Serverless Security from Source to Run
Get a single view of risk for serverless cloud computing.
Trusted at Cloud Scale


Confidently Run Serverless Workloads
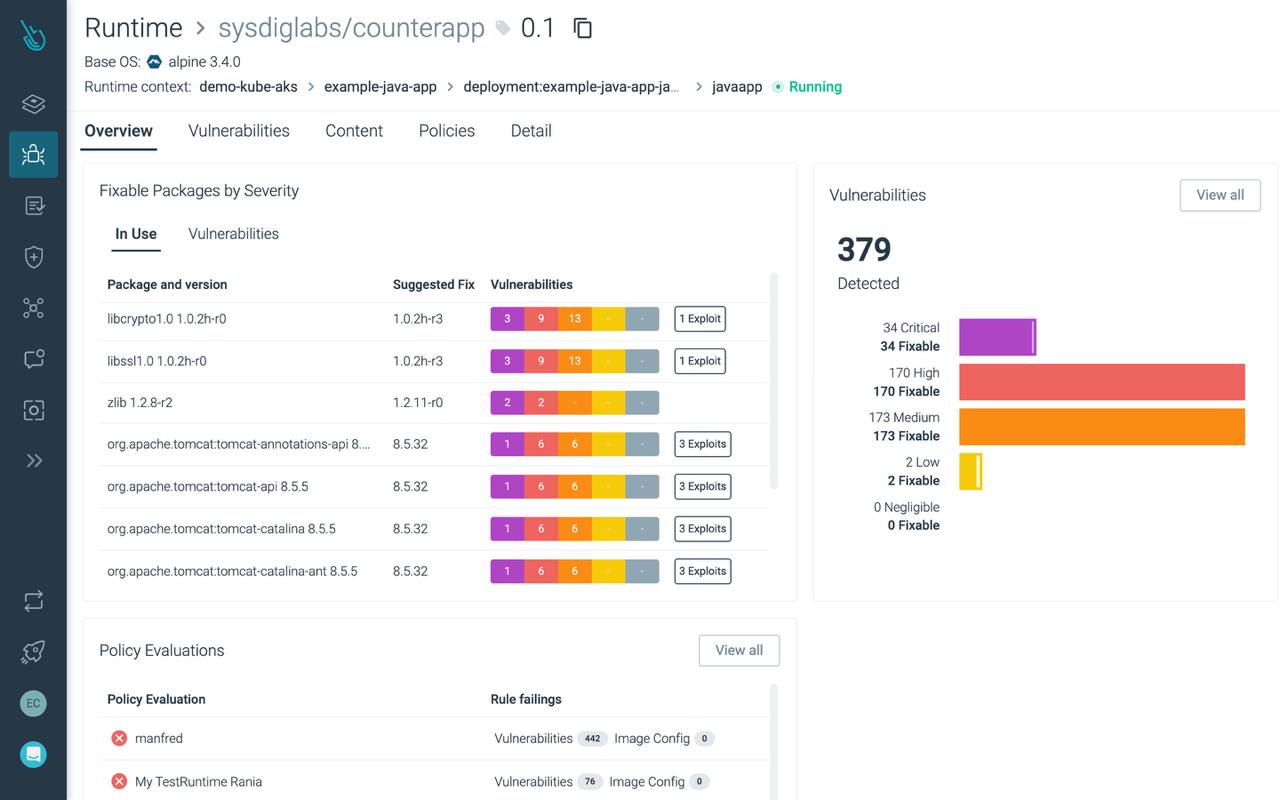
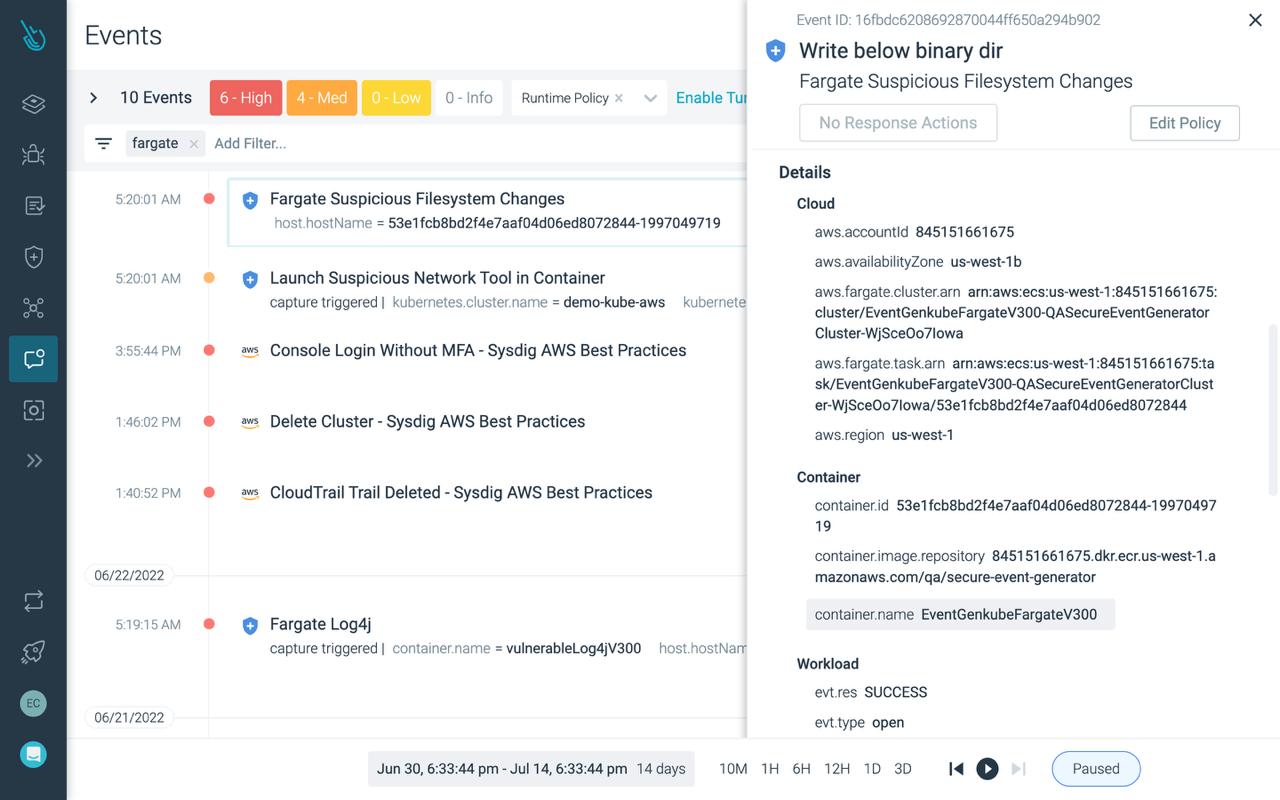
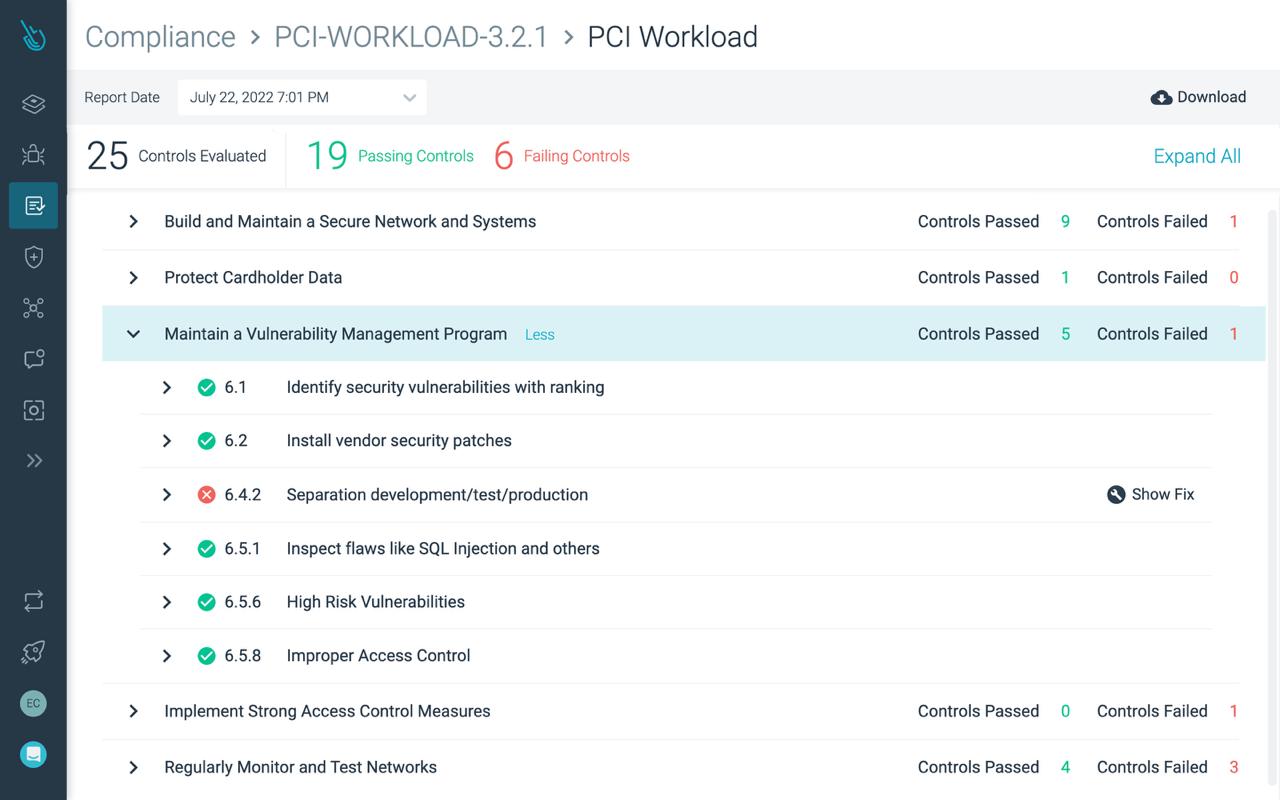
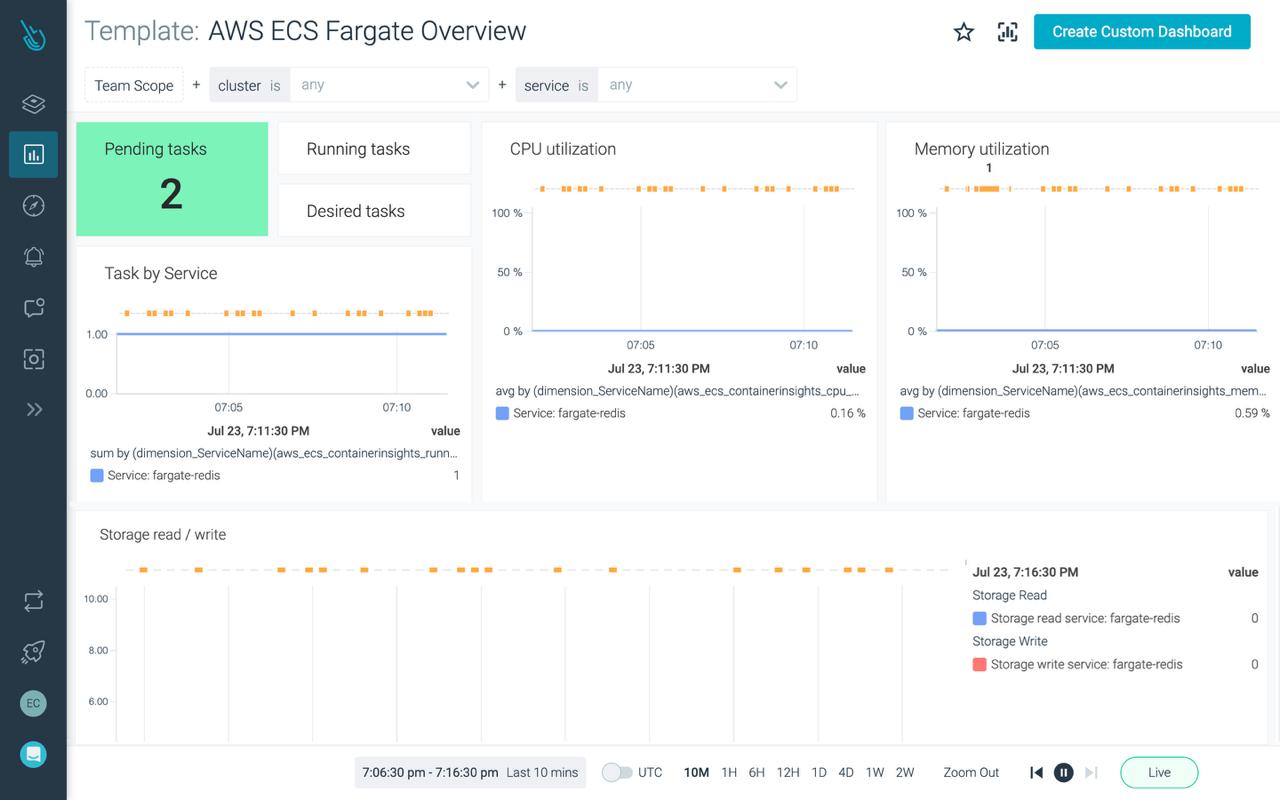
Serverless computing frees you to focus on apps instead of infrastructure but can leave you blind to threats. Sysdig unified cloud and container security eliminates security blind spots with serverless solutions like AWS Fargate, Microsoft Azure Container Apps, and Google Cloud Run.
Serverless Security and Monitoring Use Cases
Integrations
Take advantage of our integrations with serverless services like AWS Fargate, AWS Lambda, and Google Cloud Run for a single view of risk from source to run with no blind spots, no guesswork, and no black boxes.

Monitoring AWS Fargate with Prometheus and Sysdig
David de Torres Huerta
|
June 9, 2020
Monitoring AWS Fargate with Prometheus and Sysdig

Monitoring AWS Lambda with Prometheus and Sysdig
David de Torres Huerta
|
July 14, 2020
Monitoring AWS Lambda with Prometheus and Sysdig

Securing Google Cloud Run serverless workloads
Mateo Burillo
|
November 14, 2019
Securing Google Cloud Run serverless workloads
company name
year
“Big Quote Moment. Lorem ipsum dolor sit amet consectetur. Orci in ut tellus id eu id vitae nulla. Turpis id tellus nisl ultrices vulputate malesuada eu. Vitae commodo in in egestas auctor nulla. Eleifend et integer ultrices tellus. Lacus a tellus egestas molestie in urna. Aliquam risus vulputate at ut.”
featured resources