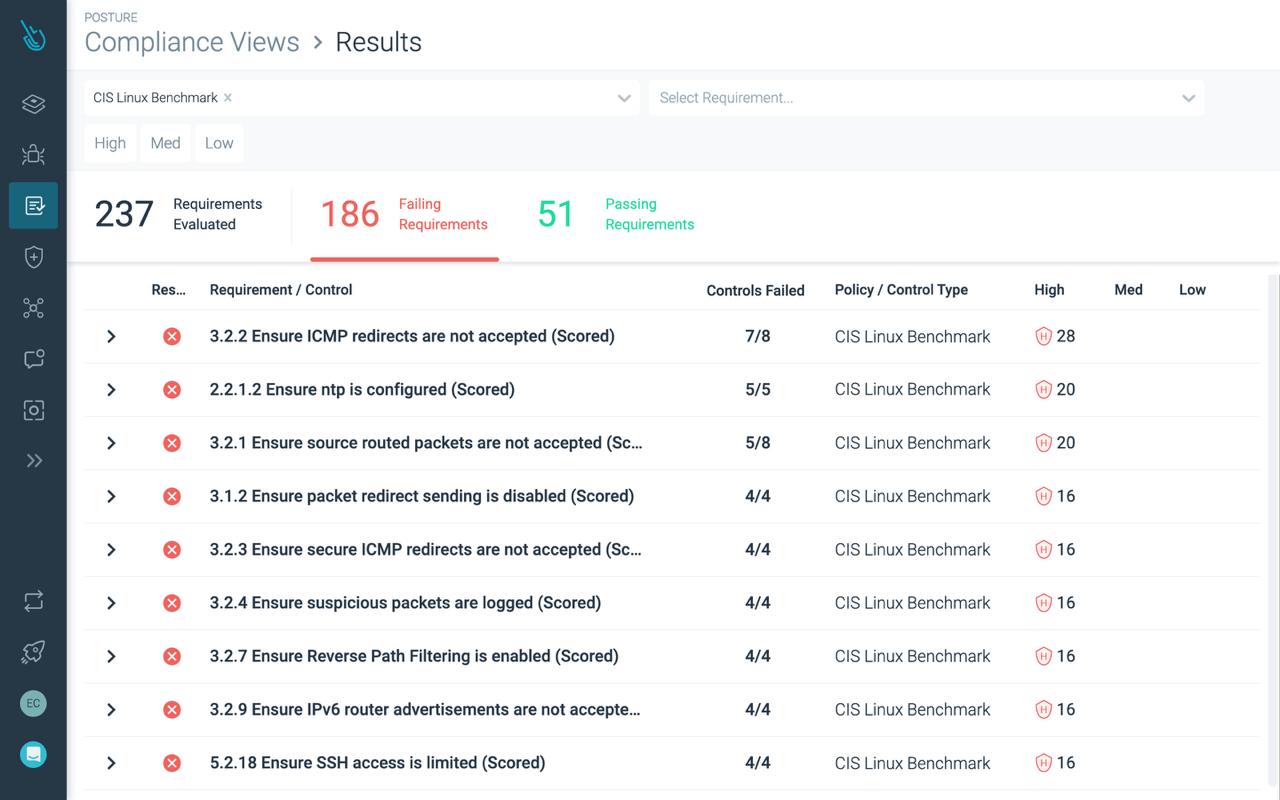
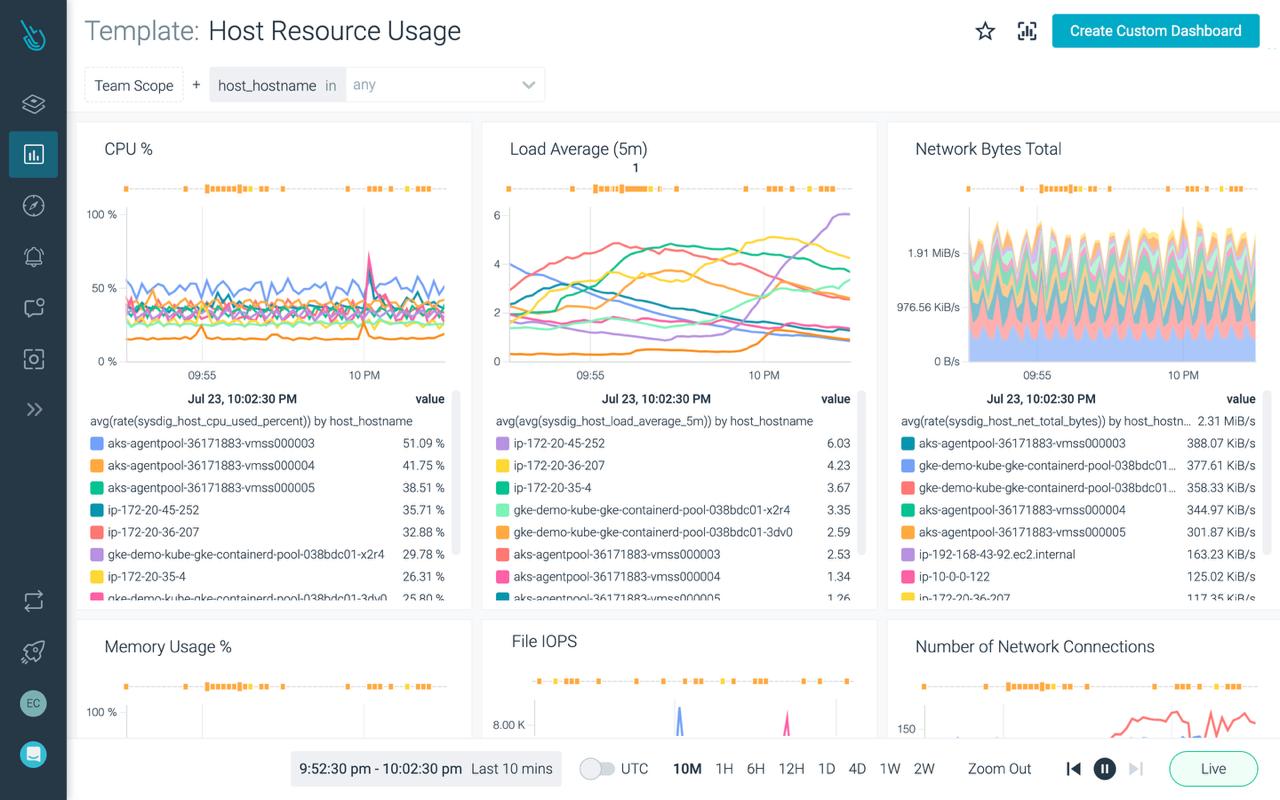
Sysdig gives you real-time visibility at scale to address risk across VMs and hosts, eliminating security blind spots. Find and prioritize software vulnerabilities, detect and respond to threats, and manage configurations and compliance.
Security and Monitoring Use Cases
featured resources