Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

Welcome to another monthly update on what's new from Sysdig. Our team continues to work hard to bring great new features to all of our customers, automatically and for free! First and foremost, Happy New Year, Voorspoedige nuwe jaar, Gelukkig nieuwjaar, عام سعيد, bon any nou, godt nytår, bonne année, Frohes neues Jahr, felice anno nuovo, שנה טובה, あけまして おめでとう ございます, laimīgu Jauno gadu, szczęśliwego nowego roku, С Новым Годом, and blwyddyn newydd dda! It seems like a cliché now to mention what a terrible year 2020 was for most of us, but it really was difficult. From all of us at Sysdig, here's hoping 2021 brings you luck, fortune, happiness, and success (and any other positive outcomes you may desire)!This month sees the launch of our always-popular fourth annual Sysdig container security and usage report, which looks at how global Sysdig customers of all sizes and industries are using and securing container environments. This real-world data provides insights about security risks, container utilization, and services used from nearly 1 billion unique containers that our customers have been running over the past year.In this report, you will learn:
- That shifting left is not enough. You also need runtime security.
- How much the new container runtimes and registries are increasing in popularity.
- Which open-source tools and standards are on the rise.
Download this report to see how your organization stacks up when it comes to securing and using containers over the past year.As always, please go check out our own Release Notes for more details on product updates, and ping your local Sysdig contact if you have questions about anything covered in here.
Sysdig Secure
Event Forwarding Runtime Policies
The JSON format for runtime policy events has been upgraded to include full scope information, rule labels, and a single-line representation for the event field's keys and values.To preserve backwards compatibility with existing integrations, the old JSON format is still available (and used by default on migration).From the Event Forwarder page, under "Data to Send," the old JSON format is labeled "Policy Events (Legacy)" and the new one as "Runtime Policy Events."
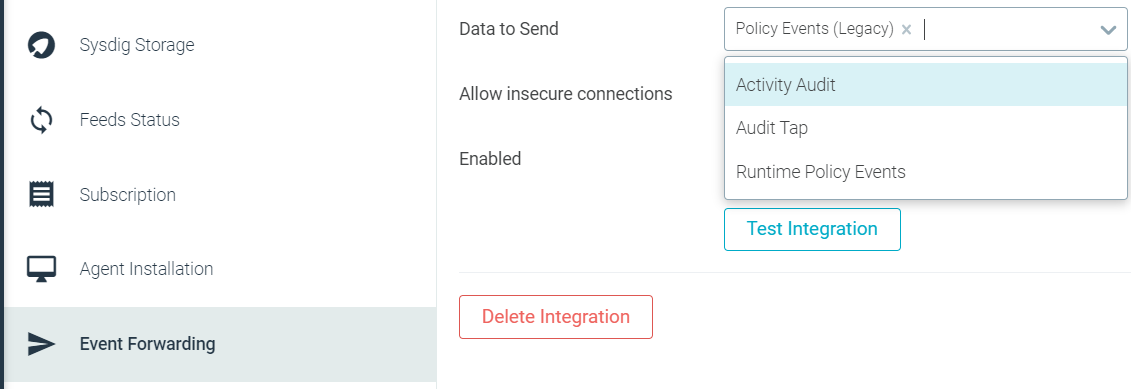
Also see Event Forwarding.
Sysdig Monitor
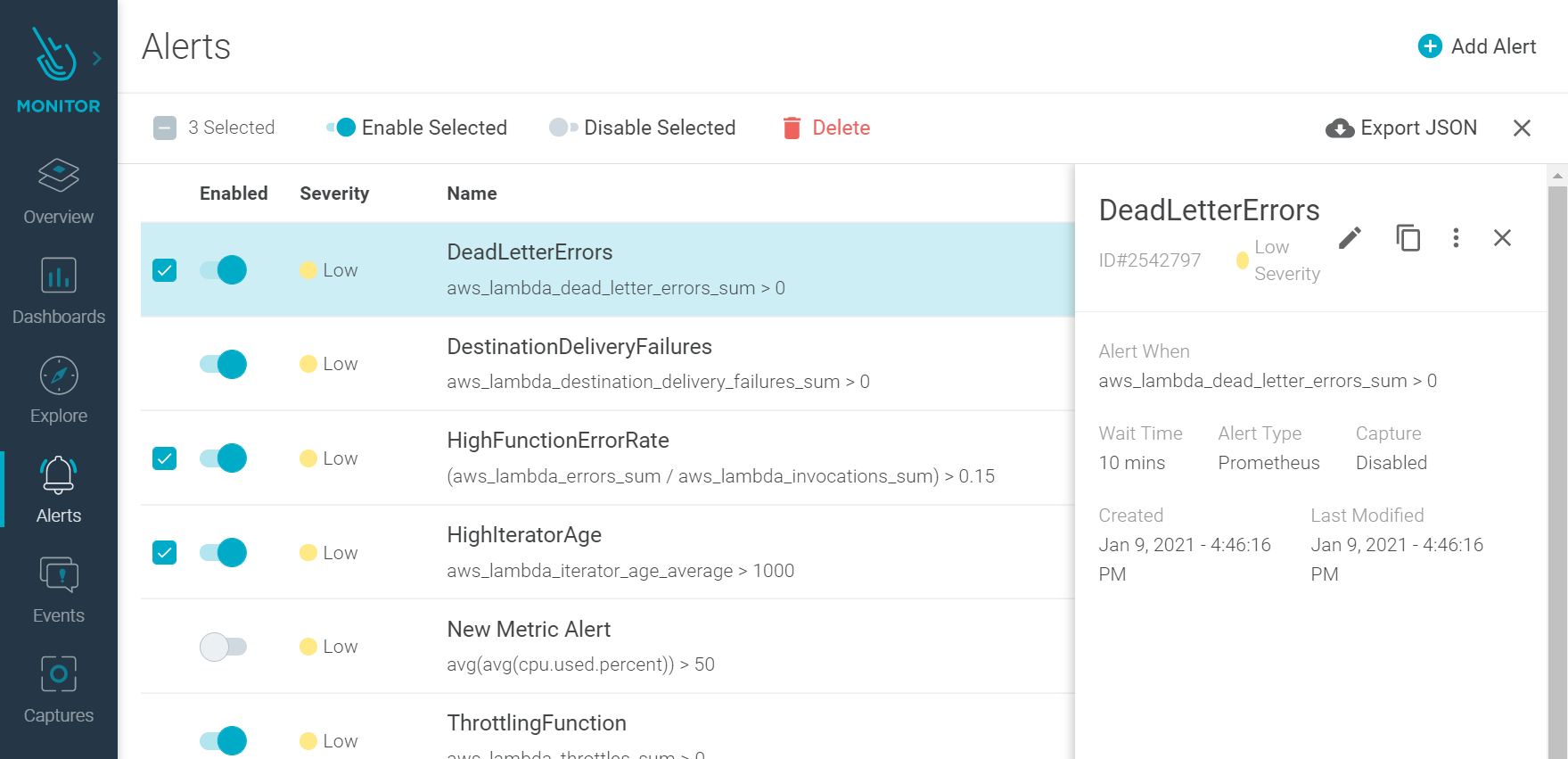
Improved Alerts
The Alert interface has been improved to allow faster browsing and easier management. For more information, see Alerts.
Prometheus Staleness Markers
The importance of this feature is that no-data conditions for Prometheus metrics will be detected faster, as we previously extended the time series artificially for five minutes. You can read more about staleness markers in this article.What does this mean?
- PromQL panels will no longer show the artificially-extended missing data for five minutes, but will do so much faster (usually after two scrape periods).
- PromQL alerts for no-data will no longer be late for five minutes by default.
Please note that you can catch the Prometheus no-data condition and alert on it by using the absent() function.
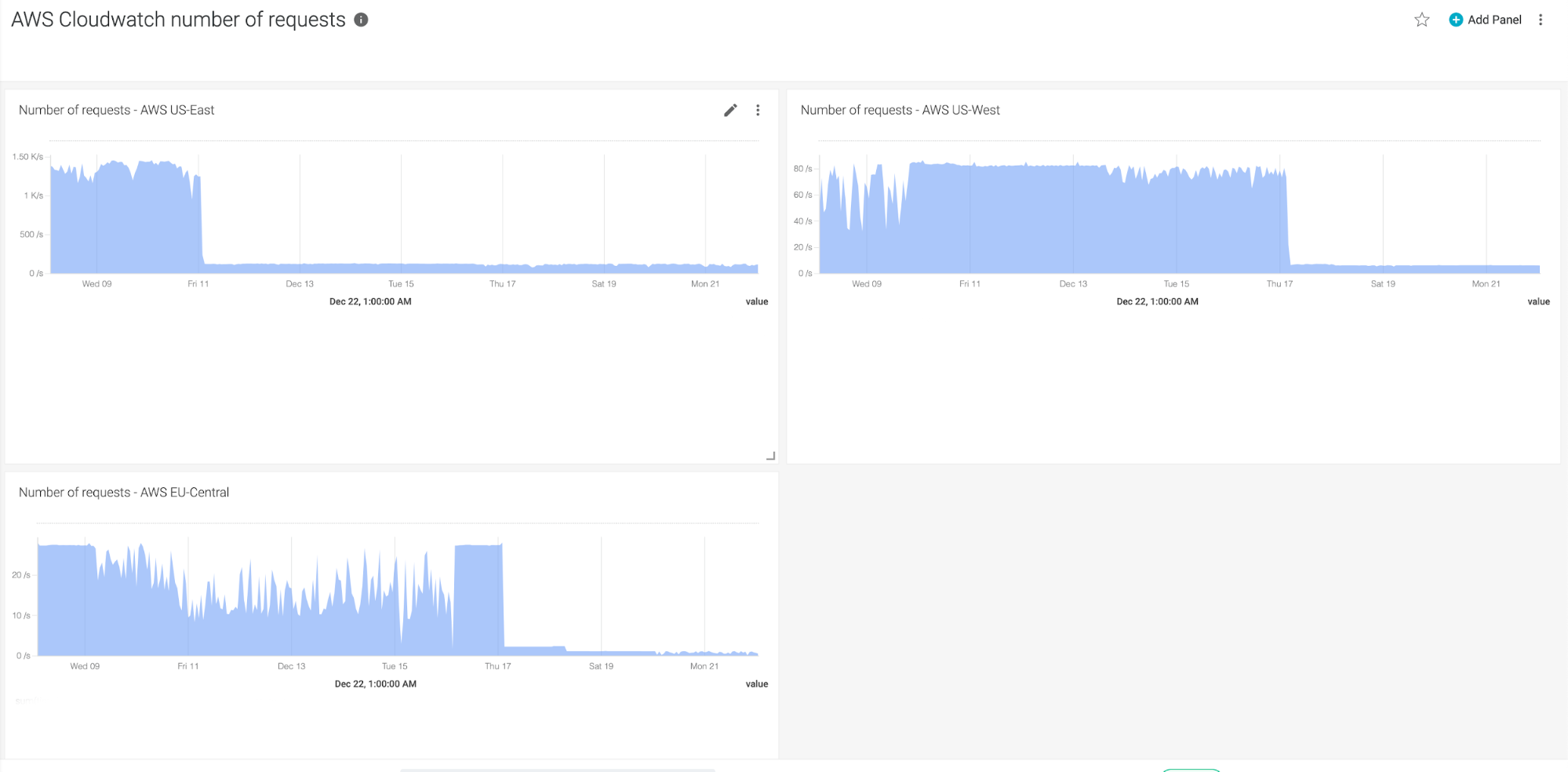
CloudWatch improvements
On the surface, this is a minor change that brings no feature impacts, but it can have a big impact on efficiency. We made some changes to the way we do our CloudWatch integrations, which makes it much more efficient, greatly reducing the number of API calls used. For some customers, this should mean a reduction in the cost associated with CloudWatch and API calls.
Sysdig Agents
Sysdig Agent
The latest Sysdig Agent release is 10.9.0. Below is a diff of updates since 10.8.0, which we covered in our last update.
New Features & Enhancements
- Support for Kubernetes CronJobs: Kubernetes CronJobs are supported when reporting network communications.
Fixes
- Runtime Policies and Rules Are Loaded with No Errors: Fixed a race condition that could prevent runtime policies and rules from being loaded properly if multiple messages from the Sysdig backend are received consecutively.
- Cluster Overview Displays Compliance Score: Fixed an issue where Statsd metrics related to compliance would have no associated Kubernetes metadata and were not visible on Cluster Overview.
Helm Chart
The Helm Chart 1.11.3 has been released. The following is a diff of changes since 1.11.1 which we covered last month.
Changes
- Used the latest image from Agent (10.9.0).
- Used the latest image from Node Image Analyzer (0.1.7).
- Allowed for customization of liveness and readiness probes initial delay.
Node Image Analyzer
Version 0.1.7 was released last month and is still the latest version available.Node image analyzer can be installed as part of the Sysdig Agent install.
Inline Scanning Engine
Version 2.2 is still the latest version.Also see: Integrate with CI/CD Tools.
SDK, CLI and Tools
Sysdig CLI
v0.7.4 was released and includes the following diff updates from v0.7.0:
Bug fixes
- Check new NC IDs when restoring alerts.
- Added missing import.
- Updated dependencies.
- A list of images is returned instead of only one image.
- Do not break the restore on missing fields.
Python SDK
v0.14.13 has been released. Listed below are the diff changes from v0.14.7 which we covered last month:
Bug Fixes
- Updated dashboards to the latest API
- Solved v2 events not scoping created events.
- Increased limit to retrieve policy events without pagination.
Documentation
- Updated
download_dashboardsexample andget_dashboardsdocumentation - Added some structure to documentation.
- Added
readthedocs.ymlto build docs. - Updated docs for readthedocs.
- Enhanced documentation.
Terraform Provider
v0.5.10 has been released, and the following are the diff changes from v0.5.6 which we covered last month:
New Features
- New resource: sysdig_secure_vulnerability_exception_list. Creates a Sysdig Secure Vulnerability Exception list that will hold all of the vulnerability exceptions.
- New resource: sysdig_secure_vulnerability_exception. Creates a Sysdig Secure Vulnerability Exception.
- New data source: sysdig_user. Retrieves information about a user from their email.
- Added support for "text" panel types for Dashboard resources. See example in the official documentation.
- Added custom notification config for Monitor alerts. See the documentation.
- Import resources: Terraform is able to import existing infrastructure. This allows you to take resources you've created by some other means and bring it under Terraform management.
- Increased timeout for Lists, Macros and Rules from 30 seconds to five minutes.
- Added retry strategy to the API HTTP client with backoff, so rate limiting problems could be more easily avoided.
Bug Fixes
- Solved a crash when importing dashboard with unsupported panel types and query types.
- Solved fields not correctly set. Some fields weren't being correctly set when retrieved from the API, like:
severityin allsysdig_monitor_alert_*resources.can_see_infrastructure_eventsinsysdig_monitor_team.can_use_aws_datainsysdig_monitor_team.severityinsysdig_secure_policy.- Also,
tcp.portsandudp.portsinsysdig_secure_rule_networkweren't being created correctly in the backend, thus, creating a network rule with no checked ports.
Falco vs. Code Extension
v0.1.0 is still the latest release.
Sysdig Cloud Connector
v0.4.4 was released. Listed below is a diff of updates since v0.4.0, which we covered last month:
Features
- Disabled noisy rules.
- Added a rule to detect AWS Cloud Shell environment creation.
- Added a guide to deploy on GCP.
Bug Fixes
- Made sure alerts are sorted before sending to CloudWatch.
Sysdig Secure Inline Scan for Github Actions
v3 is still the latest version.
Sysdig Secure Jenkins Plugin
v2.1 was released since our last update, and brings a couple of changes:
- Sysdig Jenkins Plugin 2.1 leverages the inline scanner v2 under the hood, which improves the scanning performance and execution times.
- This version also introduces proxy support for both master and worker nodes.
New Website Resources
Blogs
- Falco vs. AuditD from the HIDS perspective
- Sysdig 2021 container security and usage report: Shifting left is not enough
- Stackrox Acquisition: The Race to Secure Containers
- 5 Best practices for ensuring secure container images
- Detect CVE-2020-8554 using Falco
- Cooking the perfect holiday ham with IoT, Prometheus, and you
Webinars
- Container Security Best Practices: Forensics & Incident Response
- Kubernetes 1.20: Straight talk from the release team
- Kubernetes Attacks: What your cluster is trying to tell you
- Container Security Best Practices on Azure Kubernetes Service (AKS)
- Accelerate your FedRAMP journey for container security with Anitian & Sysdig


