Check this out. What do you see?
I see a bat. Now check out this next one.
Aaarg, two seahorses me thinks matey!
And this must be Yogi Bear! You probably see something different. Some young folks at Carnegie Mellon University decided to use this property of psychology, unique to an individual, to create easy to remember complex passwords.
Whaaa you say?
Well, lets say I come up with an algorithm in my head to use certain characters from the words that popped in my head when I saw each of the above inkblots to form a password. Say, I use the first and last characters. The result would be “bttsyr”. Seems complex enough, no? Add a couple of more inkblots to your list and you can get a longer complex password.
Why, you say?
Yeah, seems a bit much doesn’t it? Sounded like a cool idea back in 2007, but over the years other researchers found plenty of holes using this concept. So for good reason, hopefully, no one is actually doing this to create their passwords.
Introducing SSO
We wanted to make your life a tad bit better by releasing Single Sign On (SSO) for Sysdig Monitor.
Our SSO solution provides support for the most common methods of SSO, across both our cloud offering and our on-premise software offering:
- Google Authentication
- SAML
- OpenID (Cloud)
Configuration
Based on the provider of your choice we will easily enable SAML and OpenID on your system. Find more details on how to configure SAML and OpenID.
Access
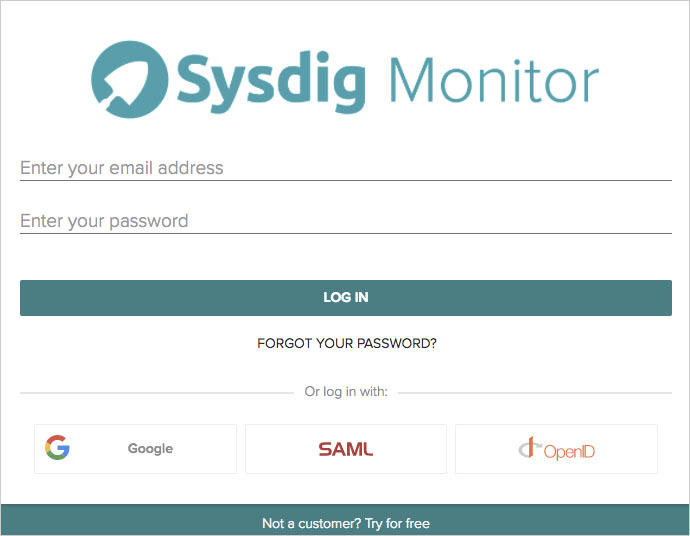
To access via Google Authentication, SAML or OpenID click on the respective icons as shown on the screen below:
Pricing & availability
SSO access to Sysdig Monitor with Google Authentication and SAML is available now across all tiers of Cloud and On Premise. Currently, the OpenID offering is limited to our Cloud solution. There is no change to our base pricing.