Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

In support of modern application development built on CI/CD, containers and open source, Google Cloud launched Artifact Registry (now generally available), a new artifact management solution. Sysdig helps DevOps teams using Artifact Registry confidently secure the build pipeline with comprehensive image scanning that identifies container vulnerabilities and misconfigurations to reduce risk.
In this blog we'll describe what makes Artifact Registry unique and explain how to take advantage of Sysdig Secure image scanning to ensure the security and compliance of container images headed for production.
What is Artifact Registry?
Artifact Registry is the evolution of Google Container Registry. It provides a single place to store, manage, secure, and share container images as well as language and OS packages. Artifact Registry is fully integrated with Cloud Build, Google Cloud's CI/CD platform, and other popular CI/CD and security tooling, giving developers and DevOps teams secure, private, build artifact storage anywhere Google Cloud is available.
"Google Cloud's Artifact Registry gives DevOps teams greater control over software delivery processes," said Juan Sebastian Oviedo, Product Manager at Google Cloud. "We're excited that Sysdig is delivering their capabilities in container security and monitoring to help organizations secure and gain greater visibility into their software supply chains."
Artifact Registry on GCP delivers several new features to support secure and efficient DevOps processes, including:
- Support for regional repositories
- VPC service controls
- Granular per-repository access controls
- Customer Managed Encryption Keys (CMEK)
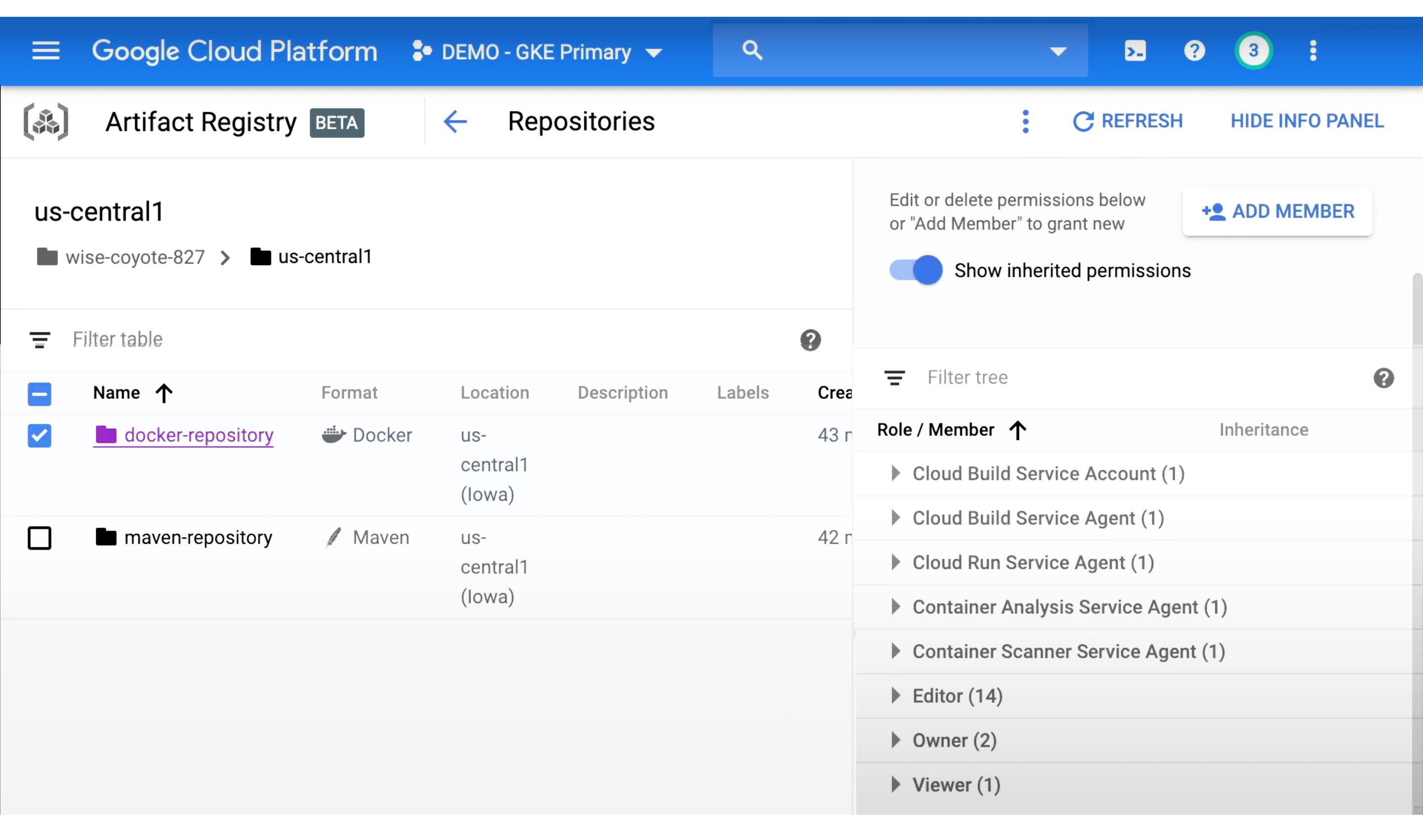
To get the complete picture of what Artifact Registry has to offer, visit the product page on the Google Cloud's website.
Sysdig Secure image scanning with Artifact Registry
One of the challenges developer and DevOps teams face is how to manage container security risk without slowing down application delivery. Image scanning is a first line of defense that helps you analyze image contents to detect and block security issues, vulnerabilities, and misconfigurations before they are pushed into production.
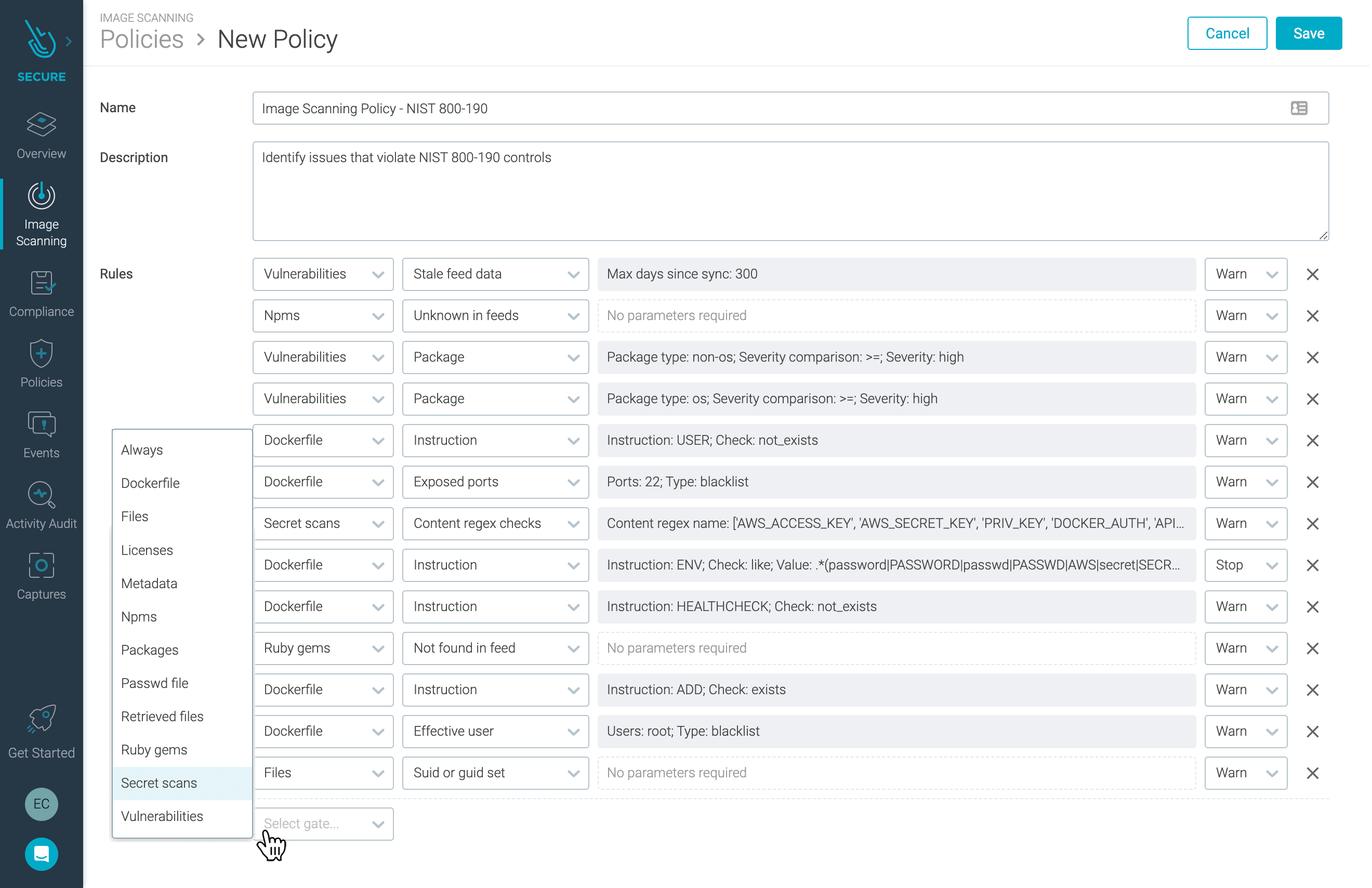
Sysdig Secure automates image scanning to identify image vulnerabilities within CI/CD pipelines and registries, as well as in production. Using what Sysdig calls ImageVision, Artifact Registry users can automate detection of vulnerabilities and misconfigurations for a range of image aspects. Pre-configured policies detect general security threats and bad practices as well as map to security and compliance standards like PCI DSS or NIST 800-190.
In addition, customizable image scanning policies let you fine-tune the validation of image contents including OS packages, unofficial packages and third-party libraries. You can also check for risky configurations like images set to run as a privileged user or the inclusion of sensitive secrets and passwords. In addition, you can set alerts and configure stop actions to block vulnerable images from running in your production clusters.
There are two image scanning approaches supported by Sysdig Secure:
- Backend scanning: Container images are retrieved, and copies are stored local to the Sysdig backend where the scanning takes place.
- Inline scanning: Container image scan takes place local to where the container image is already stored, i.e., within GCP where images are stored in Artifact Registry. In this approach, only metadata about the scan results are sent back to Sysdig.
Inline scanning provides a distinct advantage in that the contents of your container images never leave the Google Cloud infrastructure. This protects privacy and can help prevent credential leaking.
Another advantage of the Sysdig Secure image scanning solution for Artifact Registry includes the ability to identify vulnerabilities in containers running in production. What this means is that as new CVEs are reported by vulnerability databases, there is no need to re-scan images to determine whether images running in production are subject to a newly reported known vulnerability.
Artifact Registry is integrated with Google Cloud runtimes such as Google Kubernetes Engine (GKE), Cloud Run, and Compute Engine. Sysdig Secure incorporates Kubernetes metadata to add context into vulnerability reporting to help cloud teams map vulnerabilities back to specific applications and services and quickly identify the team responsible to address implementing a fix.
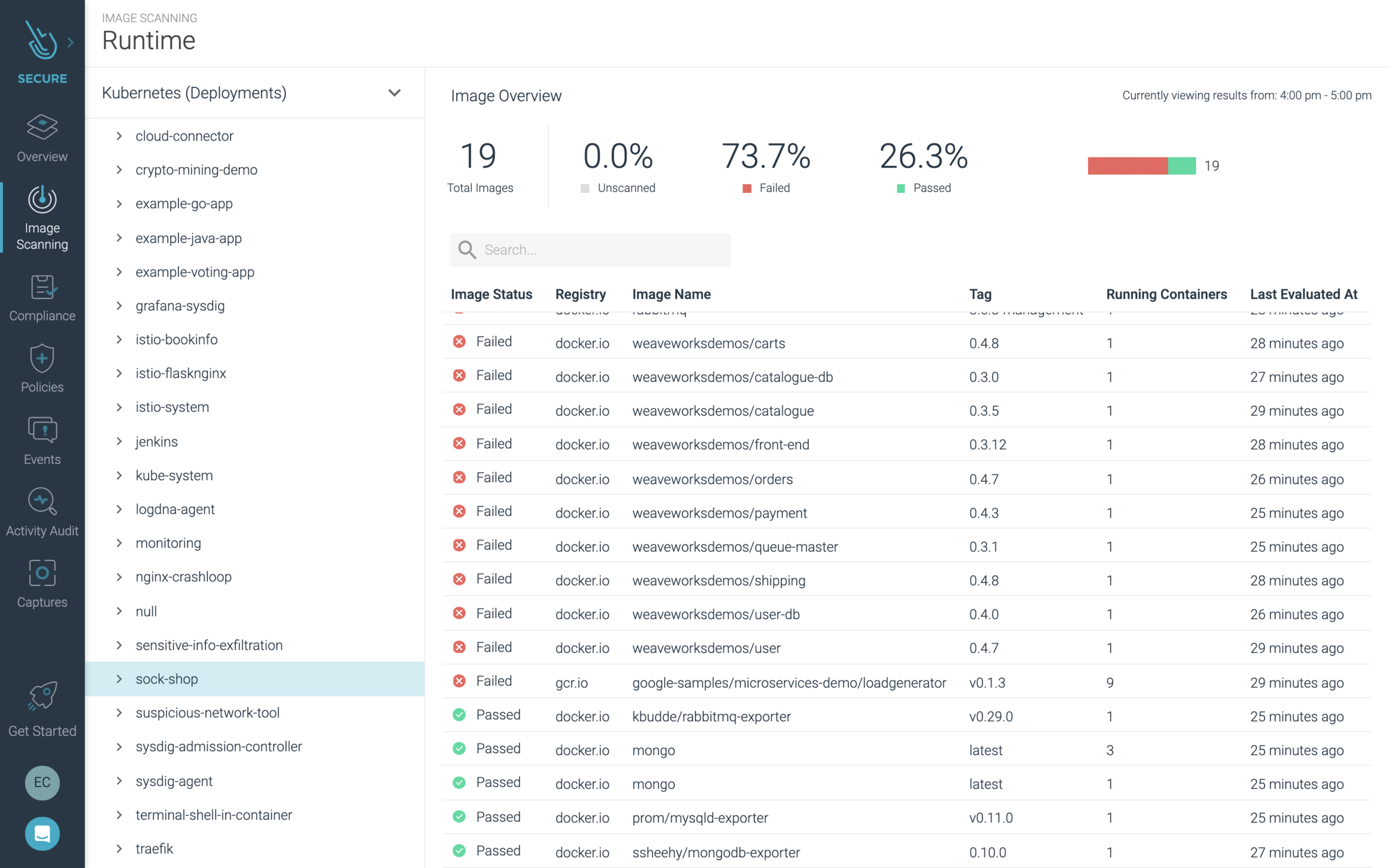
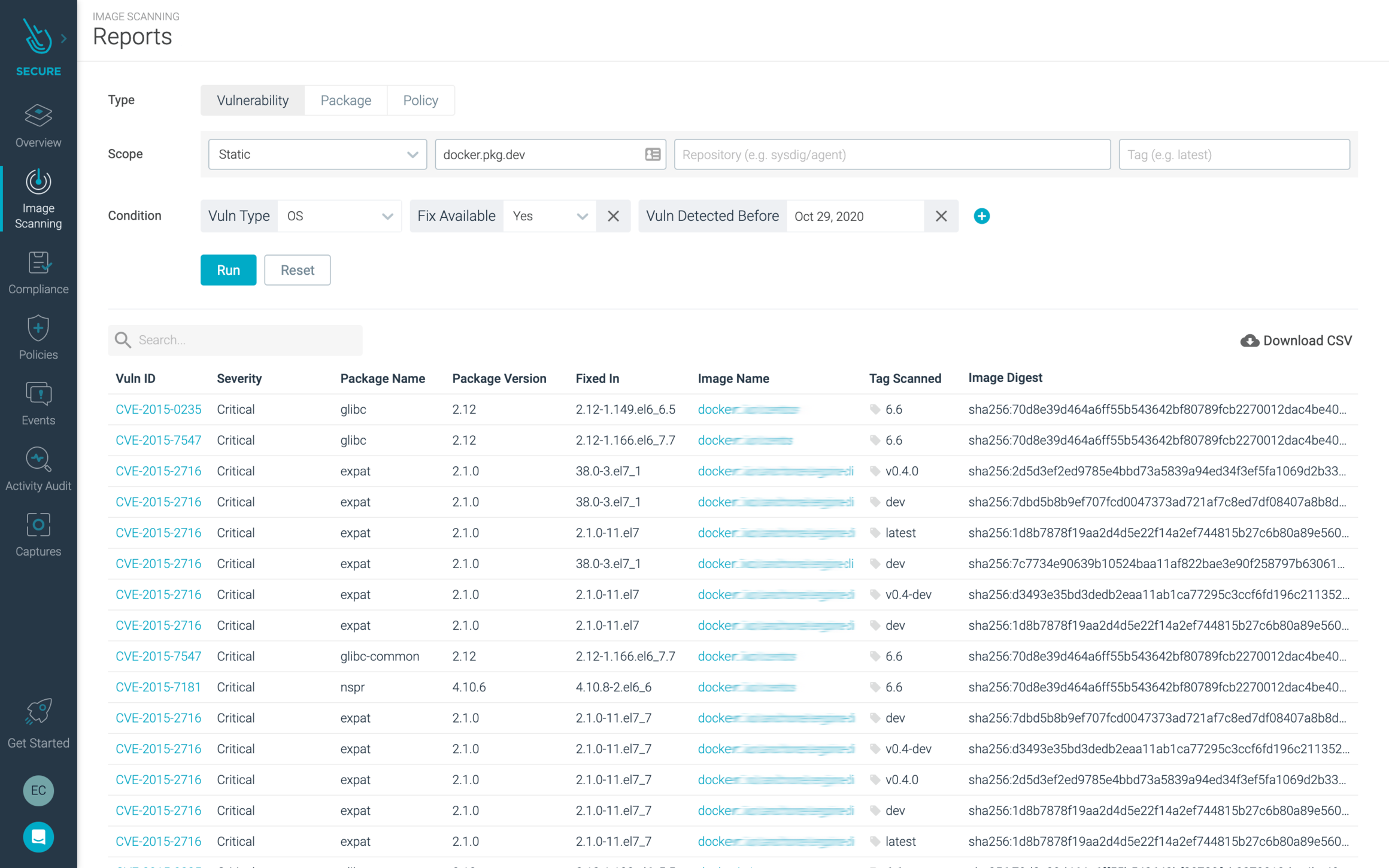
To help Artifact Registry users more easily understand the security and compliance posture of their container images, Sysdig image scanning reports allows DevOps and security teams to more easily access information about their catalog of images, packages, and CVEs to support making decisions about where to focus efforts.
You can, for instance, filter image scanning results along with parameters such as CVE age, software versions, and whether a fix is available. These reports are accessible via the user interface and can be downloaded and shared across teams to improve communication about risk and taking action to improve security.
Our goal at Sysdig is to provide enterprises with the deep visibility needed to see and stop threats to confidently run containers, Kubernetes and cloud services. To learn more about the full set of capabilities available with Sysdig, check out our platform product page.
Try Sysdig with Artifact Registry today!
Google Cloud is leading the way with innovation that is helping enterprises accelerate the delivery of cloud-native applications. By pairing Sysdig Secure with Artifact Registry, cloud teams can better secure their software delivery pipelines and keep pace change, and reduce risk in production.
You can try Sysdig with Artifact Registry today! Click here to request a free 30-day trial.


