Discover how to automate AWS Fargate image scanning directly in your AWS environment and block vulnerabilities from reaching production, among other threats.
AWS Fargate and ECS allow you to deploy containerized workloads quickly. Fargate is even more convenient, as you don’t have to take care of the infrastructure. Those services are so convenient that many people leave them unattended, risking exposure to vulnerabilities inside their containers that can exfiltrate secrets, compromise business data, impact performance, and increase their AWS costs.
For example, think of some credentials mistakenly included in an image, later deployed on Fargate. They will be exposed to anyone with access to the image (think on the repository), or to the Fargate service.
Consider a known vulnerability. Imagine you deploy a Fargate task to manage your API, and that it uses an old HTTP library version that ignores the setting to limit a request size. That could be catastrophic! Say you expect requests no bigger than 1MB, but a malicious actor exploits this vulnerability to send requests as big as 80GB. This will absolutely take a toll on your AWS bill and might cause your service to throttle.
Those are serious threats.
You might be reluctant to implement further security checks, thinking they will take away the same flexibility you were looking for when you decided to use Fargate on ECS.
In this article, you will learn how image scanning can provide the security insights you need without affecting the level of flexibility you desire.

In particular, we’ll guide you on how to implement ECS Fargate image scanning with Sysdig Secure. The resulting solution will automatically scan any container image instance that is executed, and will warn you with reports about any vulnerabilities or misconfigurations in your workload. It will do this without leaving your AWS workflow, and without data leaving your AWS infrastructure.
Introduction to Fargate and ECS
AWS Fargate is a serverless compute engine for containers that works with both Amazon Elastic Container Service (ECS) and Amazon Elastic Kubernetes Service (EKS). It allocates the right amount of compute resources, eliminating the need to choose instance types and scaling cluster capacity. With Fargate, you pay for the minimum resources required to run your containers.
Amazon Elastic Container Service (ECS) is a fully managed container orchestration service. Because ECS is a foundational pillar for key Amazon services, it natively integrates with other AWS services.
A while ago, we also covered Amazon Elastic Kubernetes Service (EKS) security.
Image scanning basics
An image scanner inspects a container’s content to detect threats like the ones we introduced earlier. You can implement image scanning best practices on several phases of your DevOps pipeline, blocking threats before they are deployed into production, and without adding extra overhead.
You can define image scanning policies to validate a container’s content against vulnerability databases, and search for misconfigurations like running as a privileged user, unnecessary open ports, or leaked credentials.
When it comes to where the scan takes place, image scanners can take two approaches.
Traditionally, image scanners are executed on a separate backend. In this variant, the scanner needs to retrieve container images from a registry. This implies that you need to publish every image on a registry accessible to the scanner backend. If your image scanner is a SaaS solution, there might be some security implications you’ll have to address.
A more advanced approach is inline scanning where the scan is performed in your own infrastructure, locally to where the container image already is. In this approach, only some metadata is sent to the backend.
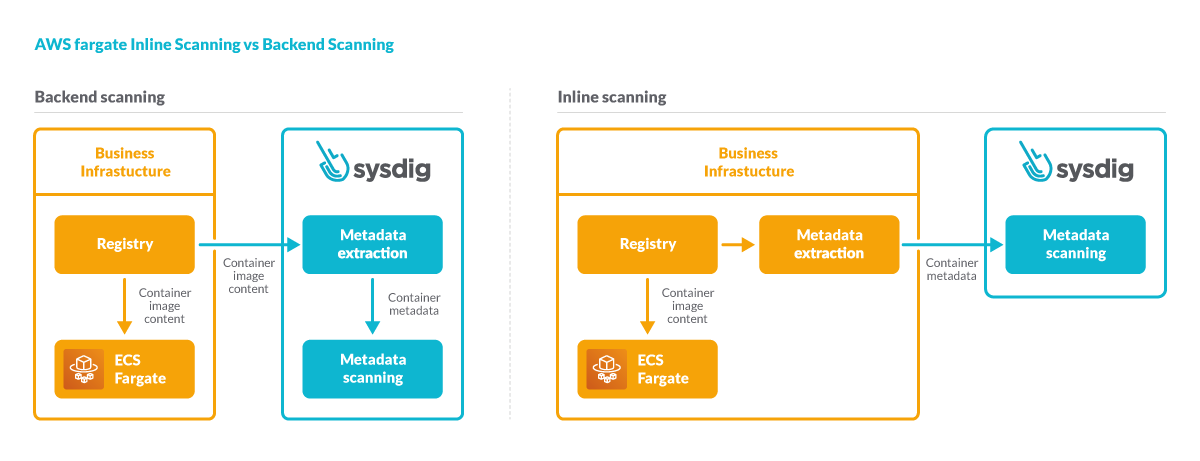
That’s the main advantage of inline scanning. The contents of your containers will never leave your infrastructure. This protects your privacy and prevents credential leaking. It’s also a requirement when security concerns require an air-gapped environment.
While inline scanning involves a few more components, in practice, its configuration is similar to a backend scanner.
An overview of ECS Fargate image scanning with Sysdig
Let’s now focus on inline image scanning, and how ECS Fargate image scanning with Sysdig works.
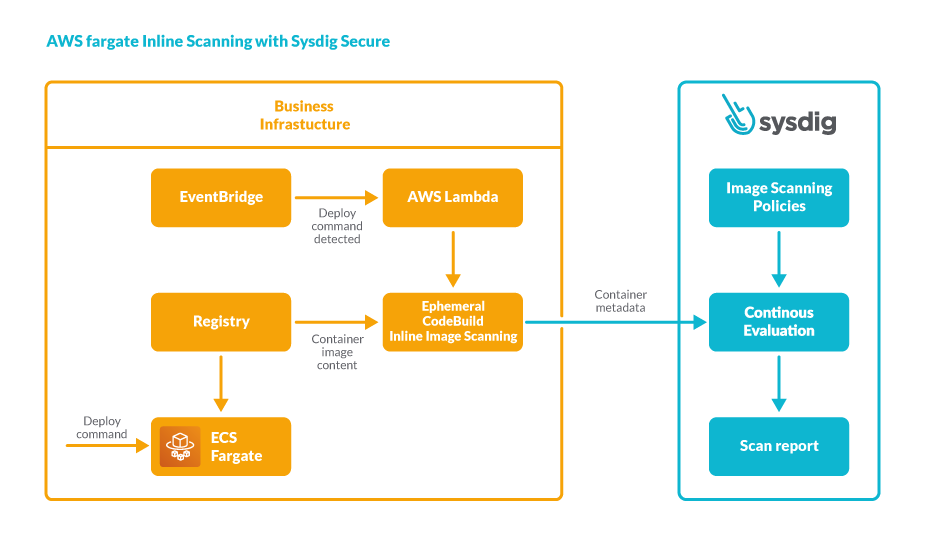
Any deploy command directed at ECS Fargate will trigger an image scanning. In particular the deploy command is detected by Amazon EventBridge, which will trigger a CodeBuild pipeline via an AWS Lambda function. It is within this CodeBuild pipeline that the image scanning runs.
The Sysdig inline image scanner will inspect the image to be deployed and will send its metadata to the Sysdig backend. The actual image contents won’t leave the CodeBuild pipeline.
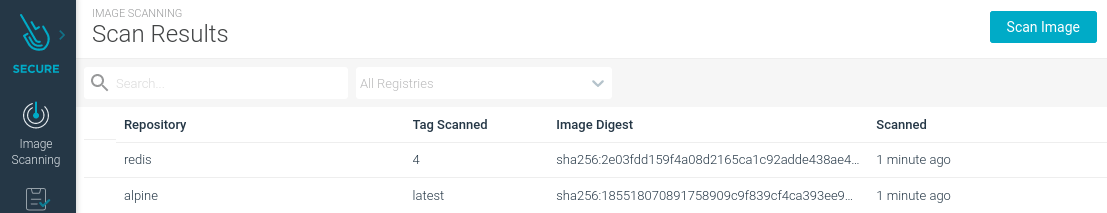
The Sysdig backend then evaluates the container metadata against your security policies. It will generate a scan report if the image doesn’t pass your security requirements, so you can take action.
There are several key points on Sysdig’s approach:
There is no need to build specific pipelines for each image. The scan will be automatically triggered for any workload that is executed in ECS Fargate across your whole infrastructure.
As the container metadata is retained in the Sysdig backend, there is no need to re-scan the images. Any update in the vulnerability databases, or any change in your policies, will eventually update the scan reports.
The Sysdig backend will act as a single source of truth for the security posture of all your running workloads. It centralizes all the security reports and from the same tool, you will also be able to check your compliance status and runtime security events.
Keep in mind that this approach is only part of the solution. You can further strengthen your security by implementing image scanning in other places of your DevOps lifecycle, like the CI/CD pipelines or in the registry. You should also implement other security controls like runtime security, compliance checks, or activity audit. Sysdig helps you extend security controls all over your AWS container services while serving as a single source of truth for the security posture of all your infrastructure.
Deploying ECS Fargate image scanning capabilities in a matter of minutes with CloudFormation
To deploy the Sysdig image scanner (inline or backend), we’ll use AWS CloudFormation.
AWS CloudFormation provides a common language to model and provision, in an automated and secure manner, all the resources needed for applications.
Applying Sysdig’s pre-made CloudFormation template is as simple as following a link and choosing some settings. The most up-to-date instructions are on the Sysdig Fargate scanning installation page.
Let’s dig in!
First, make sure to be logged into your AWS Console account with your browser.
Then, navigate to this link “CloudFormation template for ECS Fargate image scanning with Sysdig” to preview the CloudFormation template.
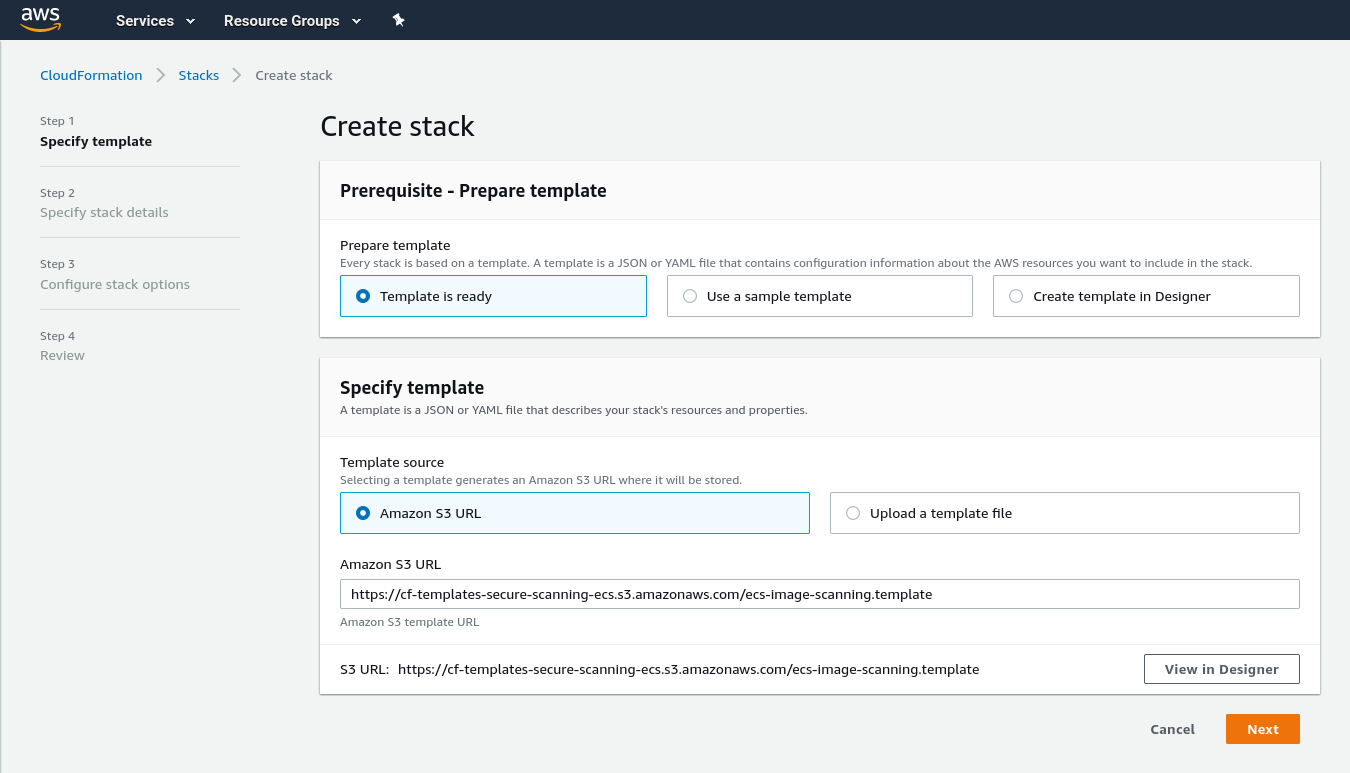
On the “Create stack,” click the Next button to start setting updeploying the template.
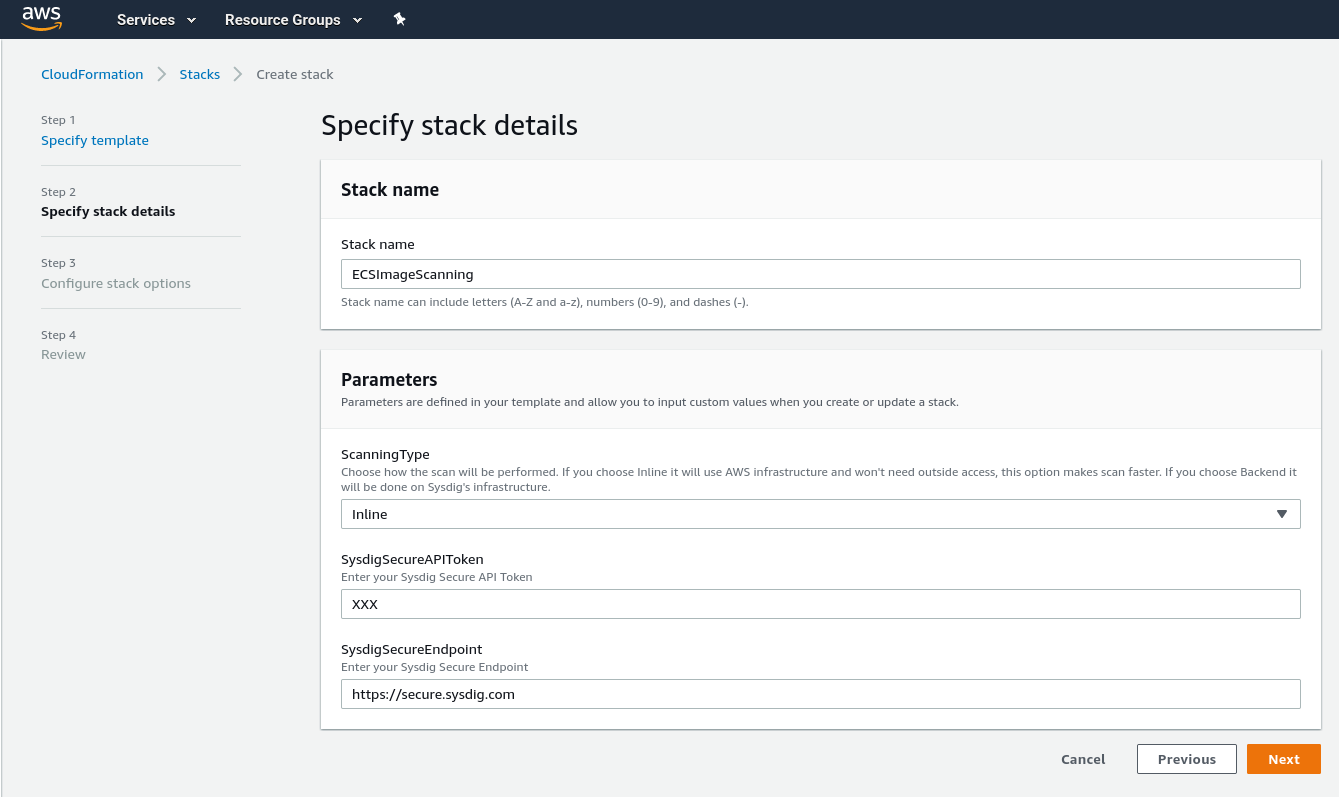
On the “Specify stack details” step you will be able to set several configuration options. For example, you will be able to choose between inline scanning or backend scanning.
You must also provide your Sysdig Secure API Token, and if you have an on-prem installation of Sysdig instead of SaaS, you will need to specify your endpoint instead of the default https://secure.sysdig.com. In case you have an air-gapped AWS infrastructure environment, the endpoint has to be accessible from within it.
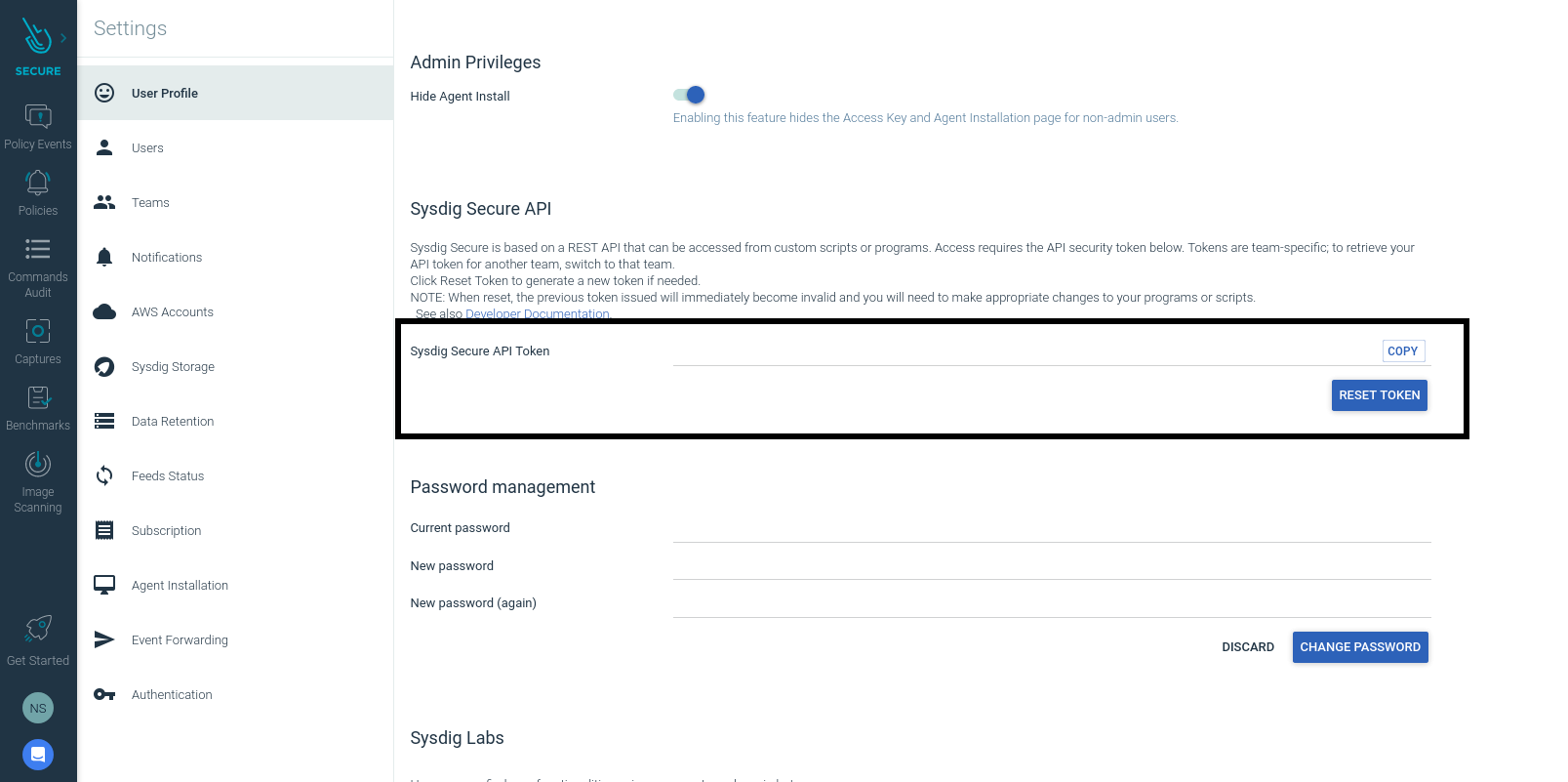
You can find the API token by visiting Sysdig Secure’s dashboard. Click on your profile icon at the bottom left, and select Settings. The API Token will be shown in the first section. Copy and paste it into the AWS Stack configuration, and click Next.
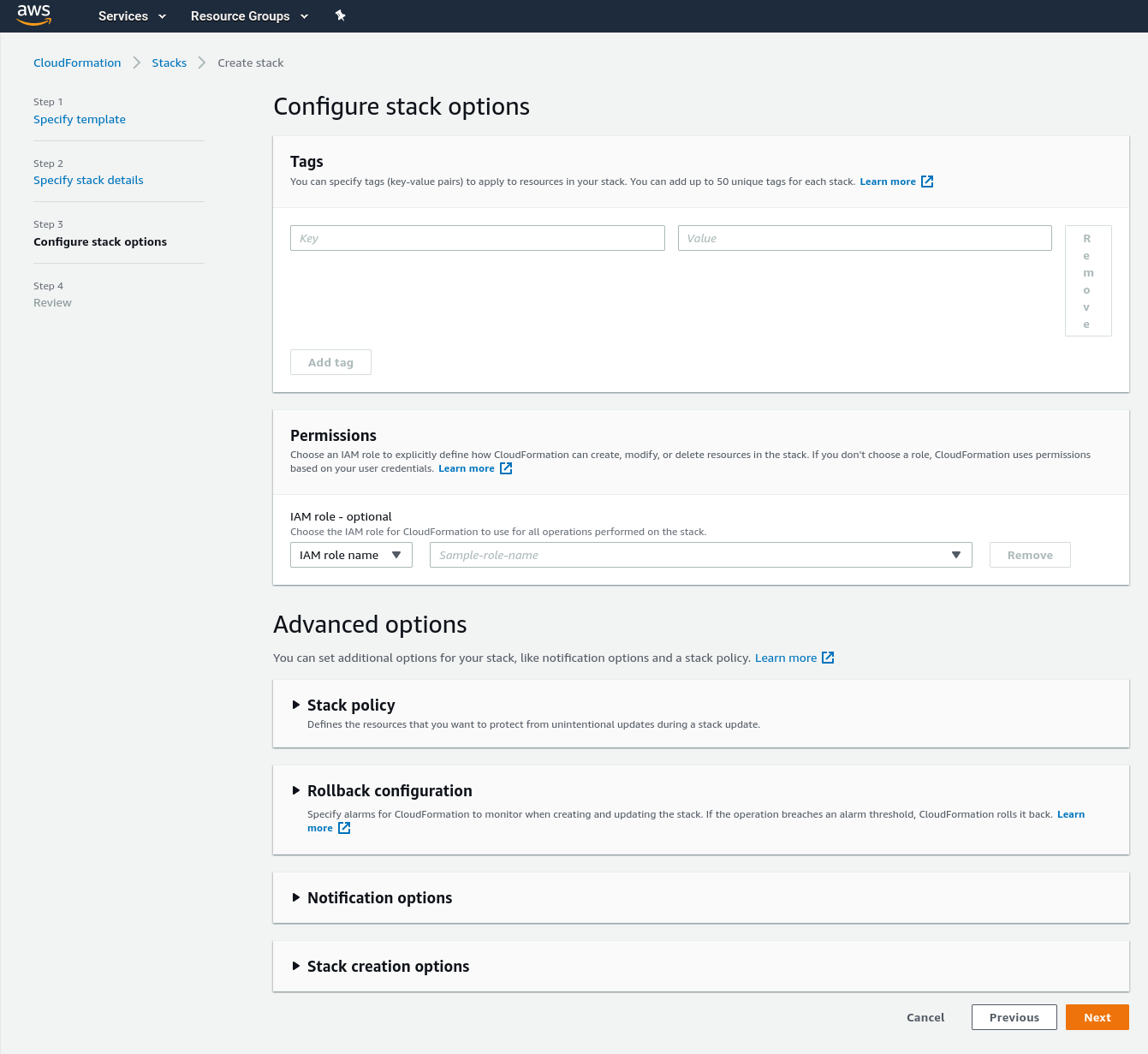
In the “Configure stack options,” a section for adding additional tags and permissions will be shown. If you need to add extra tags or permissions, this is the place.
When you are ready, click Next.
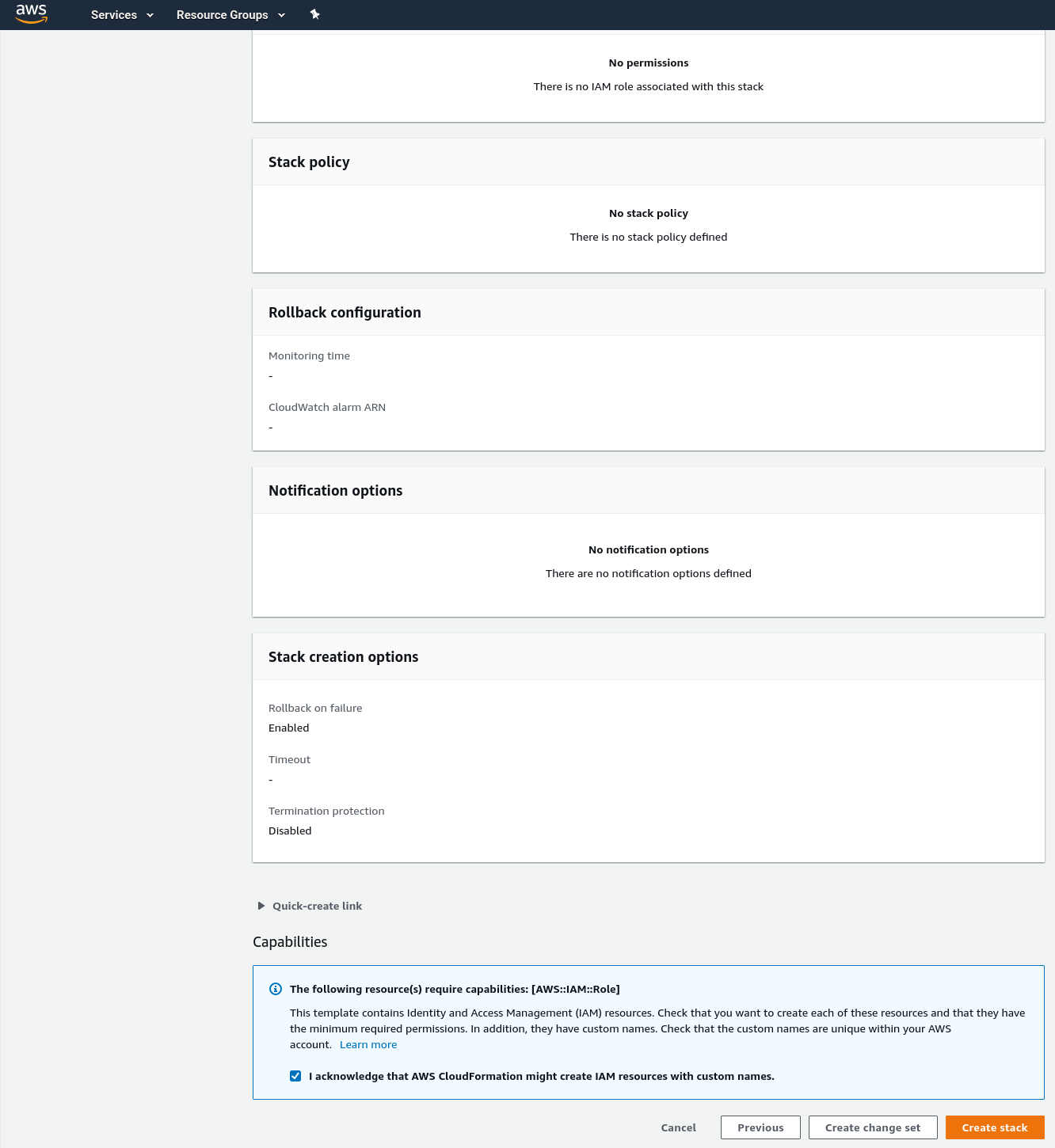
The last step will present a summary of all the parameters you introduced previously.
Check that everything is correct.
Notice that dedicated IAM roles will be created to perform the scanning. They are required for this deployment to work. We know IAM is a delicate service, so we designed those roles following the “least privilege principle” to enforce maximum security.
Once you are happy with the plan, acknowledge it by marking the checkbox, and then click the Create stack button.
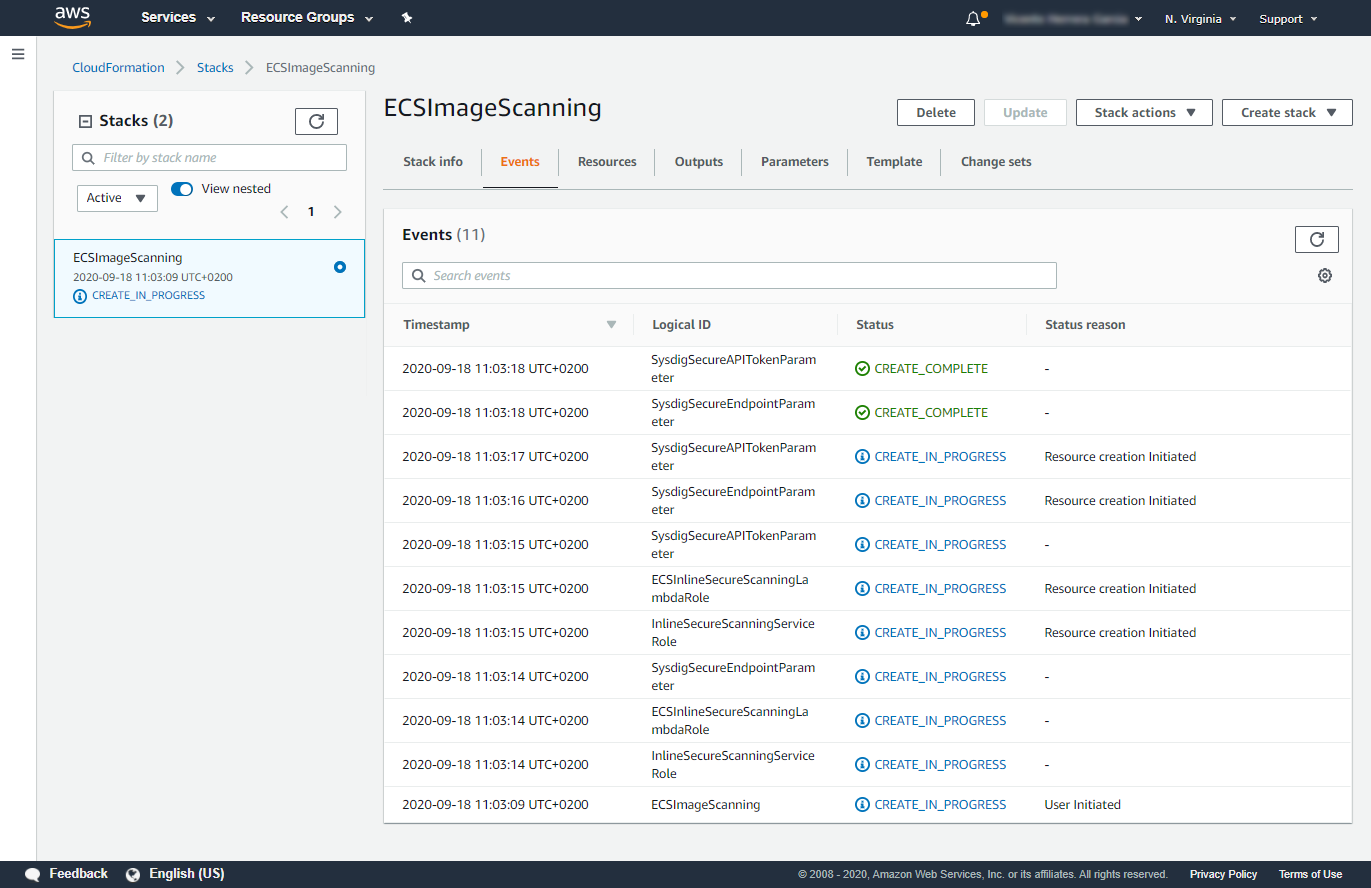
The CloudFormation stack will be created, and it will immediately start to provision the required resources. Wait until it finishes, it will take several minutes. You can revisit the CloudFormation section in AWS to check the status of the deployment.
Automatic Scanning on AWS Fargate for ECS
Once all stacks are created, you will be ready to deploy our ECS tasks in a Fargate cluster securely, as all the images that you deploy are going to be automatically scanned.
Let’s drill into how this works.
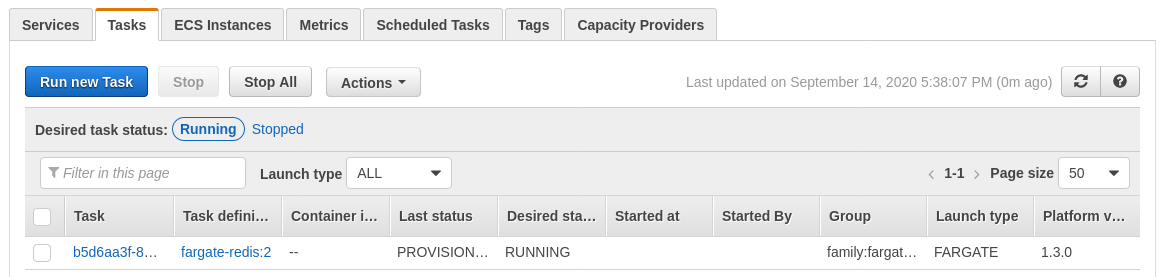
When a task in Fargate starts running, an event is automatically sent to a Lambda function. This Lambda function then triggers an image scanning. If it’s an inline scan, the scan report will be available at the CodeBuild pipeline. The scan report will always be available in Sysdig Secure.
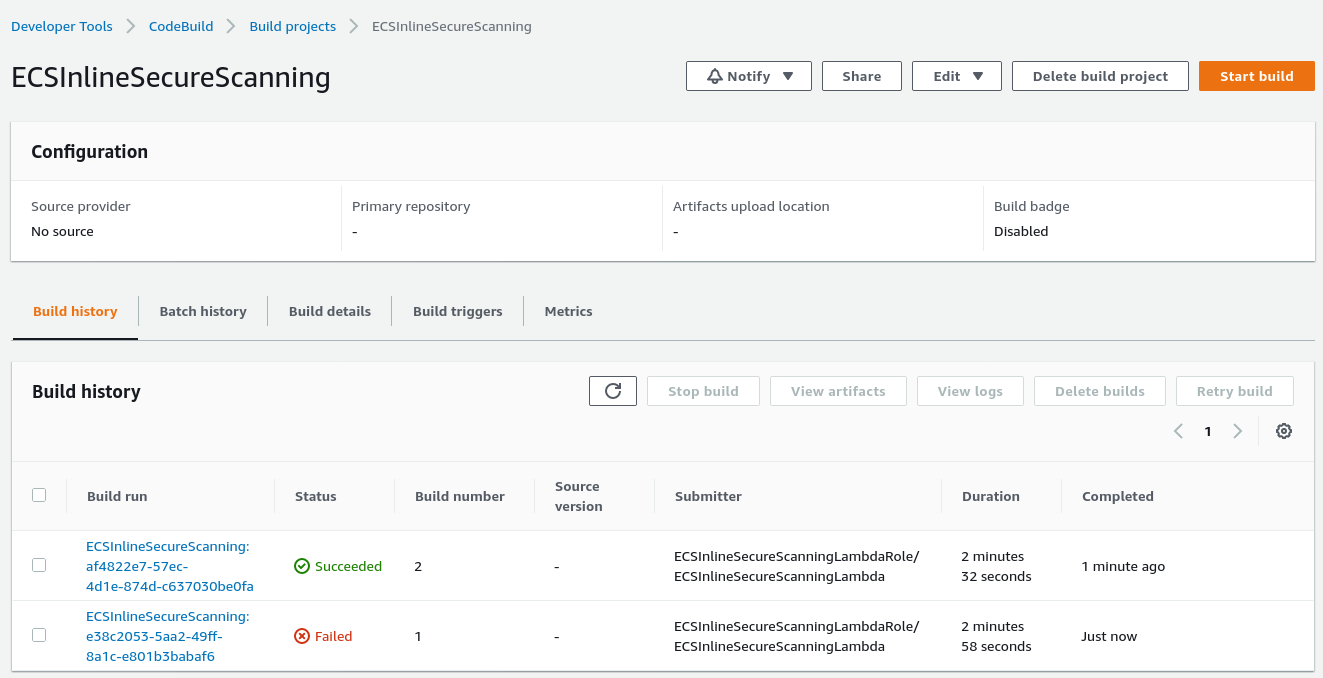
Another difference between inline and backend scanning is the number of Lambda functions that are created. If the selected scanning mode was Inline, the Lambda function will launch a CodeBuild pipeline for each of the task’s images. If the selected mode was Backend, the Lambda function will trigger a single API call to the Sysdig Secure’s backend. Then, Sysdig will pull all the images and perform the scan on each one.
And that’s it. After these initial steps, this integration will magically work without you having to set up anything else in your future projects. By automatically scanning any workload executed on ECS Fargate, you are shifting left the security in our DevOps workflow.
Conclusion
AWS ECS Fargate enables DevOps engineers to deploy applications very quickly.
At first, imposing security measures may seem like it takes away flexibility, but the right automated tools will integrate with your workflows and won’t slow you down.
Sysdig inline and backend scanning for ECS Fargate is an easy way to scan all workloads in an automatic way so you don’t need any additional setup for each project. All your security reports will be centralized on the Sysdig platform, including information on any vulnerabilities or misconfigurations detected.
Start using Sysdig for ECS Fargate security by requesting a trial account today!
You can also find Sysdig on the AWS Marketplace.

