Welcome to a new update of “What’s new in Sysdig.” Happy All Saints’/Souls’ Day! Happy International Pianist Day! Happy Thanksgiving! Happy Diwali! Glad alla helgons dag.
The “What’s new in Sysdig” blog has been rotated to a new team, and this month, Peter Andersson is responsible for the publishing. Thanks to Chris Kranz for an excellent job compiling these articles earlier. Peter has been with Sysdig since June, 2021, his role is Senior Sales Engineer, and he’s based in Stockholm, Sweden. He is a geek that loves OpenSource and sailing. When asked about this combination Peter says:
“Normal people start their boatlife with a boat. I started by building a navigation system based on OpenCPN. In true agile spirit, the first version did not work when facing production, also known as sun and water…”
Our big news this month is Cloud Infrastructure Entitlements Management, where Sysdig addresses over-permissioned accounts and roles which is the most common cloud service misconfiguration security problem. Implementing least privilege is a crucial best practice to avoid or mitigate risks of data breaches, and contain privilege escalation and lateral movement.
We are all looking forward to meeting in person and Sysdig will be attending several events across the globe, including:
- Containers Today in the Nordics: Stockholm Nov. 23, Oslo Nov. 30, and Copenhagen Dec. 2.
- AWS re:Invent in the U.S.: Las Vegas, Nov. 29-Dec. 2
As always, please go check out our own Release Notes for more details on product updates, and ping your local Sysdig contact if you have questions about anything covered here.
Sysdig Secure
Improved Handling of Forwarded Benchmark Events
Forwarded benchmark events now include AWS tags as key-value pairs (rather than a flattened string), making them easier to consume.
Cloud Infrastructure Entitlements Management (CIEM) for AWS
Sysdig Secure has added Permissions and Entitlements Management functionality. You can find it under the Posture menu tab.
By combining the CIEM capabilities announced today with Sysdig’s existing capabilities, Sysdig customers can proactively prevent cloud permissions risks, scan for vulnerabilities and misconfigurations, and detect and respond to attacks across container and cloud environments.
- Gain visibility into all cloud identities and their privileges: Get a comprehensive view into access permissions across all AWS users and services.
- Enforce least privilege: Eliminate excessive permissions by applying least-privilege policies to users and services with automatically generated IAM policies. Sysdig proposes policies based on analyzing which entitlements are granted versus which are actually used.
- Simplify audit of access controls to meet compliance requirements: Use reports for regular access reviews to evaluate active and inactive user permissions and activity.
Additional Information:
- Watch: Remediating Excessive IAM permissions in less than 2 minutes with Sysdig Secure
- Blog: Cloud Infrastructure Entitlements Management (CIEM) with Sysdig Secure
- Learn more about Sysdig CIEM capabilities
New Secure Event Forwarder Integrations: Google Chronicle, Google Pub/Sub & Amazon SQS
An extended set of output data integrations have been added to Sysdig Secure’s Event Forwarder functionality, in particular:
- Integration with Google Chronicle. NOTE: Only Runtime policy events are available as data to send at this moment.
- Integration with Google Pub/Sub and Amazon SQS, which can be used as temporary storage that will adapt the EFO push behavior into a data pull endpoint.
See also:
Sysdig Secure for GCP
We did a big press release last month, so this month we want to share some more details.
- Cloud Security Posture Management (CSPM): Based on CIS benchmarks tailored for your assets.
- Cloud Threat Detection: Identify threats in your GCP environment using Falco rules for GCP.
- Audit Logs: Google Security Command Center integration to forward threats identified by Falco rules.
- Image Vulnerability Scanning: Automatic vulnerability scanning of images pushed to Google Container Registry, Google Artifact Registry, and images executed on Google Cloud Run.
- Chronicle Integration: Events forwarding to Google Chronicle.
- Installation via GCP Marketplace: You can install Sysdig from the GCP marketplace and pay using the payment method and credit of your GCP account.
See full details: Sysdig Secure for cloud and Deploy Sysdig Secure for cloud on GCP.
Sysdig Monitor
Expose Custom Data on Webhook Notification
Sysdig gives you the ability to specify custom data and attach it to the alert notification, enabling the possibility to parse additional information and take action based on the contents.
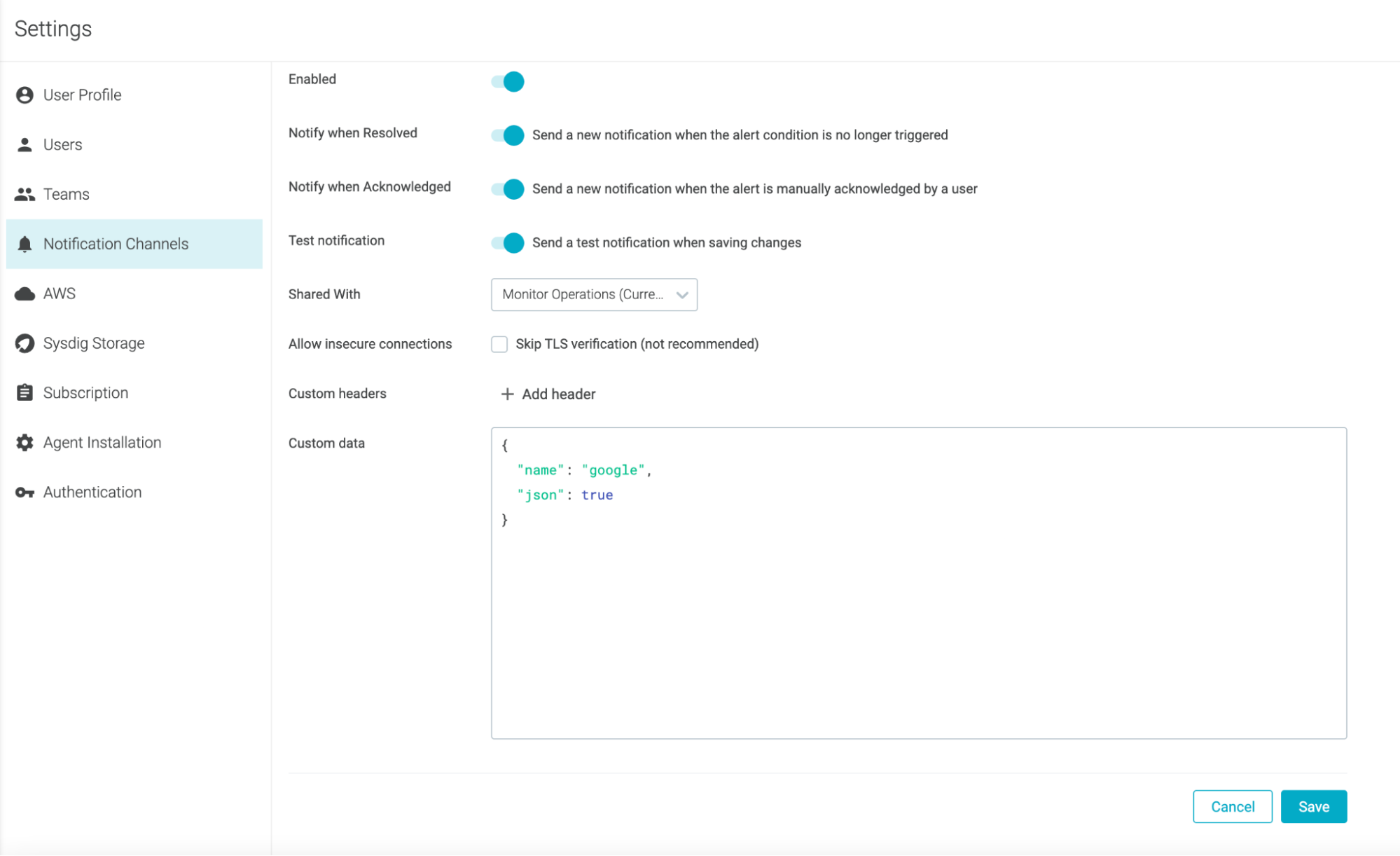
For more information, see Configure a Webhook Channel.
Prometheus Recording Rules
Sysdig now supports Prometheus recording rules for metric aggregation and querying. To enable this feature in your environment, contact Sysdig Support.
Sysdig Agents
The latest Sysdig Agent release is 12.0.4. Below is a diff of updates since 12.0.2, which we covered in our last update.
- Secure Policies Load as Expected: Fixed an issue present in 12.0.3 where Secure policies might not be loaded correctly by the agent.
- Leases Fallback Works as Expected on OpenShift v3: Fixed an issue where Kubernetes clusters that don’t support leases failed to report Kubernetes data due to not falling back to the previous behavior.
- Update the Cluster Install Scripts for Leases on OpenShift: Modified the OpenShift agent installer to add the sysdig-agent cluster role and to assign it to the sysdig-agent service account. The new cluster role allows the agent to utilize the coldstart leases.
- Added SUSE Linux Enterprise Server to supported hosts.
- Added Oracle Kubernetes Engine to support list together with installation instructions.
- Added Oracle Linux UEH and RHCK to supported hosts.
SDK, CLI and Tools
Sysdig CLI
v0.7.14 is still the latest release, which we covered in our last update.
https://github.com/sysdiglabs/sysdig-platform-cli/releases/tag/v0.7.14
https://sysdiglabs.github.io/sysdig-platform-cli/
Python SDK
v0.16.3 is still the latest release, which we covered in our last update.
Terraform Provider
v0.5.27 is the latest release. Below is a diff of updates since v0.5.24, which we covered in our last update.
Bug Fixes
- Refactor Azure Service Principal Attributes
- Azure trusted identity has been fixed from previous release 0.5.25
- Parse Azure trusted identity
Falco VS Code Extension
v0.1.0 is still the latest release.
Sysdig Cloud Connector
v0.11.3 of the Sysdig Cloud Connector was released. We covered v0.11.1 last month.
Here are some highlights of the diff between these versions:
New Features
- Updated MITRE tags for all rules.
- Added cloudtrail-s3-sns-sqs ingestor.
- Merged scanning and threat detection.
Bug Fixes
- Solved scanning not executing GCR action.
- Added schema to
gcp.resourceNameto be consumed by Google Cloud SCC. - In the
aws-cloudtrail-sns-sqsAWS ingestor create s3 service with assumeRole when it was specified.
Check the full list of changes to get the full details.
Inline Scanner
v2.4.7 is still the latest release.
Fixed support for COPY, USER, and other instructions when the image is built. This information is used to implement security gates that evaluate the Dockerfile content to prevent misconfiguration that may expose security risks. Examples of security rules that may have been impacted by the bug are “Dockerfile Effective User Type: blacklist; Users:” and “Dockerfile Instruction Check: =; Instruction: COPY.”
Sysdig Secure Inline Scan for Github Actions
v3.2.0 is still the latest release.
Added our sysdig inline scan with SARIF report as a new action into Github starter workflows. It is publicly available for any project (Your project > Security > Code Scanning Alerts > Add more scanning tools > Sysdig Inline Scan).
https://github.com/actions/starter-workflows/blob/main/code-scanning/sysdig-scan.yml
Sysdig Secure Jenkins Plugin
v2.1.12 is still the latest release.
Prometheus Integrations
New applications added:
Training & Education
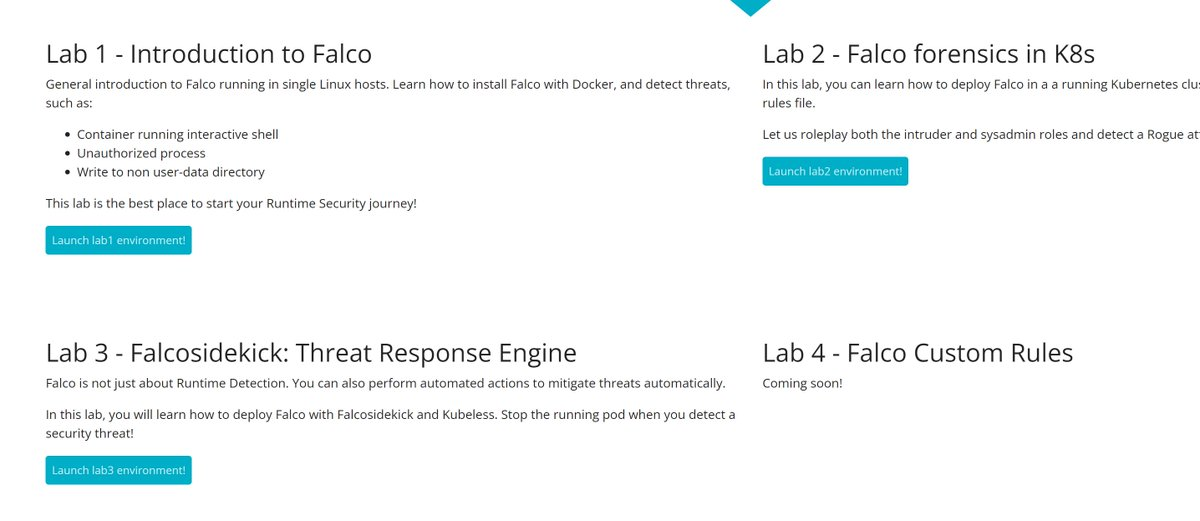
We are super proud to announce https://falco.org/labs/, a community created and led resource that helps you learn Falco in a controlled environment.
New Website Resources
Blogs
- AWS ECR Scanning with Sysdig Secure
- Challenges maintaining Prometheus LTS
- Hands-On Muhstik Botnet: Crypto-mining attacks targeting Kubernetes
- Getting started with runtime security and Falco
- Sysdig & SUSE: Security & Visibility for SUSE Rancher
- Secure software supply chain: Why every link matters
- Top key metrics for monitoring MySQL
- Malware analysis: Hands-On Shellbot malware
- Tales from the Crypt o’ mine – Four spooky short stories
- Cloud Infrastructure Entitlements Management (CIEM) with Sysdig Secure
Webinars
- Streamline the Endpoint Detection and Response (EDR) Workflow for Containers
- Continuous Compliance on Google Cloud
- Scale up Threat Detection, Scale Down False Positives in the Cloud
- Cloud and Container Runtime Security on Google Cloud
- Image Scanning on Google Cloud
- Enforcing Least Privilege Access in AWS Cloud Infrastructure with CIEM


