Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

At Sysdig, we are constantly looking for ways to improve the security posture of the organizations that we work with. One of the areas we continuously improve upon is our platform's threat intelligence and detection capabilities that leverage the open-source Falco project. We incorporate threat intelligence sourced from our own strategically placed honeypots, data collection systems, and multiple other open-source feeds.Sysdig scans for hundreds of IoCs – "indicators of compromise" – to enrich and provide context to our detections. To bolster our capabilities in this area even further, Sysdig has integrated with threat intelligence from Proofpoint, a leader in "Emerging Threats" detection. Timely and accurate threat feeds of malicious IPs and domain names are pulled from Proofpoint into Sysdig Secure. These are then used to drive Falco-based threat detection that helps our customers prevent attacks and reduce risk.
Proofpoint is a leading cybersecurity company that protects the people, brand, and data of organizations against advanced threats and compliance risks. Proofpoint's Emerging Threat (ET) Intelligence provides actionable threat intel feeds to identify IPs and domains involved in suspicious and malicious activity. All threat intelligence feeds are based on behavior observed directly by Proofpoint ET Labs. Read more about Proofpointhere. These are the top five reasons why Sysdig chose to partner with Proofpoint for sourcing additional threat feeds, as they:
- Are big on malware detection and identifying different types of attacks.
- Provide context and categorization around threats.
- Constantly update the malicious IPs and domains lists leading to better detections.
- Have a robust threat research organization behind it.
- Follow a good scoring system and keep the malicious IPs and domains lists accurate.
Below is a four-step illustration of how this partnership and integration between Proofpoint and Sysdig protects organizations.
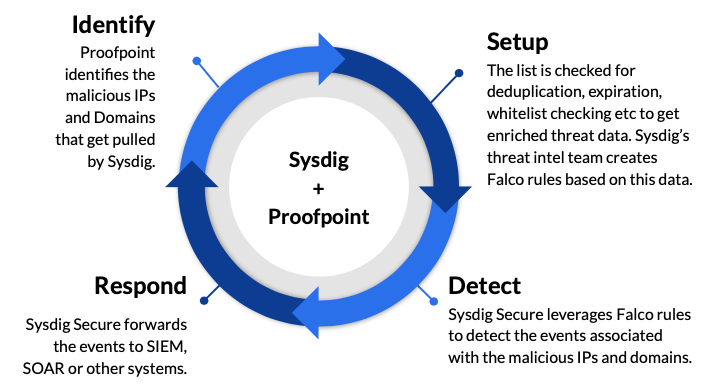
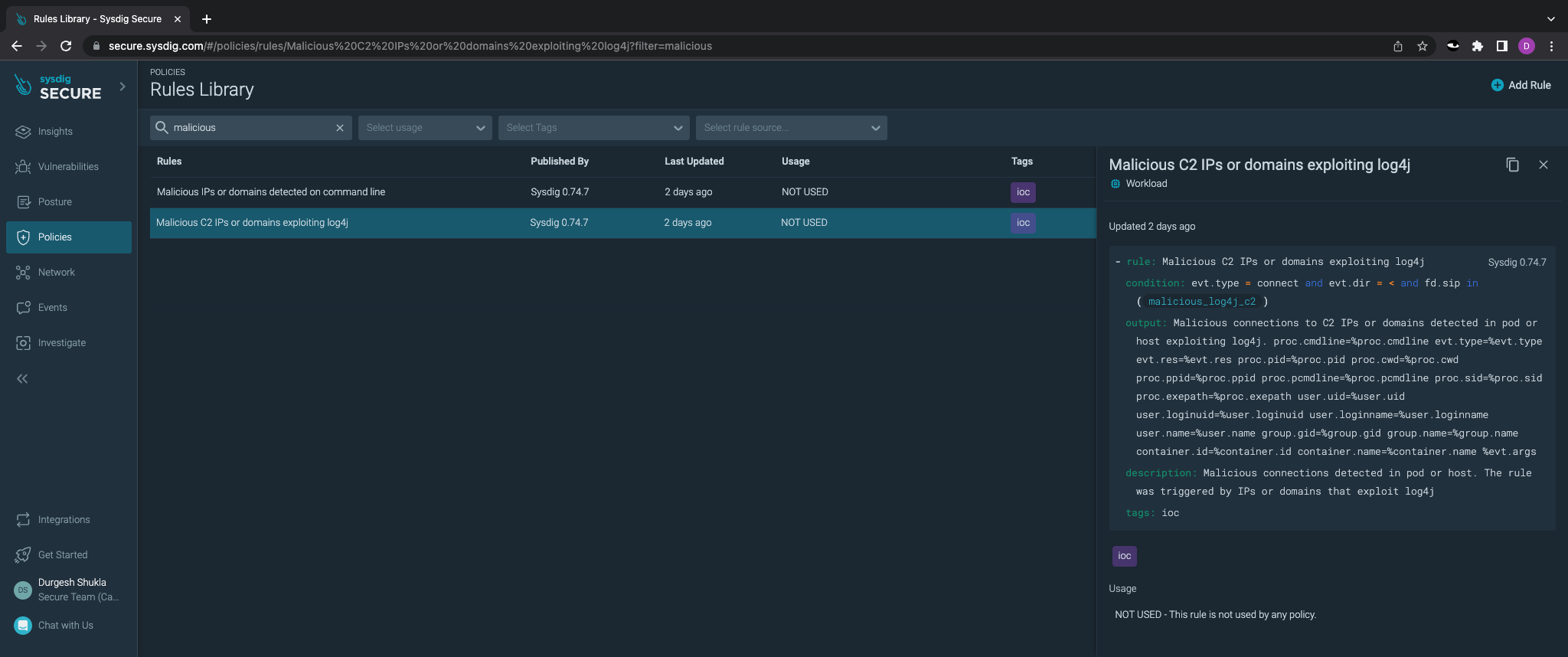
The list of malicious IPs and domains data that Sysdig pulls from Proofpoint is fed into a threat intelligence platform which checks for deduplication, expiration, whitelist checking, etc., and that generates a rich contextual data about threats. This data is then used by Sysdig Secure's threat intelligence team to create Falco rules. Falco rules help to analyze and alert on the behavior of various actors that are associated with customer infrastructure. These rules increase the overall threat awareness for the customers' incident response (IR) or security operations center (SOC) teams. This technical partnership provides Sysdig customers with the ability to protect customer endpoints from an ever-changing threat landscape at no additional cost.
Sysdig Secure also allows the forwarding of any suspicious events to SIEMs and SOAR systems. This means less risk and less time spent identifying, resolving, and recovering from incidents for Sysdig customers.
Conclusion
We are thrilled about this partnership as Sysdig Secure would now get the latest threat intelligence feeds from ProofPoint, which would:
- Help detect attacks and adversary activity based on timely and accurate threat intelligence feeds.
- Stay up to date on new malicious IPs and domains.
- Expand the scope of indicators of compromise that we scan for to 10s of thousands.
In the future, we plan to expand on the integration so that Sysdig can:
- Provide context, such as location, and perform enrichment of the activity audit that we provide to our customers within Sysdig Secure.
- Leverage the premium set of SNORT (network-based intrusion detection system) rules provided by Proofpoint to do file hashes and, thus, detect malicious files.
- Broaden detection capabilities with regards to different types of threats.
Please feel free to share this article and also give this official press release from Sysdig and Proofpoint a quick read, as we have announced multiple other features for Sysdig Secure.