Modern security for modern infrastructure
Detect faster and respond smarter

Real-time detection and configurability
Ditch the black box approach with customizable and transparent detection and detection logic across your entire cloud estate. Sysdig unlocks adaptability and speed with real-time runtime detection.
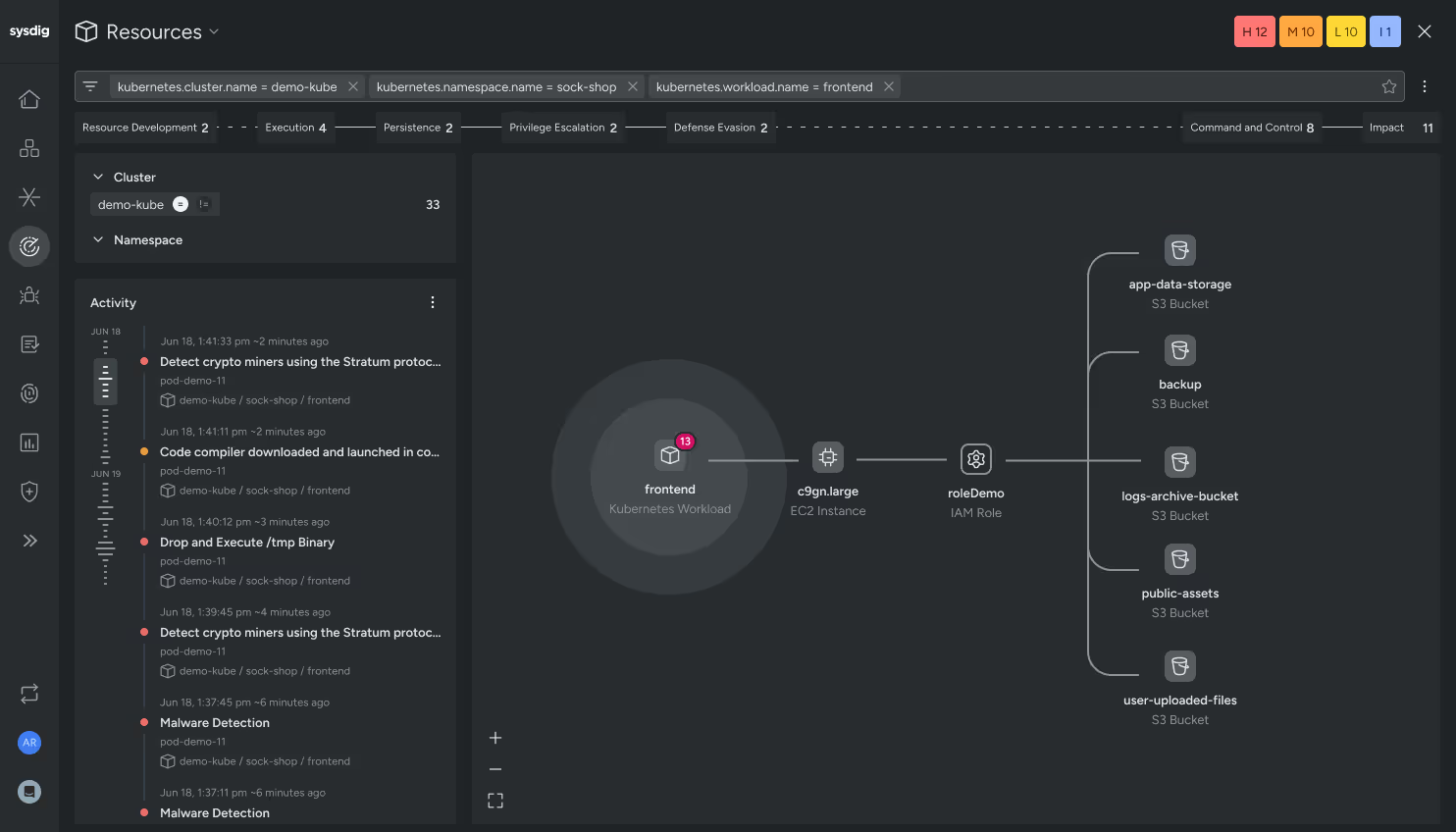
Contextualized investigation
Automatically correlate insights across hosts, containers, and cloud activity for streamlined forensic triage and investigation. Capture every Linux system call and access rich context to quickly evaluate an event’s impact.
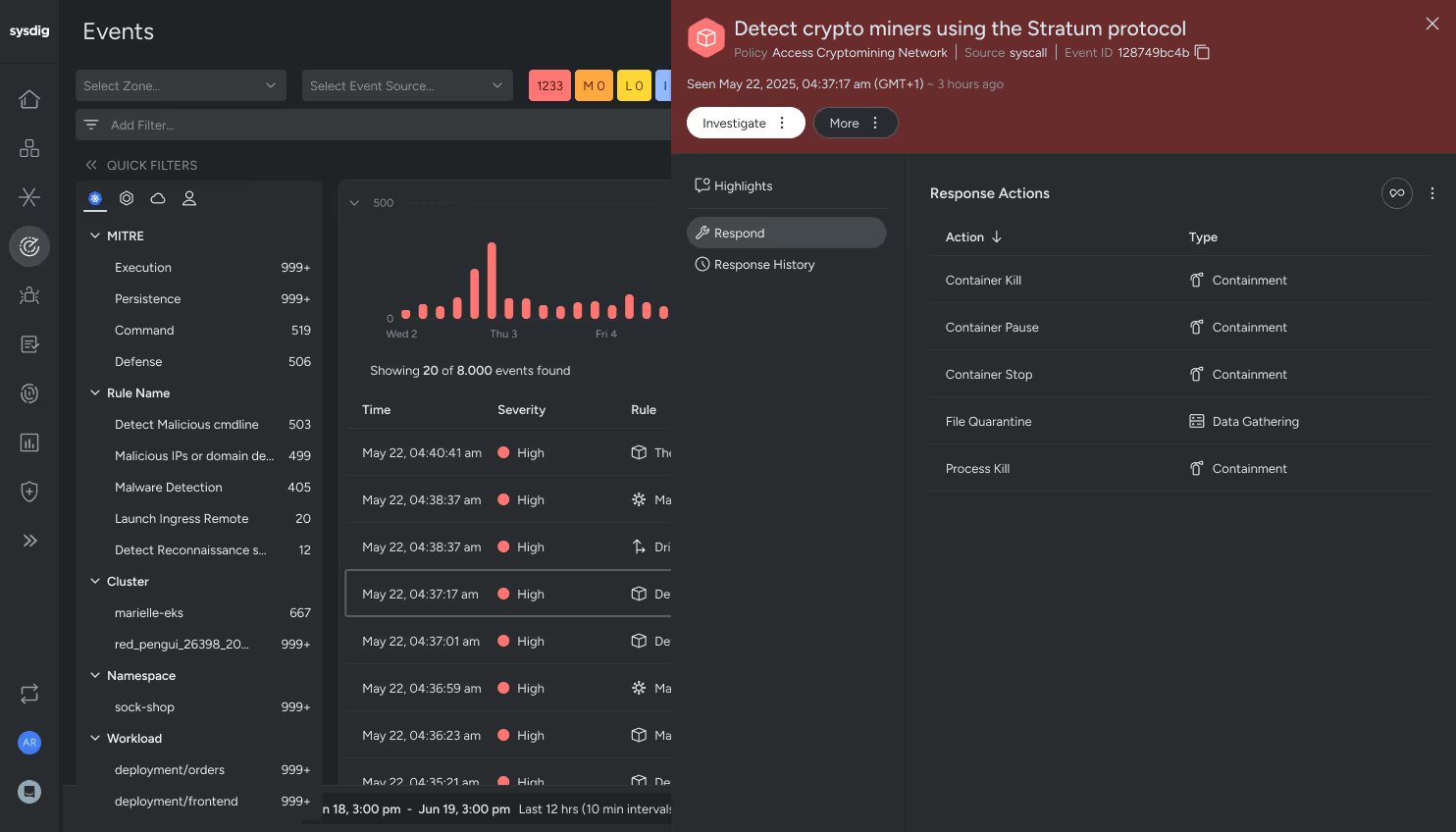
Flexible response options
Accelerate response with automation and granular control across a variety of capabilities. Connect a remote shell within your environment to troubleshoot directly, initiate a response inline from the event, or automate response actions through policy or through Sysdig’s streamlined automation logic.
Without Sysdig, it would be far more complicated to get the information we need. The solution provides us with a single pane of glass, giving us complete visibility into the state of our infrastructure.
How Sysdig’s server threat detection works
Sysdig server threat detection starts with our lightweight agent, fueled by the adaptable and transparent Falco detection engine. Our agent streams kernel-level events, cloud service logs, and Kubernetes metadata in real time. This continuous monitoring and detection of runtime vs. scheduled scanning detects tactics and techniques such as privilege escalation, container escape, and suspicious process launches in real time, without visibility gaps across hybrid and multicloud estates. This is imperative because cloud attacks need less than 10 minutes to fully execute.
Sysdig’s high-fidelity threat detections are correlated and enriched in the Sysdig threat management hub. In this hub, you can quickly understand the who, what, where, and how of a threat with AI-assisted summaries and forensic-level data analysis that has been contextualized and correlated for you.
Real-time runtime threats are enriched with posture data from the Sysdig event feed, which provides analysts supplemental data to dig deeper during threat hunting and post-event analysis. Sysdig’s Cloud Attack Graph unlocks additional posture context, enabling a more comprehensive investigation and response.
Sysdig also delivers highly effective automated and manual response capabilities. Automated responses can be initiated by policy, such as with container drift, shutting down a container that has drifted from a baseline or forensic collections. Other manual response capabilities can be accelerated through Sysdig Automations, a no code/low code automation framework to initiate response actions such as file acquisition, ticketing, or messaging based on predefined logic.