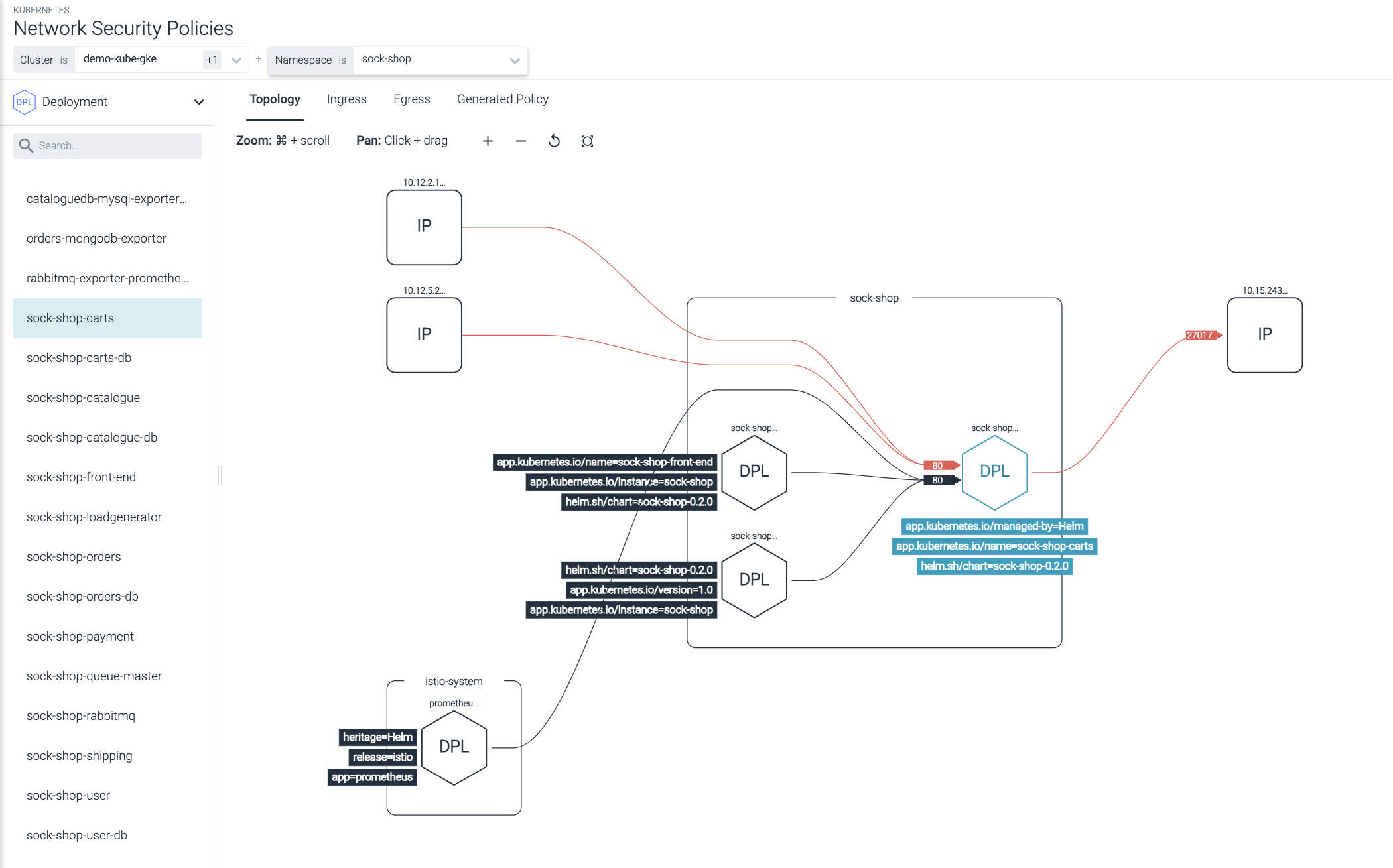
Kubernetes Network Security
Secure Kubernetes networks with automated microsegmentation. See and audit all communications between pods, services, and applications.
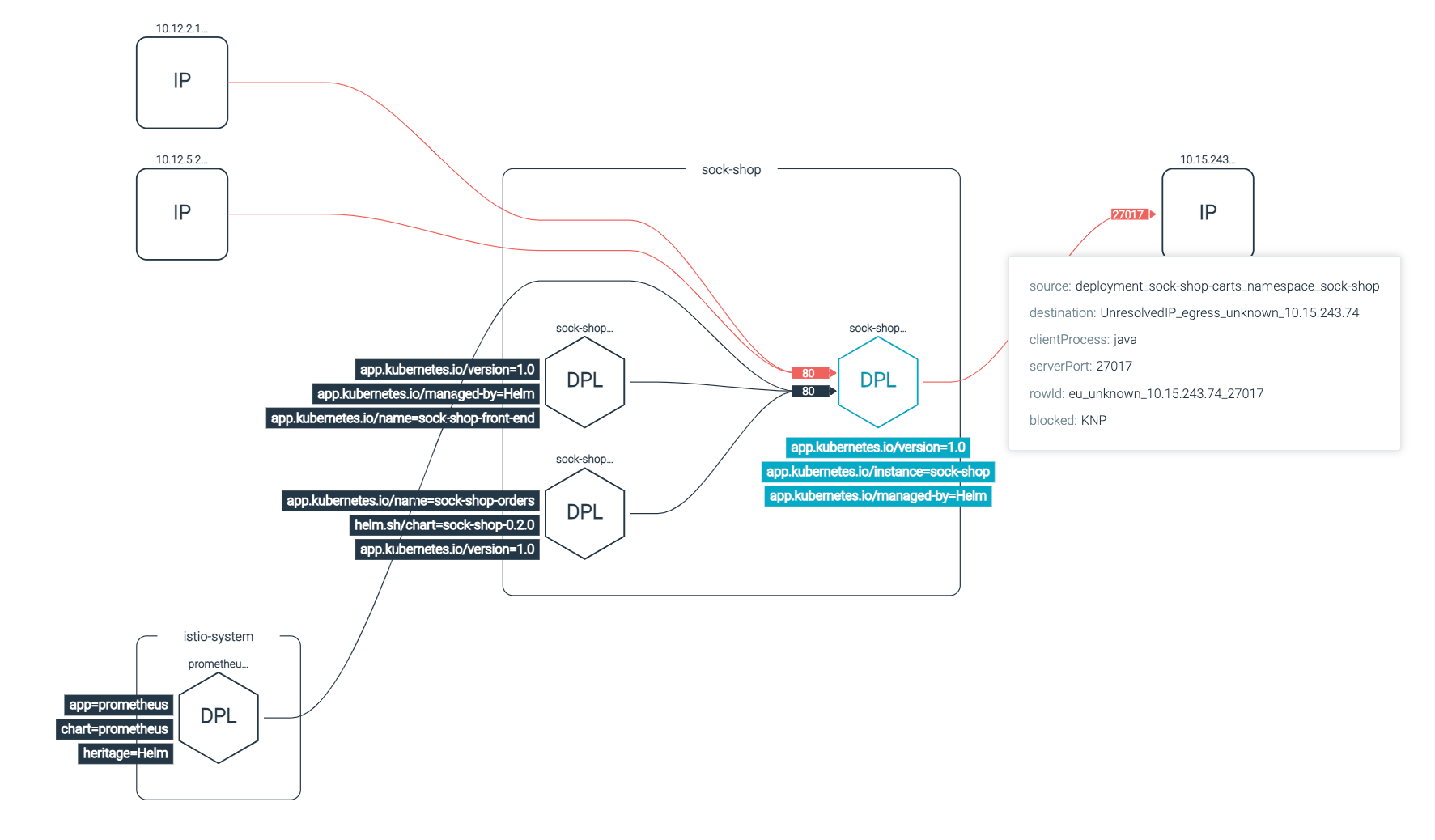
Prevent Lateral Movement in Kubernetes
Enforce microsegmentation and stop lateral movement threats with a cloud-native network security tool like Sysdig Secure.
Kubernetes Network Monitoring
See all network activity in and out of a particular pod, service, or application. Investigate suspicious traffic and connection attempts.
Kubernetes-Native Microsegmentation
Enable microsegmentation using Kubernetes cloud-native network policies with rich context. Apply Kubernetes network security without breaking the application.
Automated Network Policies
Save time by automating Kubernetes network policies. Use a simple graphical software interface to modify policies without manually changing the YAML.
The Sysdig Secure DevOps platform not only provides the underpinnings of a cloud-native system, but also serves as the point where all container security begins.
Yoshihiko Ishikawa, Group 1, Department of Middleware 2, IT Engineering Division, SCSK2
Kubernetes-Native Network Security
featured resources