Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

The Sysdig Threat Research Team (Sysdig TRT) recently discovered a long-running botnet operated by a Romanian threat actor group, which we are calling RUBYCARP. Evidence suggests that this threat actor has been active for at least 10 years. Its primary method of operation leverages a botnet deployed using a variety of public exploits and brute force attacks. This group communicates via public and private IRC networks, develops cyber weapons and targeting data, and uses its botnet for financial gain via cryptomining and phishing. This report explores how RUBYCARP operates and its motivations.
RUBYCARP, like many threat actors, is interested in payloads that enable financial gain. This includes cryptomining, DDoS, and Phishing. We have seen it deploy a number of different tools to monetize its compromised assets. For example, through its Phishing operations, RUBYCARP has been seen targeting credit cards. As we have seen with other threat actors, it has a diversified set of illicit income streams.
Attribution
RUBYCARP, the name we have given this group, is a financially-motivated threat actor group that is most likely Romanian. RUBYCARP may be related to the Outlaw advanced persistent threat (APT), as it does share many of the same tactics, techniques, and procedures (TTPs). However, since these shared TTPs are common across many botnet operators, we cannot definitively make this conclusion. RUBYCARP leverages Shellbot often during its operations, which can also cause attribution confusion since this tool is a common choice among threat actors.
In the murky world of cybercriminal threat intelligence, there is often a lot of crossover in both tools and targeting. In the recent advisory from CISA, the Androxgh0st threat actor's choice to exploit Laravel is discussed. This is another example of cybercriminal overlap, with RUBYCARP notably targeting the same framework vulnerabilities. Many of these threat actors are fighting it out over the same target space, making it difficult to attribute attacks.
What is RUBYCARP?
For months, Sysdig TRT's has been tracking RUBYCARP through the targeting and exploitation of Laravel applications vulnerable to CVE-2021-3129. This led to evidence of SSH Brute forcing as another way the group gained access to its targets. Recently, we also discovered evidence of the threat actor targeting WordPress sites using dumps of usernames and passwords. RUBYCARP continues to add new exploitation techniques to its arsenal in order to build its botnets.
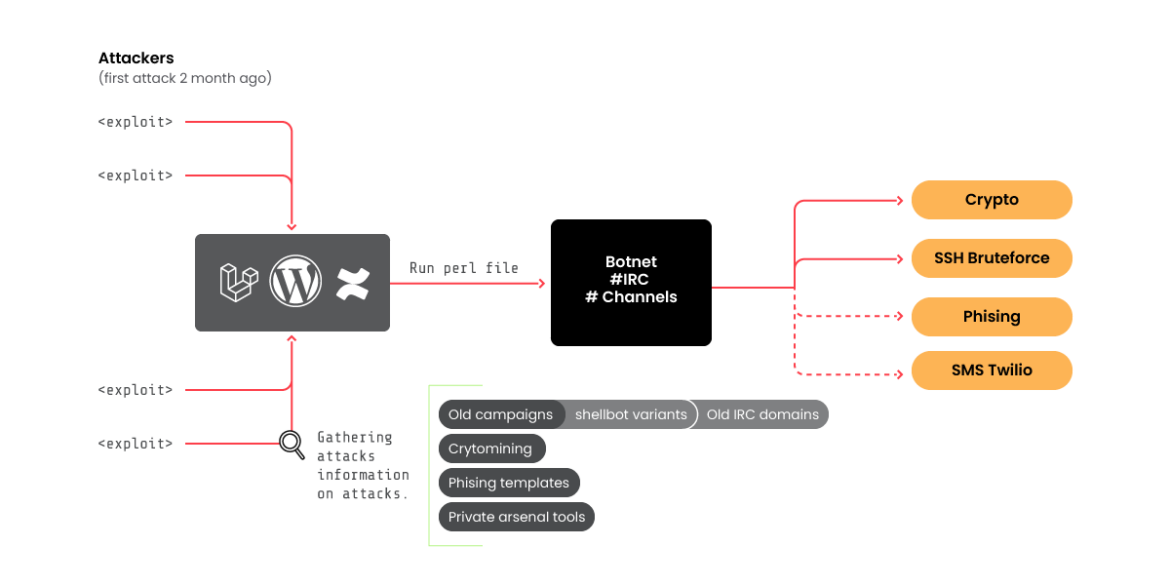
Once access is obtained, a backdoor is installed based on the popular Perl Shellbot. The victim's server is then connected to an IRC server acting as command and control, and joins the larger botnet. During RUBYCARP's reconnaissance phase, we found 39 variants of the Perl file (shellbot), but only eight were in VirusTotal. This means that only a few campaigns were previously detected. The modifications of the files are:
- A nickname is used to join the IRC server
- The channel where the victim joins is often marked by either a platform name (e.g., apache) or a member name (e.g., juice)
- Sometimes auth is added
- The IRC server
Campaigns
After connecting to the IRC server, we discovered the actual number of compromised hosts at over 600. On the other hand, by not properly configuring the connection to the server, RUBYCARP has a detection system to kick out unexpected/unwanted users of the server and ban their IP to prevent new connections. It tries to keep the network hidden as much as possible.
The last active domain of this botnet is chat[.]juicessh[.]pro, and we were able to obtain the information below:
- It was created on Monday, May 1, 2023 at 04:30:05 UTC
- 624 nicks [2 ops, 0 halfops, 0 voices, 622 normal]
- VICTIMS by channel at the moment of writing:
- #juscan1, 176 victims
- #cfs, 11 victims
- #php3, 34 victims
- #sb, 33 victims
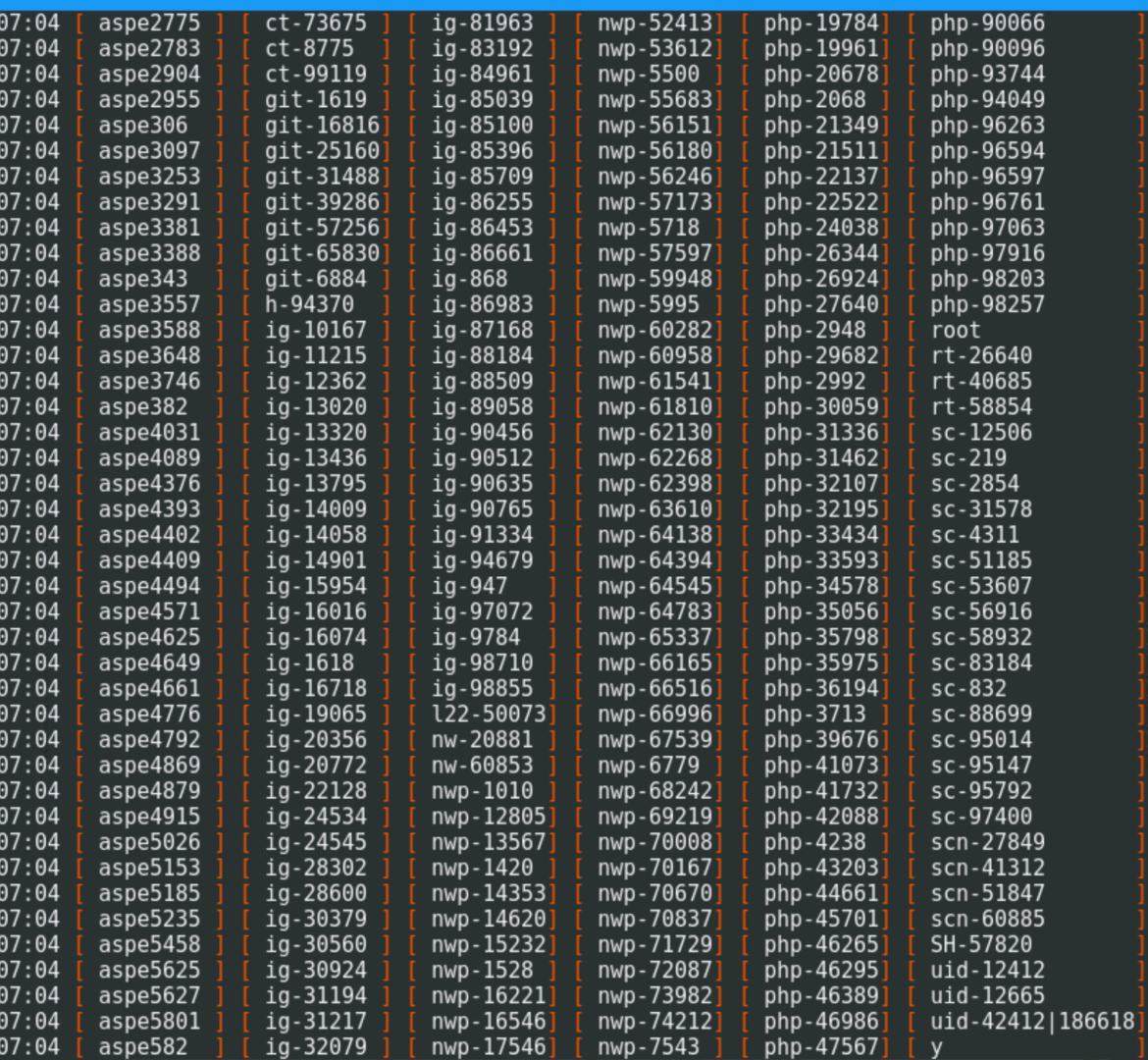
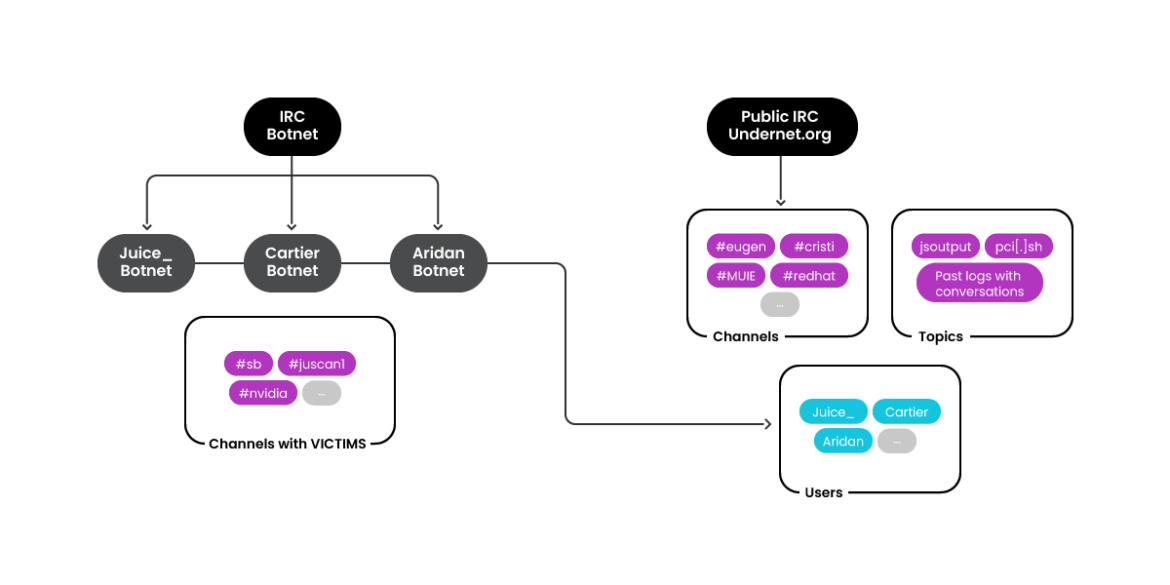
Based on naming schemes and connection configuration, the apparent group would be composed of users like "juice," "cartier," or "aridan," but there could be more, where each one might be dedicated to a purpose, cryptomining, customized tools, etc. During our investigation, we determined that its IRC server of choice for public and private hosting is undernet.org. The active private IRC networks are chat[.]juicessh[.]pro and sshd[.]run.
The infrastructure we discovered for RUBYCARP is comprised of a significant number of malicious IPs and domains, rotated regularly and often replaced and emptied of its malicious content as soon as any potential research activity was detected. A full infrastructure list is available here.
How does RUBYCARP Operate?
RUBYCARP uses multiple IRC networks for general communications, but also to manage its botnets and coordinate cryptomining campaigns. An outline of its organization when managing botnets would be as follows:
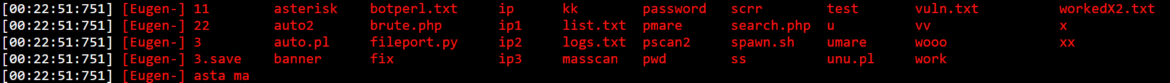
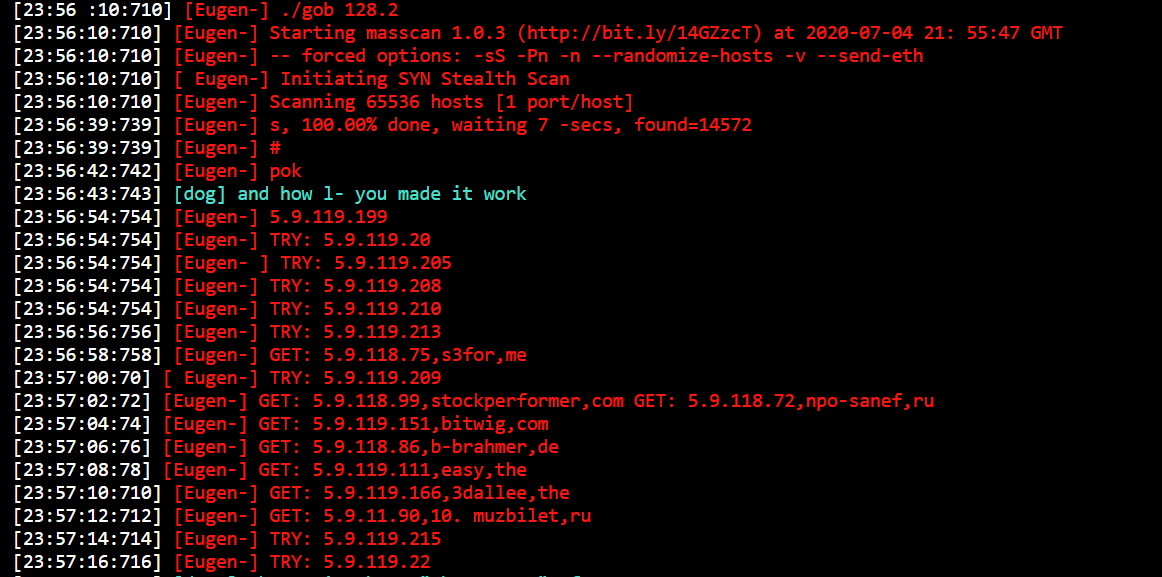
In one of the logs we acquired, RUBYCARP tends to share the tools it is using, which include many of the tools we have been able to collect through our honeypot, such as:
- Banner
- Masscan
- X (kernel module)
- brute
Communications
Private IRC
For managing its botnet, RUBYCARP uses a collection of private IRC servers and seems to rotate them regularly. "Juice.baselinux.net," "chat.juicessh.pro," and others are the latest active ones at the time of writing. Each RUBYCARP campaign gets its own IRC channel and the bots within each channel are then named according to a predefined scheme. We were able to map the observed servers and their respective channels, although, unfortunately, not all of them are still active or accessible.
Public IRC
Members
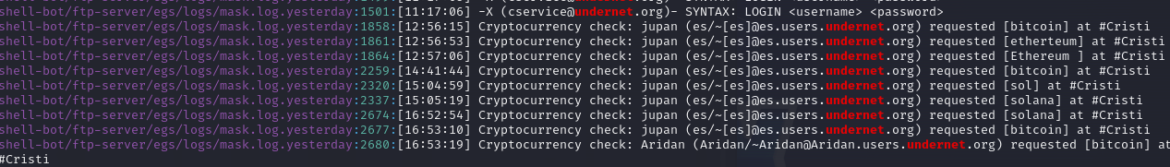
Members of RUBYCARP mainly communicate through an Undernet IRC channel called #Cristi. Public logs for the channel show a user (and admin) "_juice" interacting with other members of the group in Romanian; we can also see that the channel topic is related to previous or current campaigns, available below.
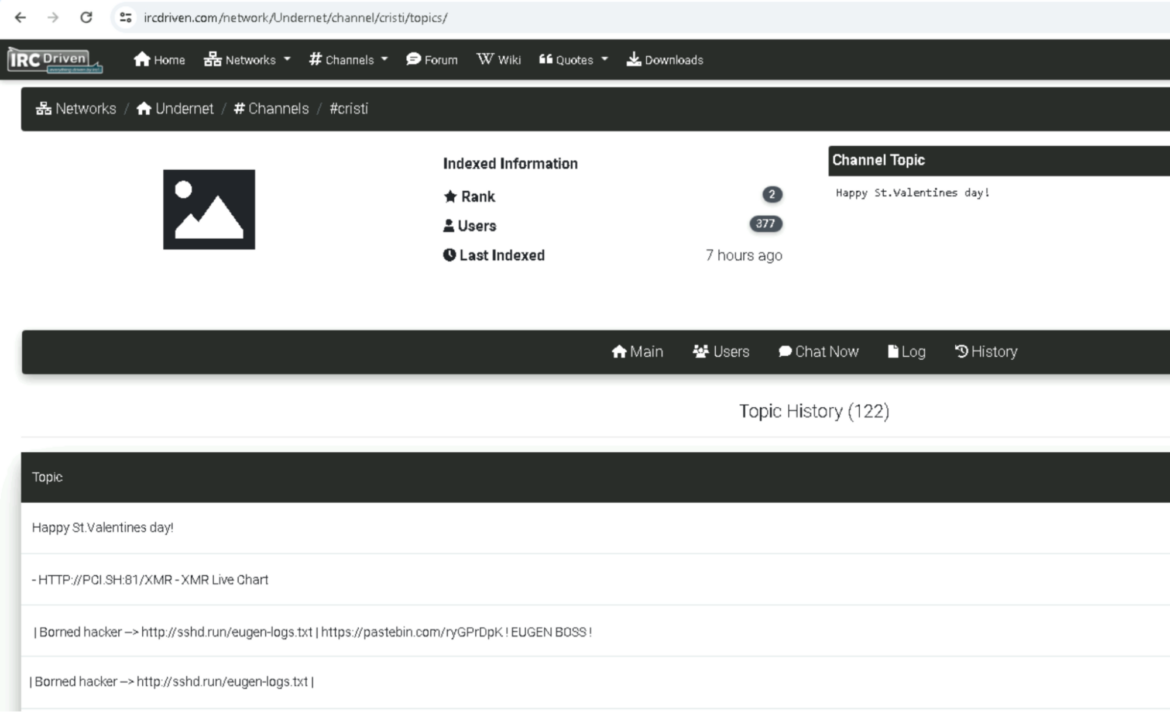
While we monitored the chats, both actors, juice and Eugen, who own the channel #Eugen from which we collected most of the mining setup evidence, were present in channel #Cristi.
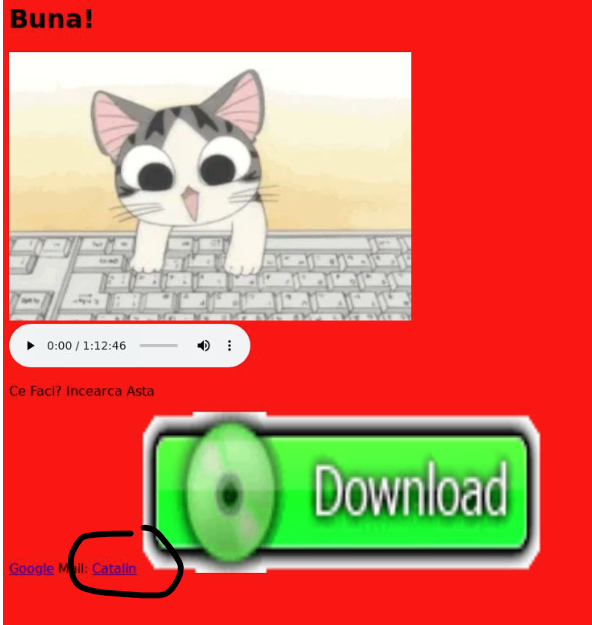
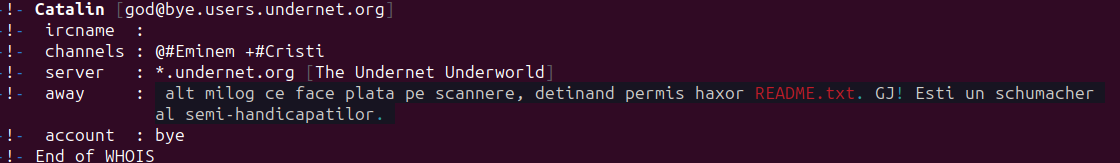
Within the user base of the channel #Cristi, which at the time of writing contained 280 users, we identified multiple familiar names of actors who attacked our honeypot. For example, "Catalin" attacked our honeypot on Jan. 8, 2024 from IP 80[.]83[.]124[.]150. The following image is of the website hosted there at the time of the attack. Notice the attribution to "Catalin" at the bottom.
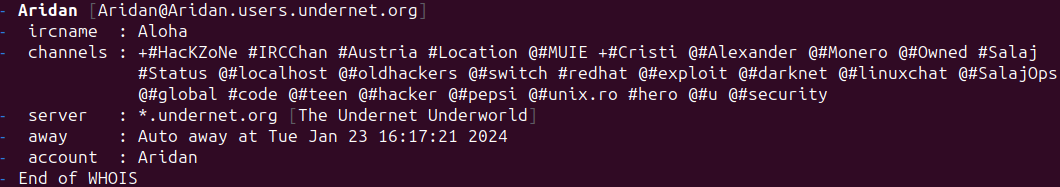
Another one is "aridan," who we observed in previous attacks with the domain "aridan.men."
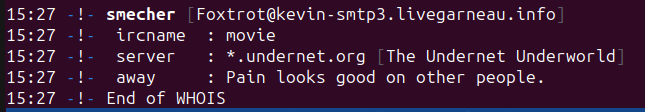
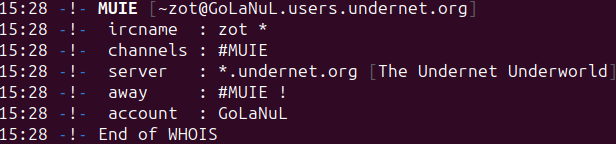
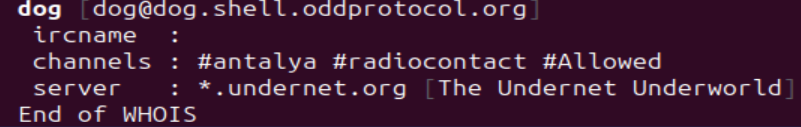
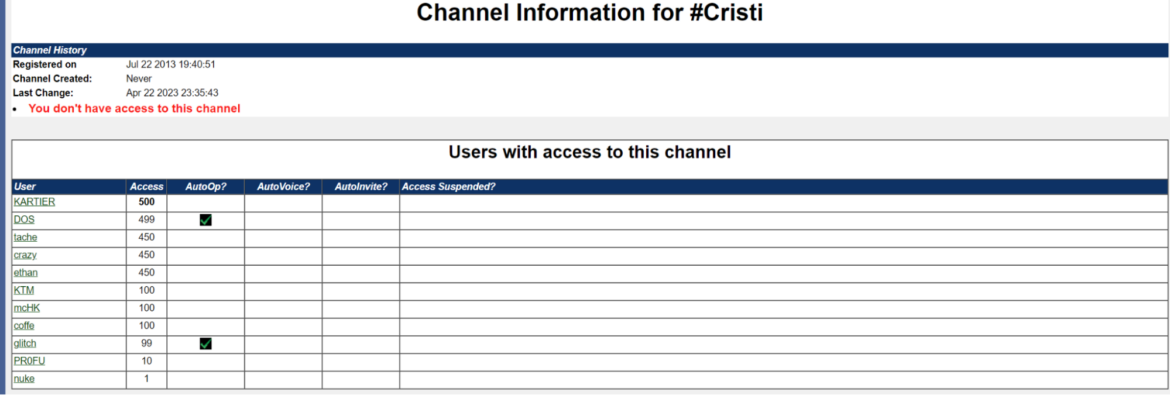
The most recurring IRC admins we found within the Shellbot configuration files are "juice," "MUIE," and "Smecher," who also each have their own respective channels for malicious operations. "juice" has been the most prolific in setting up new malicious Shellbot configurations, new servers, and new victim channels. Below is the WHOIS screenshot for the #Cristi channel members we've identified:
juice_, admin
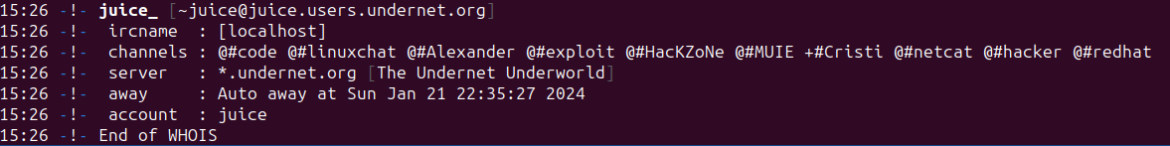
Smecher, admin
MUIE, admin
Aridan, member
Catalin, member
Dog, developer
Community
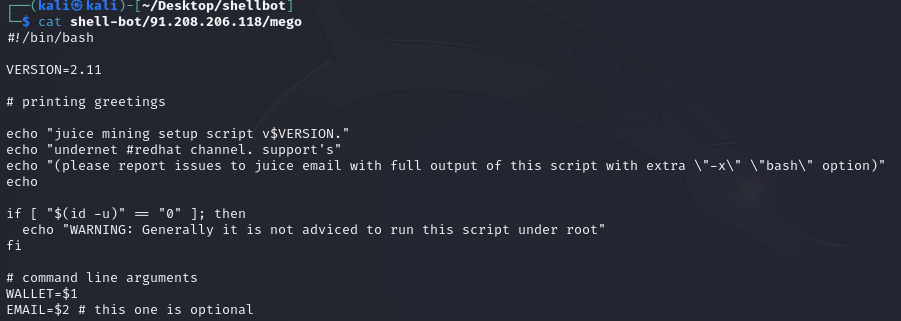
We identified a custom script that is plausibly circulated among the group members on how to set up the juice mining operation. It then lists the #redhat channel hosted on undernet for support. This channel has no official relation to RedHat the business or software, and is likely just a nod to redhat vigilante hacking.
The redhat channel uses the undernet IRC network. Specifically, this group uses the Romanian server bucharest.ro.eu.undernet[.]org, where the username @juice_ is present.
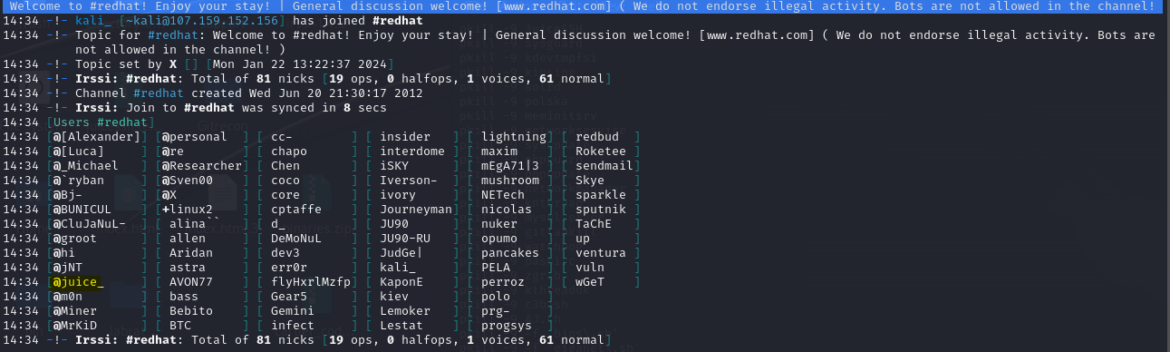
The channel #Cristi is used to set up mining operations and keeps track of the members utilizing the custom malicious tools we encountered, often signed by "Juice" and "Cartier" (aka "dog" and "Kartier") group members.
Within the channel #Cristi logs we were able to scrape, we found a reference to an external link http://physics.uctm.edu/funis/eugen. To our surprise, it contained quite an extensive record of logs taken from the private channel #Eugen, which we had not seen before.
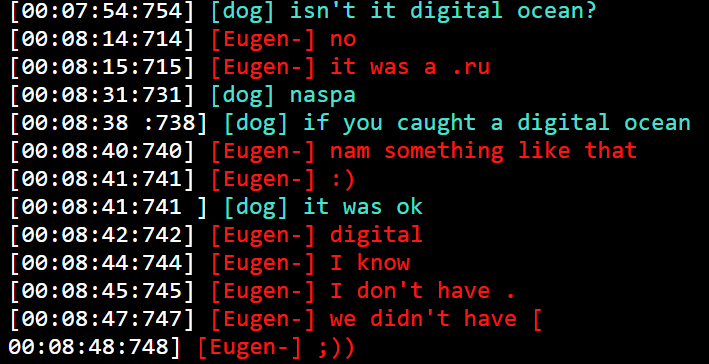
By investigating what we had found, we quickly discovered that the two people involved in most of the interactions within these logs were user "Kartier" (signed as "dog") and "Eugen." Both members were present, at different times, in the channel #Cristi. "Eugen" seems to be a moniker for a Romanian individual who also conducts malicious operations alongside the other members, as the logs containing their own miner setups attest.
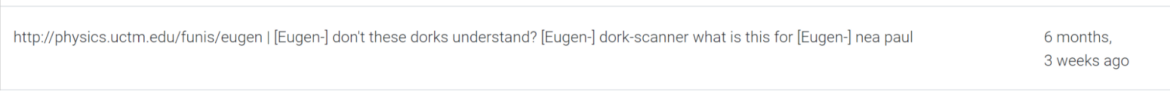

The main domain where these logs are currently saved belongs to a legitimate Bulgarian University, the University of Chemical Technology and Metallurgy. The subdomain physics.uctm[.]edu appears to be compromised by RUBYCARP and contains detailed instructions and information on the tools used and the miner configuration.
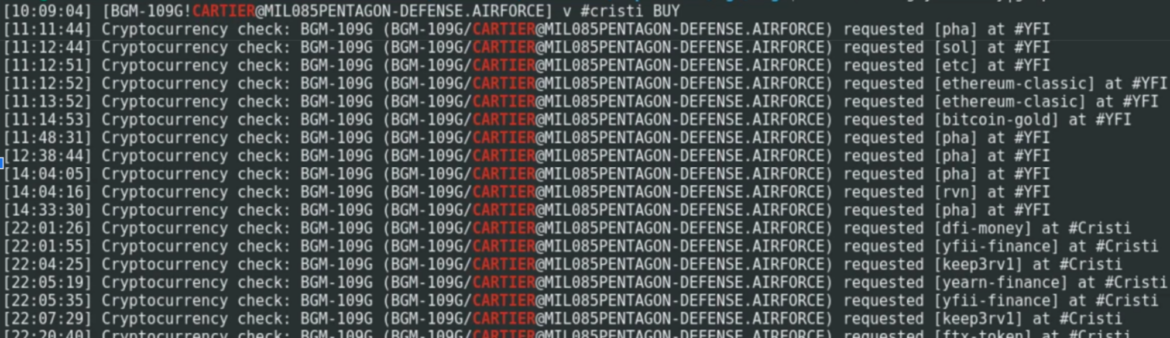
We've identified the user "dog" as the main malicious tool developer of the group, signing their tools with "Cartier" and "Kartier." We have also found direct evidence of tool developer, "Cartier," within the channel #Cristi, as shown below.
Dog's tool expertise is reflected in the way it instructs other members of the group how to set up and run the custom malicious tools. These malicious tools have been found in almost all of the campaigns we were targeted in. This list includes:
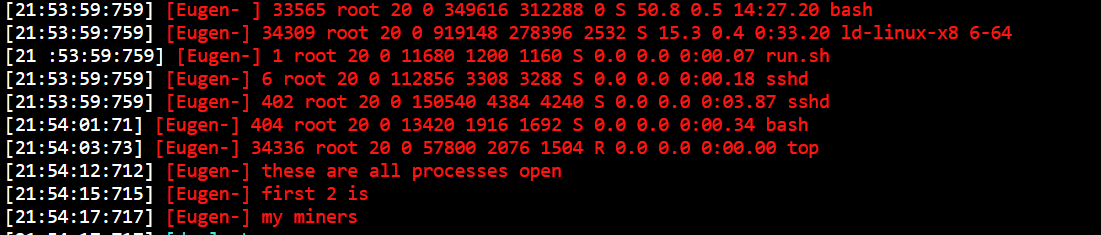
Here, user "Eugen" shows running miners, bash, and ld-linux-x8:
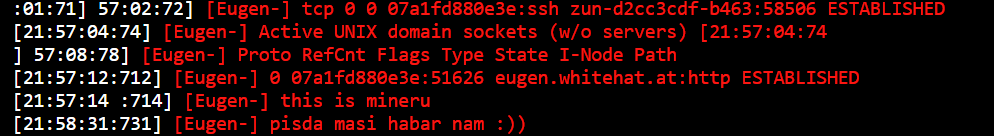
There is also a reference to malicious ELF "plm," observed multiple times in attacks against our honeypot and also reported in past campaigns:
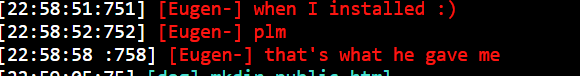
Below, there is an excerpt of how user "dog" is attempting to give access to user "Eugen" to a malicious domain containing a setup script for its infrastructure.
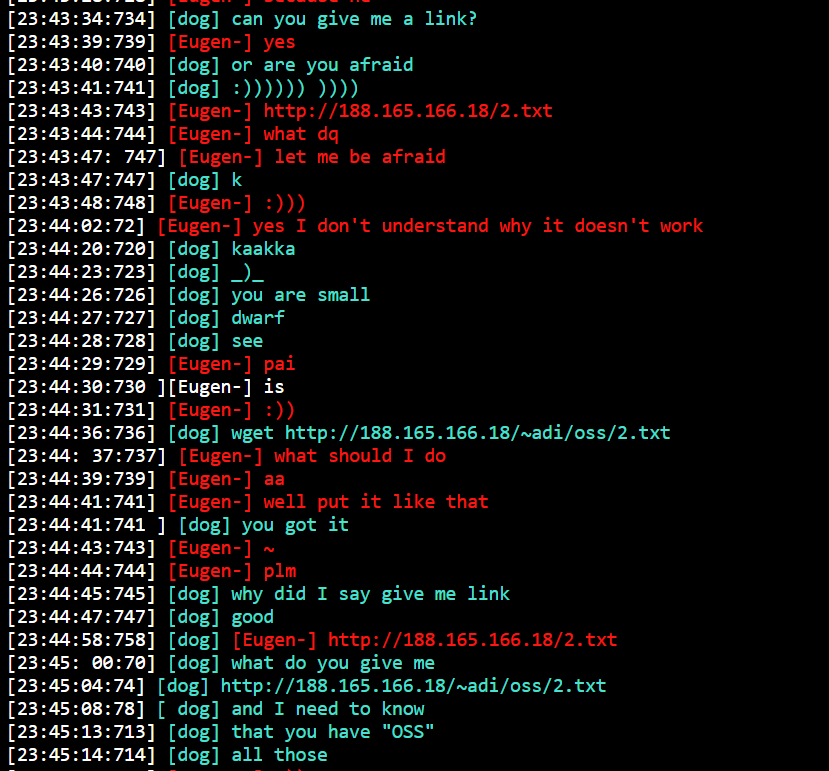
The IP above corresponds to a malicious indicator on VirusTotal, identified as malware.
There are also references to RUBYCARP's most commonly used tool, Mass Scanner (masscan), a tool omnipresent within its pre-exploitation activities and utilized to find new potential victims.
RUBYCARP's Motivations
Cryptomining
RUBYCARP uses its own pools for mining that are hosted on the same domains where it has created the IRC server to control the bots. These custom mining pools allow it to avoid detection from IP-based blocklists, and the usage of common and random ports provides another layer of stealth from simple detection systems. We've also discovered that it has not focused on a single cryptocurrency or mining tool but, instead, has several miners and wallets with activity. All the following IoCs are related to the "juice" threat actor.
Mining Pools:
- juicessh[.]space:443
- juicessh[.]space:4430
- juicessh[.]space:5332
- 91[.]208.206.118:443
- 194[.]163.141.243:4430
- sshd[.]baselinux[.]net
- run[.]psybnc[.]org:443
Known miners
- NanoMiner
- XMrig
Cryptocurrencies
- Monero
- Ethereum
- Ravencoin
The Ravencoin wallet has been particularly prolific. From a wallet checker, its total amount in USD would be over $22,800 received. The wallet has a large number of transactions associated with it and has been active since February 2022, and the last available transaction was mined on March 12, 2024.
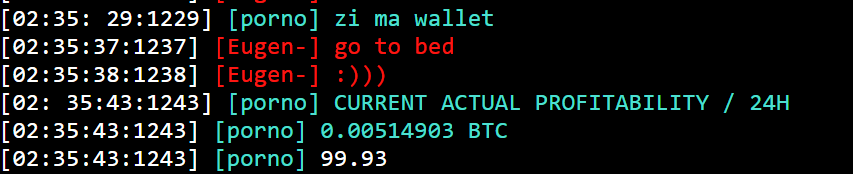
There are also several exchanges of wallet information among the members, in an attempt to show how much they have gained from these malicious campaigns. In the excerpt below, user "porno" claimed to have gained 0.00514903 BTC, around $360 USD, within 24 hours.
C3Bash
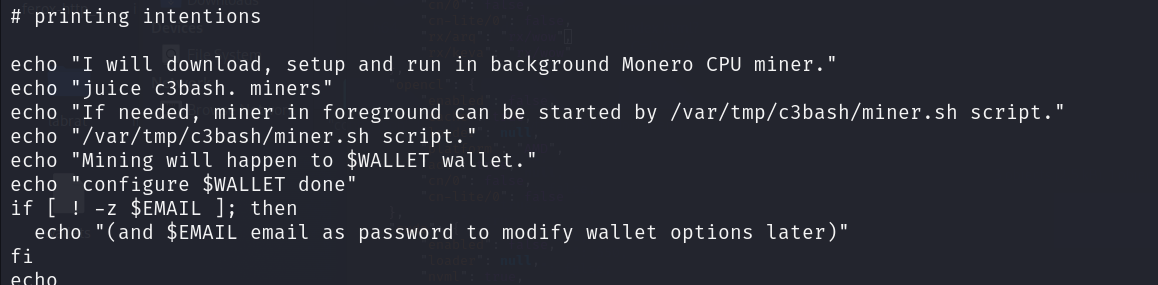
On top of the already known miners we observed above, we also encountered a custom command-line miner set up called simply "miner," which we named "C3Bash" due to the self-labeling we found. The script in question is signed by "Juice" and it allows a potential user to set up its wallet address with a command line argument, as well as any miner of choice.
Once the user has set up its configurations, the script takes care of downloading, installing, and running the miners in the background, also alerting the user if the script gets killed by an antivirus or simply removed. It also suggests what the CPU usage should be compared to the host, probably to avoid detection. On a victim device, this may result in the running of multiple miners at the same time, effectively reducing both the time it takes for the attacker to execute the malicious payload and the chances of it being detected, as the execution will now rely on a single script.
The script at the moment supports miners XMRig/Monero, and the script itself was hosted on a now-dead domain "download[.]c3bash[.]org."
Phishing
We found evidence that RUBYCARP also executes phishing operations to steal financially valuable assets, such as credit card numbers. Based on logs, it appears that it is using this to fund its infrastructure but it is reasonable to think RUBYCARP also uses these for other purposes, or possibly to sell.
In one of the attacks we received against our honeypot in December 2023, we identified a phishing template (letter.html) targeting Danish users and impersonating the Danish logistics company "Bring."
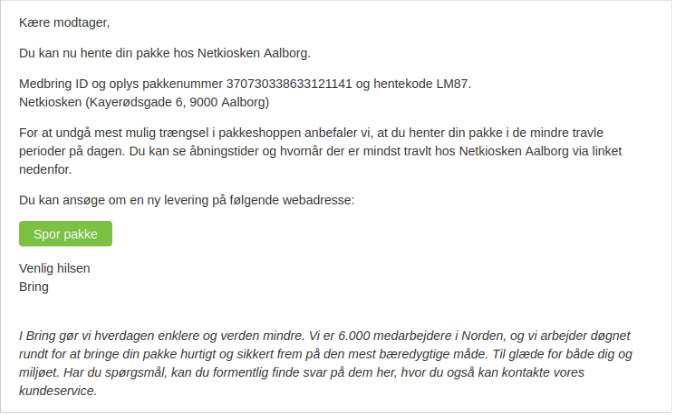
We also discovered a PHP script, named "ini.inc," used to send those phishing emails. An email.txt file was found that contained two potential compromised email accounts from which the attackers would send emails: "test@lufaros[.]com" and "maria@cenacop[.]com." At the time of this writing, the domain "lufaros[.]com" is marked as Malicious on VirusTotal.
Analyzing the shellbot code shows that it has specific commands to send emails, and it is likely that this is the template used in the campaigns:
sendraw($IRC_cur_socket, "PRIVMSG $printl :!u sendmail <subject> <sender> <recipient> <message>");We identified 36 text files containing hundreds of Danish email addresses, some of which were present in both old and recent data leaks. It is reasonable to think that the email addresses may have been the target of the phishing template shown above.
Within the same data, we also identified a Zip file named "remote_code.zip." Once extracted, the archive contains a logo image of the European bank Nets. Within the same folder, there are also SVG files containing an "ID Check" verification image and a Visa logo. More images were also found containing a mobile phone layout, as shown below, effectively emulating a Nets home banking application. These would be used to build a convincing phishing landing page.
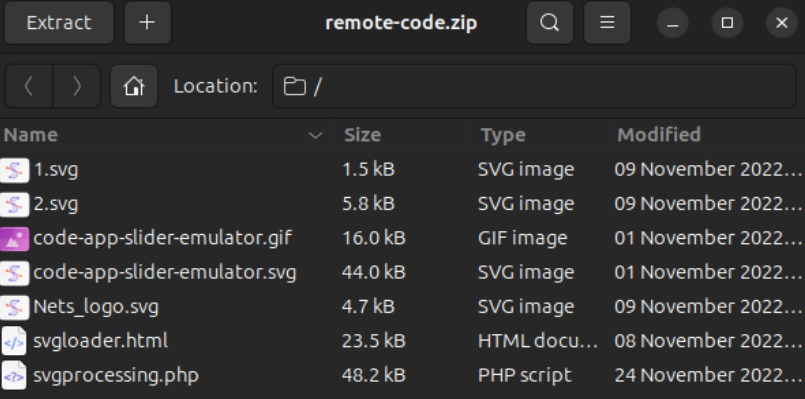

Archive content
Finally, we also found direct evidence of a new domain purchase. In an excerpt below, it is possible to see how the user "dog"/"cartier" is preparing to purchase a new potential domain with stolen credit card data.
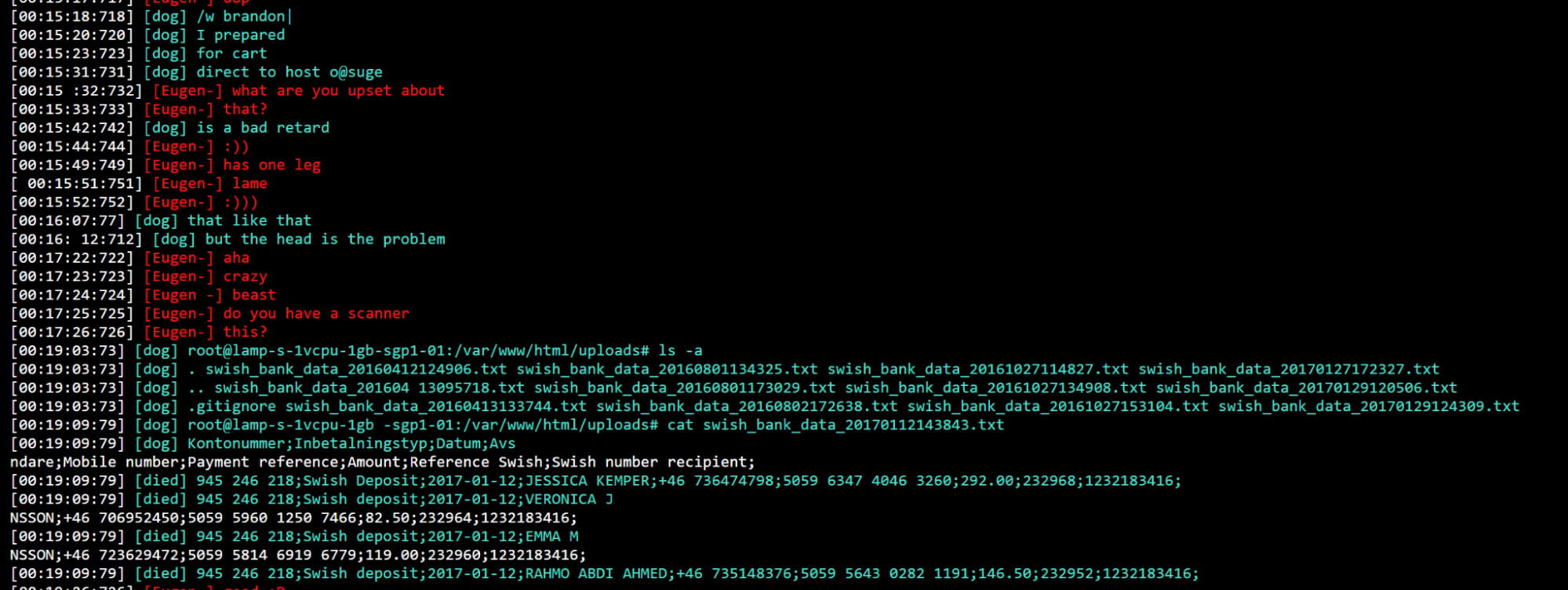
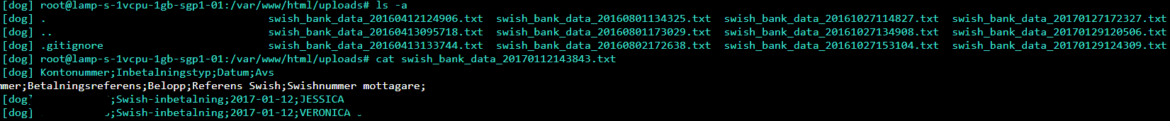
The screenshot above shows a conversation where user "dog" lists files which we believe it has stolen. The filenames seem a clear reference to Swedish bank Swish, and the timestamp in the filenames suggests they may have been stolen in 2016. "Dog" also provided credit card information to be used, presumably, by other members. These were printed in clear text within the channel, and have been redacted as they contained payment information.
Given the evidence above, it is plausible that the attackers may rely on phishing templates to collect payment information. It is safe to assume the phishing targets European entities, such as Swish Bank, Nets Bank, and Bring Logistics, among others.
Conclusion
RUBYCARP is a group of Romanian threat actors who have been active for almost a decade. Attribution is always difficult, but they are most likely Romanian and may have some crossover with the "Outlaw APT" group and others who leverage the Perl Shellbot. These threat actors are also involved in the development and sale of cyber weapons, which isn't very common. They have a large arsenal of tools they have built up over the years which gives them quite a range of flexibility when conducting their operations.
Communications between threat actors hasn't changed very much over the years, with IRC still being very popular. There is also a community aspect to RUBYCARP which is interesting, as they help mentor people who are new to the scene. This does provide some financial benefits to the group since it can then sell them the toolset that it has made.
While RUBYCARP targets known vulnerabilities and conducts brute force attacks, what makes it more dangerous is its post-exploitation tools and the breadth of its capabilities (i.e., Phishing). Defending against this group requires diligent vulnerability management, a robust security posture, and runtime threat detection.


