We’ve introduced an updated opensource sysdig cheatsheet of our favorite commands for getting deep visibility into containers and linux servers!
Sysdig started off with a simple goal in mind: “To give you easy access to the actual behavior of your Linux systems”.
One prime example is the missing link between the network and the host. There are tools that let you see what’s happening on the wire, and different tools that let you look at activity inside your machines. But even though the two worlds are deeply related, the picture you get today is disconnected at best. So disconnected, in fact, that the simple task of understanding which process is sending data to the network is something that has eluded a clean solution.
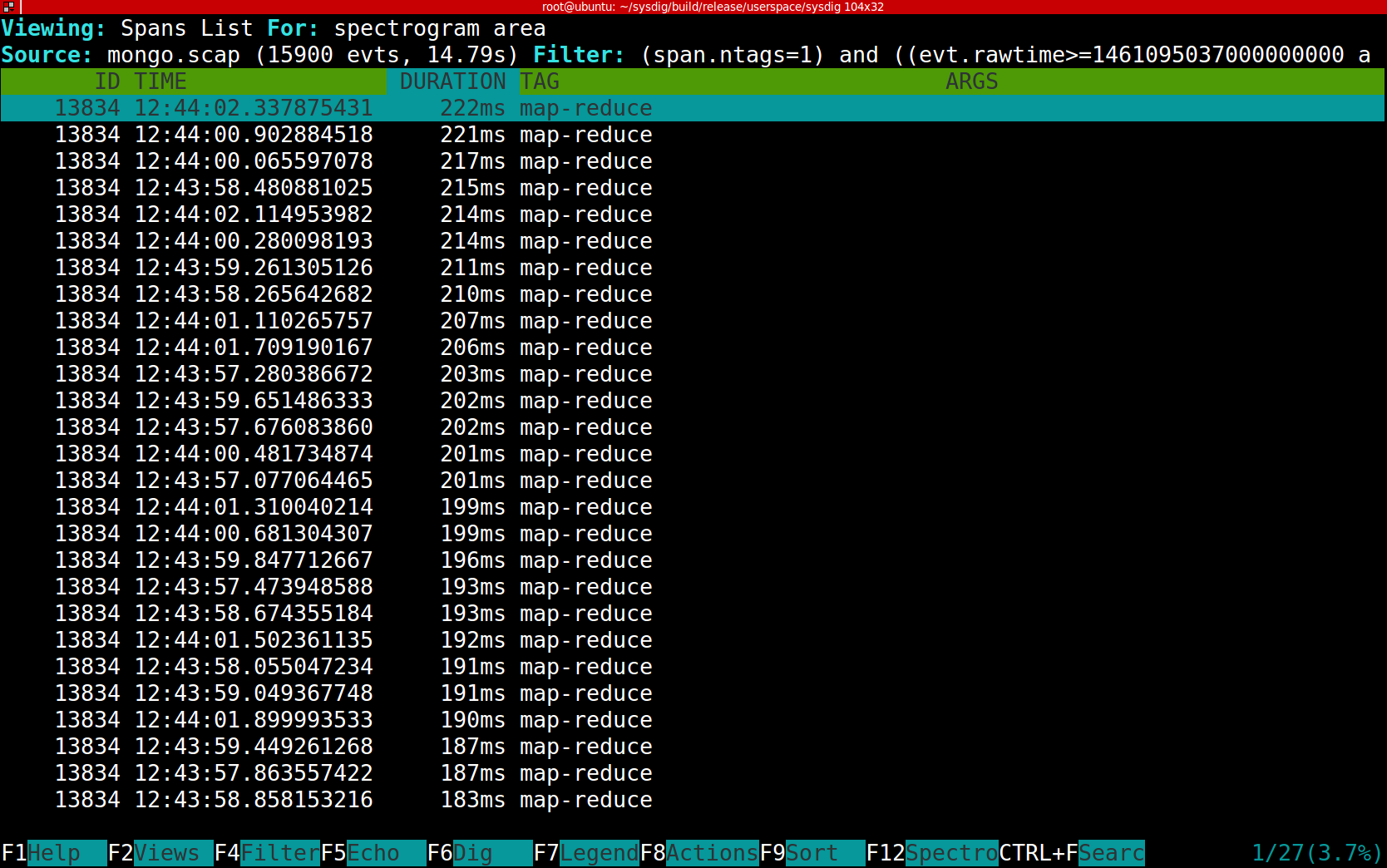
With sysdig you can do this:
Or, if you like a simpler view, this:
Around the same time as the creation of sysdig a company named DotCloud developed Docker, and the rest is history. If you are new to sysdig or troubleshooting containers this linux troubleshooting cheatsheet is a great transition from tools like htop, strace, tcpdump, and other tools you’ve likely used in the past.