
Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

In this blog post you'll learn how to set up image vulnerability scanning for AWS CodePipeline and AWS CodeBuild using the Sysdig Platform.
\r\r
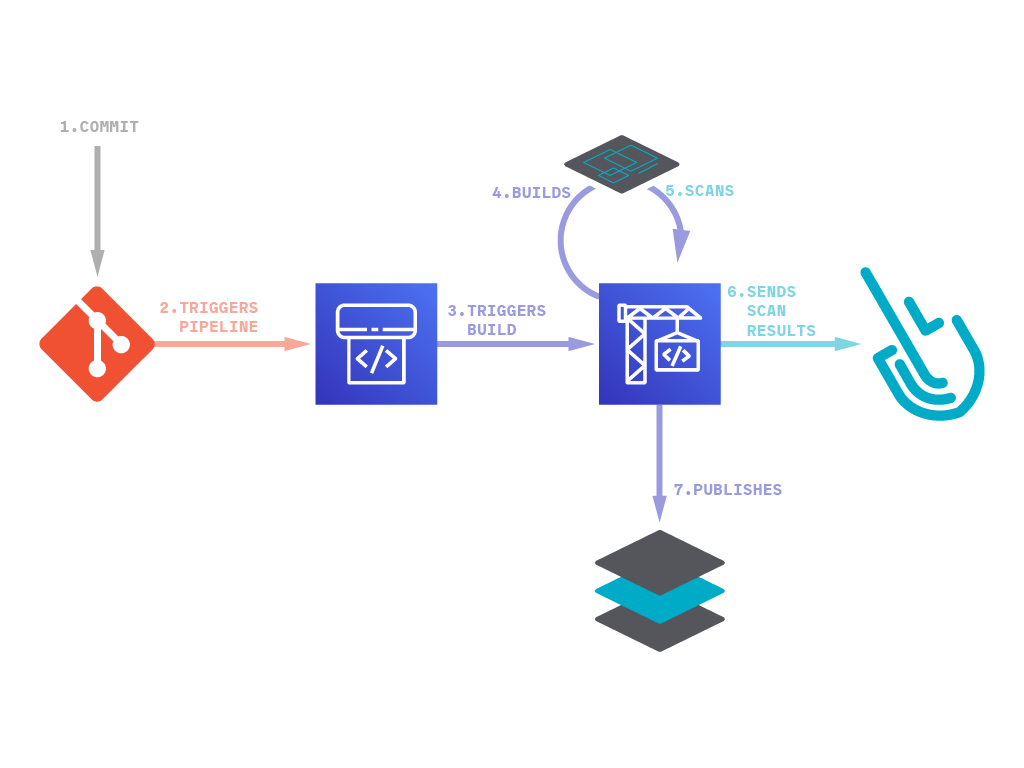
AWS provides several tools for DevOps teams: CodeCommit for version control, CodeBuild for building and testing code, and CodeDeploy for automatic code deployment. The block on top of all these tools is CodePipeline that allows them to visualize and automate these different stages.
\r\r
Image Scanning for AWS CodePipeline raises the confidence that DevOps teams have in the security of their deployments, detecting known vulnerabilities and validating container build configuration early in their pipelines. By detecting those issues before the images are published into a container registry (like Amazon Elastic Container Registry) or deployed in production, fixes can be applied faster, improving delivery to production time.
\r\r
The process of scanning images with Sysdig includes:
\r\r
Analyzing the Dockerfile and image metadata to detect security sensitive configurations, such as:
\r\r
- \r
- Running as privileged (root) user, without the
USERcommand. \r - Using images tagged as
latest, rather than specific versions with full traceability. \r - Exposing insecure ports. \r
- Not using the
HEALTHCHECKinstruction. \r - Many other configurable Dockerfile checks. \r
\r\r
Checking software packages against well-known vulnerabilities databases:
\r\r
- \r
- OS packages. \r
- Third party libraries that our application makes use of, such as Python pip, Ruby gems, Node npm, Java jars, etc. \r
\r\r
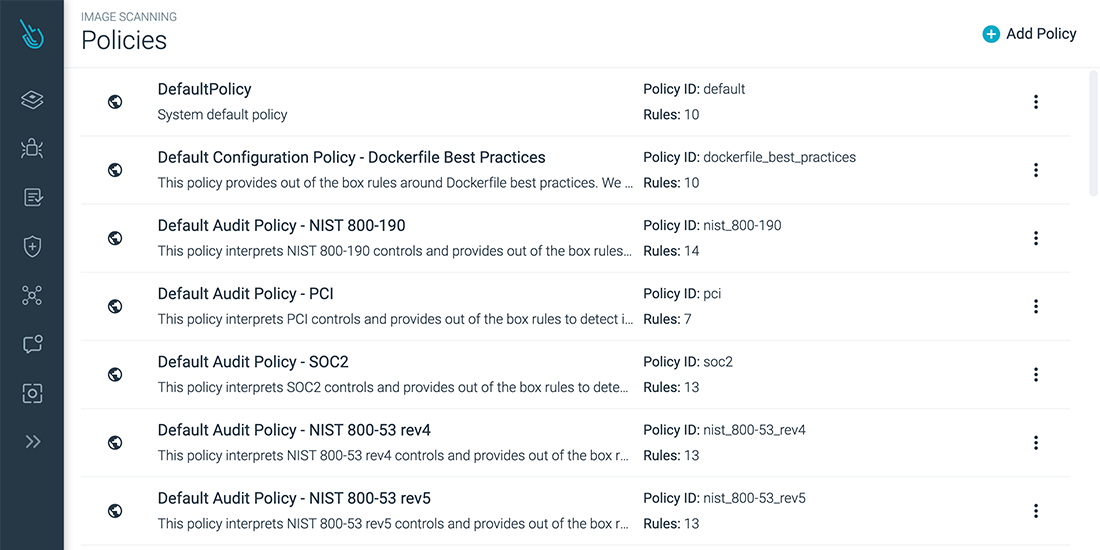
And user-defined policies or compliance requirements that you want to check for every image, such as:
\r\r
- \r
- Software packages blacklists. \r
- Base images whitelists. \r
- Image scanning parameters that match with the NIST 800-190 or PCI compliance lists. \r
\r\r
Using Sysdig's local scanning, you won't lose control over your images as they don't need to be sent to the backend or exposed to a staging repository. After the image is built, it will be scanned in the same node where you run your pipeline, and only the scanning results will be sent to the Sysdig Secure backend, whether it be our SaaS or your self-hosted instance.
\r\r
Planning AWS CodePipeline and CodeBuild for vulnerability scanning
\r\r
AWS provides a CI/CD DevOps platform where you can create pipelines that will be automatically executed when an event of our choosing occurs. The most common events used to trigger pipelines are new commits pushed to a code repository.
\r\r
\r\r
The AWS CodePipeline in this article will be invoked after a commit is pushed to a GitHub repository. The Pipeline will then use AWS CodeBuild to build the repository code into an image, then push the image to a registry like ECR where it can be deployed into Kubernetes.
\r\r
Building the AWS CodePipeline and CodeBuild infrastructure
\r\r
In search of simplicity, all the infrastructure needed for this example is defined as code and can be recreated using Terraform manifests, available in our inline-scan-aws-infrarepository.
\r\r
The Terraform manifests define one AWS CodeBuild project that we'll later set up for building and scanning our image.
\r\r
They also define one AWS CodePipeline configured to:
\r\r
- \r
- Retrieve the code from GitHub and save it in an AWS S3 Bucket. \r
- Invoke the execution of the AWS CodeBuild project. \r
\r\r
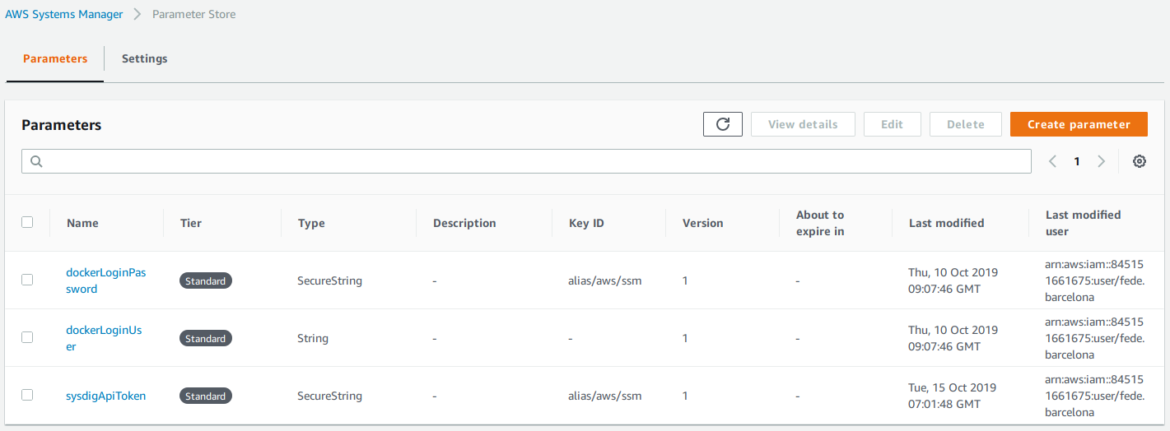
And finally, they'll store the credentials for the image registry and the Sysdig Secure API token in the AWS Parameter Store, which is the recommended way to handle secrets to avoid leaks.
\r\r
Create those by running:
\r\rterraform apply\r
\r\r
Check further configuration details in the repository documentation.
\r\r
AWS CodeBuild YAML definition for Inline Scanning with Sysdig Secure
\r\r
Once the infrastructure is created, we can start setting up the building process. The steps for our build are:
\r\r
- \r
- Install and execute Docker. \r
- Login into DockerHub and pull Sysdig's image for inline scanning. \r
- Build the image from the downloaded code. \r
- Scan the new image and send the results to Sysdig Secure. \r
- Publish the image to the registry if it passes the scan. \r
\r\r
AWS CodeBuild will perform the steps defined in a buildspec.yml file, inside the root path of our code repository:
\r\rversion: 0.2\r
env:\r
variables:\r
IMAGE_NAME: "sysdiglabs/dummy-vuln-app:latest"\r
SCAN_IMAGE_NAME: "sysdiglabs/secure-inline-scan:latest"\r
parameter-store:\r
DOCKER_LOGIN_USER: dockerLoginUser\r
DOCKER_LOGIN_PASSWORD: dockerLoginPassword\r
SYSDIG_SECURE_TOKEN: sysdigApiToken\r
phases:\r
install:\r
runtime-versions:\r
docker: 18\r
commands:\r
- nohup /usr/local/bin/dockerd --host=unix:///var/run/docker.sock --host=tcp://127.0.0.1:2375 --storage-driver=overlay2&\r
- timeout 15 sh -c "until docker info; do echo .; sleep 1; done" \r
pre_build:\r
commands:\r
- docker login -u $DOCKER_LOGIN_USER -p $DOCKER_LOGIN_PASSWORD\r
- docker pull $SCAN_IMAGE_NAME\r
build:\r
commands:\r
- docker build . -t $IMAGE_NAME\r
post_build:\r
commands:\r
- docker run --rm -v /var/run/docker.sock:/var/run/docker.sock $SCAN_IMAGE_NAME /bin/inline_scan analyze -s https://secure.sysdig.com -k $SYSDIG_SECURE_TOKEN $IMAGE_NAME\r
- docker push $IMAGE_NAME\r
\r\r
Let's break it down.
\r\renv:\r
variables:\r
IMAGE_NAME: "sysdiglabs/dummy-vuln-app:latest"\r
SCAN_IMAGE_NAME: "sysdiglabs/secure-inline-scan:latest"\r
parameter-store:\r
DOCKER_LOGIN_USER: dockerLoginUser\r
DOCKER_LOGIN_PASSWORD: dockerLoginPassword\r
SYSDIG_SECURE_TOKEN: sysdigApiToken\r
\r\r
First we are going to define environment variables for our pipeline:
\r\r
- \r
IMAGE_NAME: the name of the image we are going to build and scan. \rSCAN_IMAGE_NAME: the name of the image that contains the inline scanning script. \rDOCKER_LOGIN_USERandDOCKER_LOGIN_PASSWORD: the DockerHub credentials we need to push the image to the repository. As these credentials must not be publicly available, we will save them in the AWS Parameter Store. These parameters were created by Terraform in the previous section. \rSYSDIG_SECURE_TOKEN: the token from Sysdig Secure so we can send the results from the scans. This token must be saved as a credential as well, and it will be referenced from the Parameter Store. The parameter was created using the Terraform manifests. \r
\r\r
\r\r
We save the sensitive credentials in the AWS Systems Manager > Parameter Store using the Terraform manifests.
\r\r
Now we define the actual build, the steps to execute when there's a new commit:
\r\rinstall:\r
runtime-versions:\r
docker: 18\r
commands:\r
- nohup /usr/local/bin/dockerd --host=unix:///var/run/docker.sock --host=tcp://127.0.0.1:2375 --storage-driver=overlay2&\r
- timeout 15 sh -c "until docker info; do echo .; sleep 1; done" \r
\r\r
The pipeline will ensure we have Docker 18 installed in the runner. The runner will start Docker as a daemon and wait until it's running.
\r\rpre_build:\r
commands:\r
- docker login -u $DOCKER_LOGIN_USER -p $DOCKER_LOGIN_PASSWORD\r
- docker pull $SCAN_IMAGE_NAME\r
\r\r
Before building the image, it will log into the Docker registry and pull the image with the inline scanning script.
\r\rbuild:\r
commands:\r
- docker build . -t $IMAGE_NAME\r
\r\r
Then, the runner will build one image using the Dockerfile in the git repository.
\r\rpost_build:\r
commands:\r
- docker run --rm -v /var/run/docker.sock:/var/run/docker.sock $SCAN_IMAGE_NAME /bin/inline_scan analyze -s https://secure.sysdig.com -k $SYSDIG_SECURE_TOKEN $IMAGE_NAME\r
- docker push $IMAGE_NAME\r
\r\r
The scanning tool will perform the scan within the runner in the same machine where the image was built, all without the container image ever leaving your AWS account.
\r\r
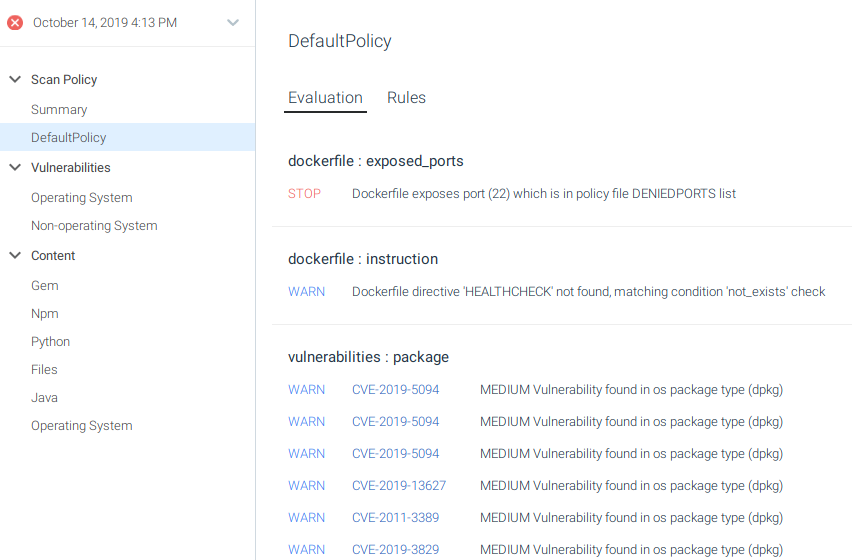
Within Sysdig Secure, we can configure multiple scanning policies with different checks to define what is considered dangerous and should be warned or blocked.
\r\r
\r\r
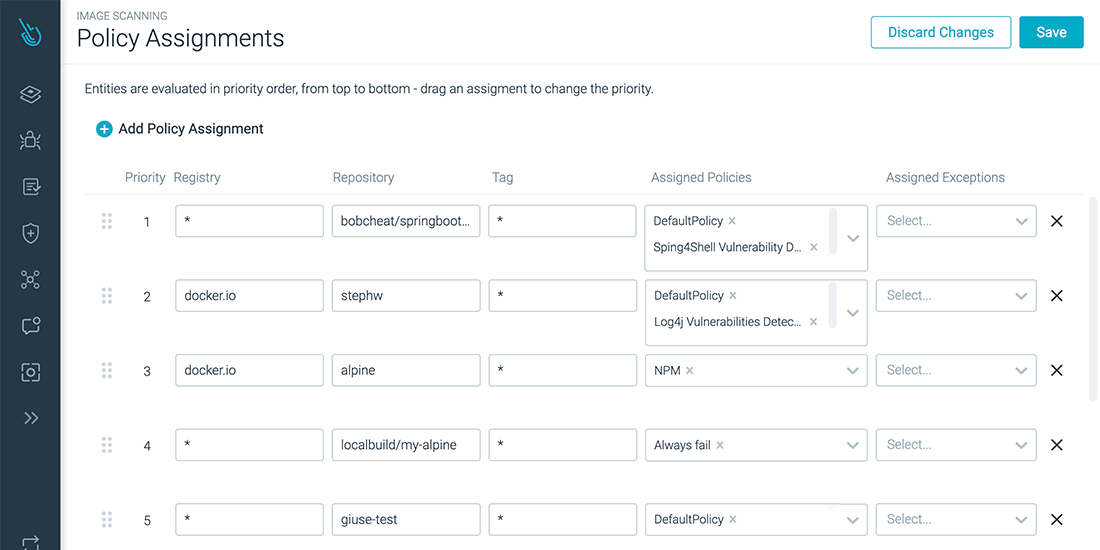
Assigning scanning policies for our image is as easy as linking the registry, repository, or tag to a policy.
\r\r
\r\r
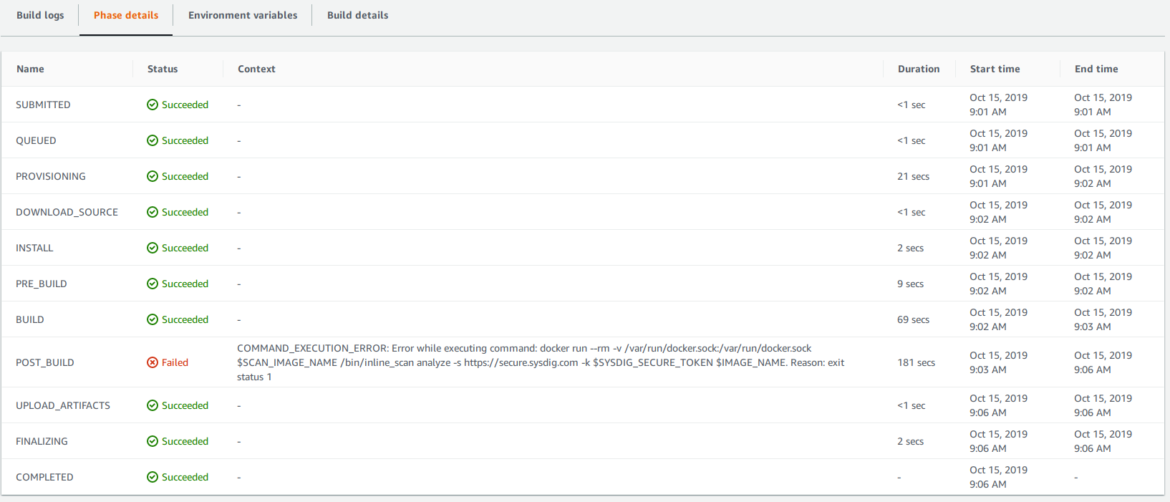
If the inline_scan script finds any STOP condition from our scanning policy, the script will be aborted with a return code different from 0, and the pipeline execution will be considered as FAILED. Then, the execution of the pipeline will end here.
\r\r
However, if everything is correct and the image passes the scan, the pipeline will continue and we will push the image to the Docker Registry.
\r\r
Let's execute the pipeline and see it in action!
\r\r
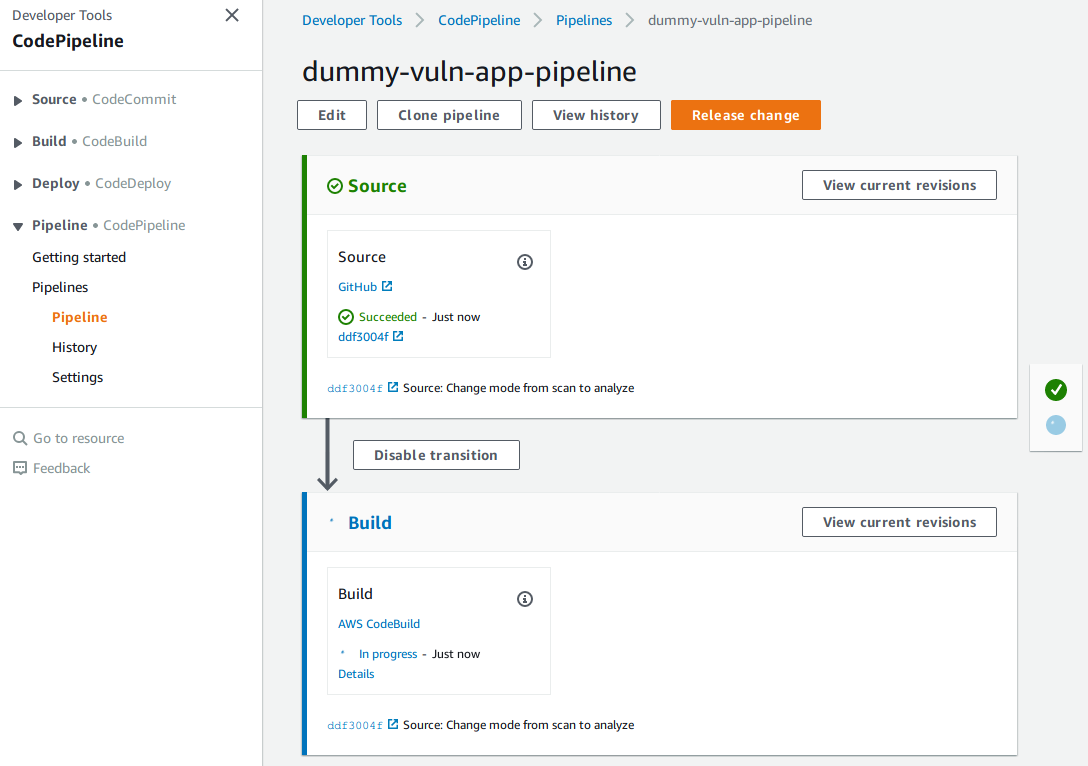
\r\r
Here are the results of the pipeline. Uh-oh! Something went wrong:
\r\r
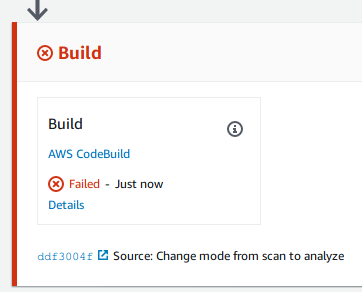
\r\r
If we navigate into Details and open the Execution details, we will see the CodeBuild execution that failed.
\r\r
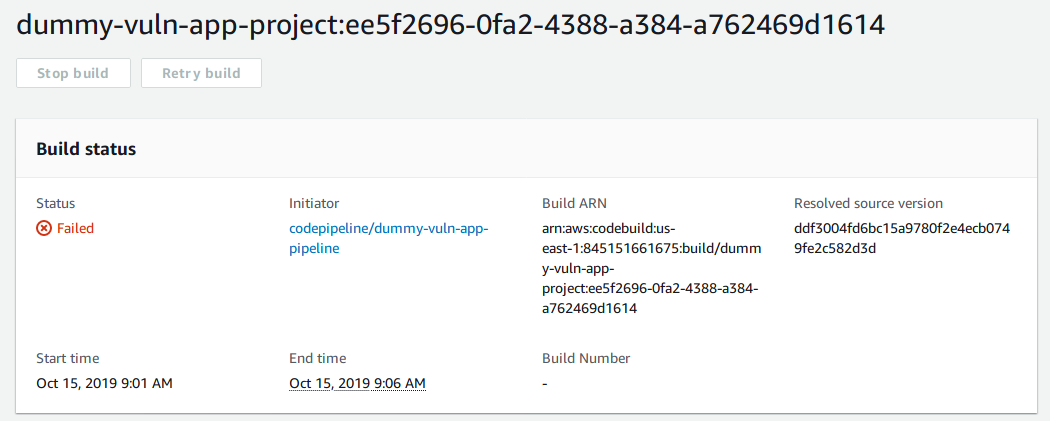
\r\r
Inside the Phase details tab we can see how it failed in the POST_BUILD stage. We can also identify the last command executed, which is the one that generated the error.
\r\r
\r\r
Let's check the full information in Sysdig Secure.
\r\r
Image scanning results in Sysdig Secure
\r\r
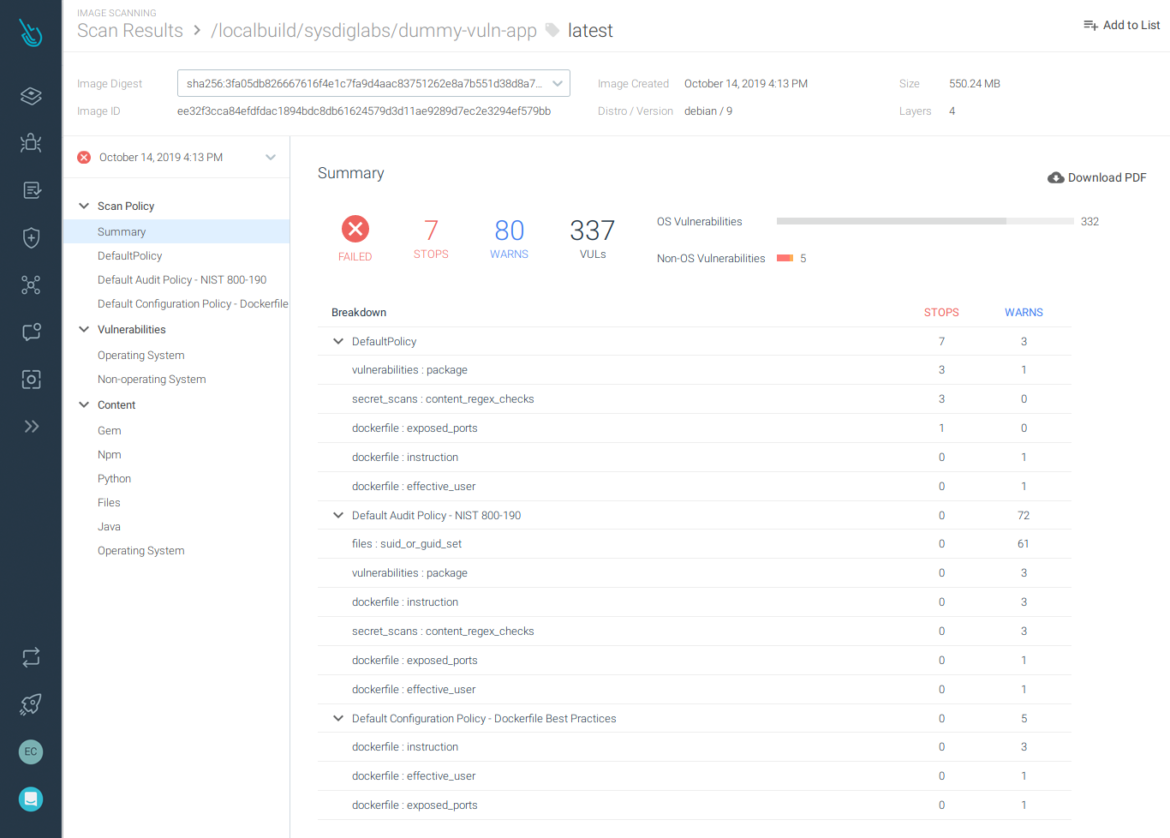
The image will be scanned in the local machine, but the results will be sent to Sysdig Secure for further analysis and we will be able to download the full report:
\r\r
\r\r
We can see that:
\r\r
- \r
- The Dockerfile exposes the port 22. \r
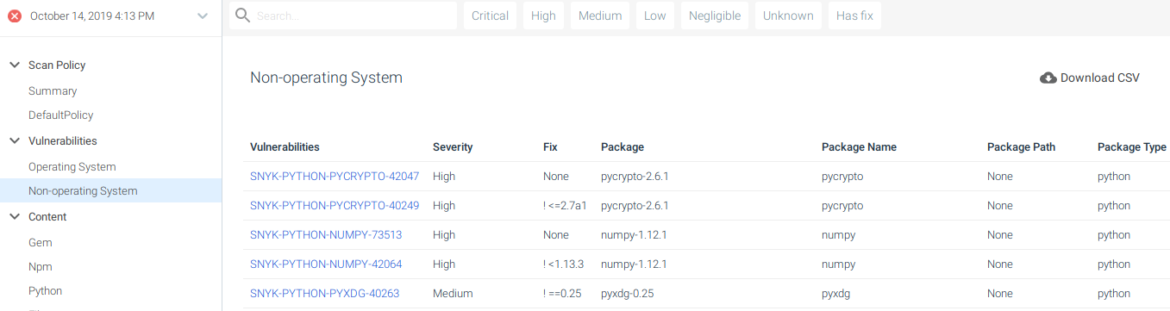
- There are some non-OS packages for Python that contain HIGH and CRITICAL-rated vulnerabilities. \r
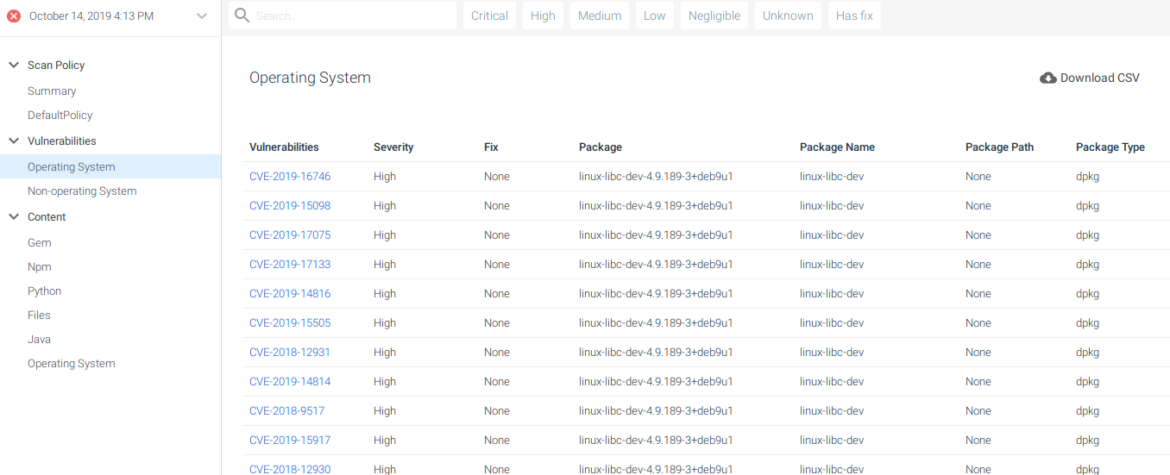
- The OS package linux-libc-dev contains some HIGH-rated vulnerabilities. \r
\r\r
\r\r
Exposed port 22 is a STOP condition in the scan results.
\r\r
\r\r
Operating system vulnerabilities found in the image.
\r\r
\r\r
Non-operating system vulnerabilities, from libraries that our software makes use of.
\r\r
Sysdig Secure provides more features that enhance the security of your DevOps workflow:
\r\r
- \r
- Trigger alerts when there's a new image being pushed in the repository, either a new or an overwritten tag. \r
- Reevaluate policies if they change against existing scanning metadata and notify if the results change. \r
- Notify if there's a new CVE that affects any existing image. \r
\r\r
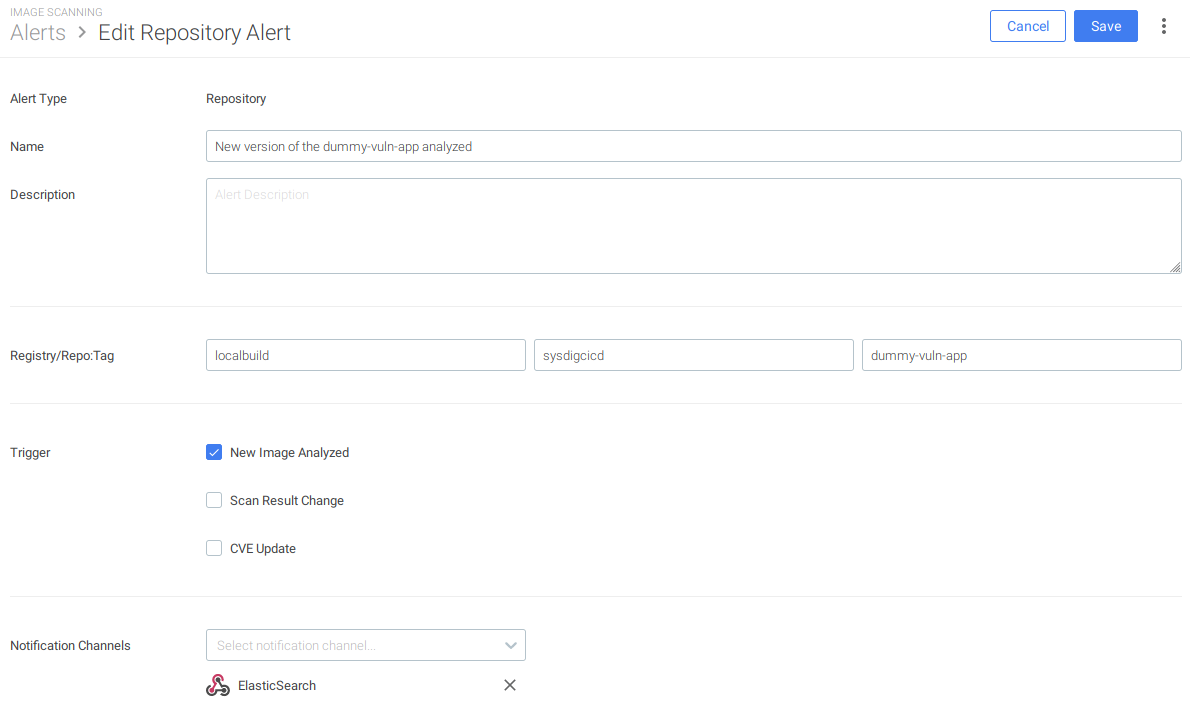
Alert creation in Sysdig Secure for a repository.
\r\r
Conclusions
\r\r
Image Scanning for AWS CodePipeline allows DevOps teams to detect problems earlier in the CI/CD pipeline, when the context is recent; this improves security, delivery, and raises their confidence in running their images in production.
\r\r
Using Sysdig, we can scan the images we build in AWS CodePipeline, without having them leave the infrastructure, and without needing a staging registry; this enables the possibility of running multiple scans in parallel and improving the throughput.

