
Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

Amazon EKS Anywhere is a deployment option for Amazon Elastic Kubernetes Service that lets you create and operate Kubernetes clusters on-premises. With it, you can run containerized workloads in whatever location best serves your business. Carefully considering what's needed for security will help you reduce risk and safeguard against potential threats. We have validated the Sysdig Secure DevOps Platform with EKS Anywhere, ensuring AWS customers have the security and visibility needed to confidently run containers anywhere with EKS.
In this article, we'll take a look at how Sysdig works with EKS Anywhere. In addition, we'll highlight several use cases for securing and monitoring your hybrid cloud.
Running containers in a hybrid cloud model with EKS Anywhere
EKS Anywhere provides an installable software package for creating and operating Kubernetes clusters on-premises. It simplifies Kubernetes setup and management with automation tooling for cluster lifecycle support. EKS Anywhere is built on the strengths of Amazon EKS Distro (the same Kubernetes that powers EKS on AWS). Moreover, it runs upstream Kubernetes, so you can easily migrate your standard Kubernetes applications without refactoring your code.
With EKS Anywhere, you'll have a consistent AWS management experience to simplify cluster installation. To this end, it includes default configurations for OS, container registry, logging, monitoring, networking, and storage.
With the GA launch of EKS Anywhere, AWS now makes a full spectrum of deployment options available for EKS. Here's a view of the various ways you can run EKS and a mapping of who is responsible for each aspect.

Instead of contending with the management of the various components that make up the Kubernetes stack, you can take advantage of EKS Anywhere for consistent cluster deployments across locations, tested and supported by AWS. Given the pace at which most DevOps teams operate, a solution like EKS Anywhere that frees up valuable engineering time can help you get apps into production faster.
You can learn more about getting started with EKS Anywhere in this AWS blog.
Using Sysdig to secure and monitor EKS Anywhere
Sysdig is well suited for securing and monitoring EKS Anywhere. Our platform is built on an open-source stack to provide insight into Kubernetes, containers, and cloud. Sysdig's instrumentation inspects and filters Linux syscalls to help you understand the actual behavior of your containerized microservices. It also integrates with the Kubernetes API to provide context for the behavior of your workloads (e.g., which cluster/namespace/pod/container) and alert on suspicious orchestrator activity as reported by your Kubernetes audit logs.
If you're using EKS Anywhere to deploy a hybrid-cloud application environment, you'll be able to observe and secure all of your clusters from a single point. You can deploy the Sysdig agent instrumentation anywhere you need to implement security and monitoring. Regardless of whether EKS is on VMware vSphere, bare-metal, AWS Outposts, or in the AWS Cloud, you can see and manage your entire estate from one place.
To get started, you can run the agent container as a Kubernetes pod. If you use the Kubernetes DaemonSet feature, it will ensure the Sysdig agent is present on each node in your environment. Sysdig will then automatically monitor all of your hosts, apps, pods, and services, and connect to the Kubernetes API server to pull relevant metadata about the environment. If you prefer, additional install automation mechanisms are also available, such as using a Helm chart or a CloudFormation template.
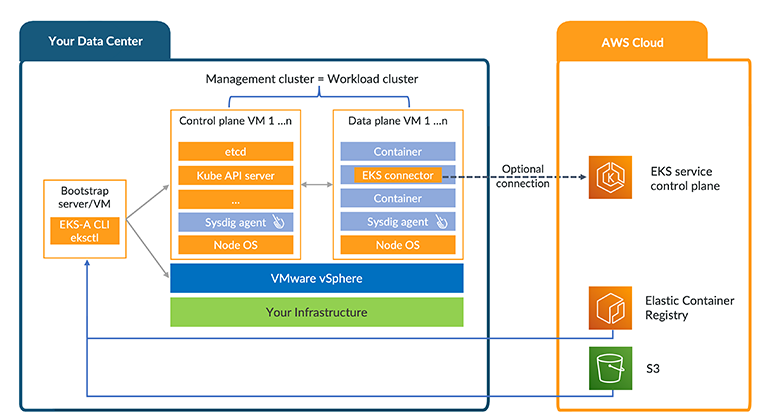
EKS Anywhere deployment with Sysdig agent
Continuous security for EKS Anywhere
The Sysdig Secure DevOps Platform is built on a number of open-source projects, including Falco, the cloud-native runtime security project. We've unified a range of security and compliance capabilities that you can apply to your AWS and EKS Anywhere environment – from the time you're building applications through production. This includes, for example:
- Image scanning to identify vulnerabilities pre-production and at runtime
- Runtime security to detect threats across containers, CaaS (like Fargate), and cloud services
- Network security to apply microsegmentation using Kubernetes-native network policies
- Compliance to control and validate adherence to regulatory standards like PCI and NIST
- Cloud security posture management to flag misconfigurations and detect suspicious activity
- Incident response and forensics to understand security breaches and recover quickly
Let's look deeper at the runtime security and compliance use cases.
Runtime security with EKS Anywhere
Sysdig's runtime security based on Falco provides container-level and cloud activity visibility, leveraging syscalls, k8s audit logs, and cloud logs to help you understand the behavior of your container applications and cloud infrastructure.
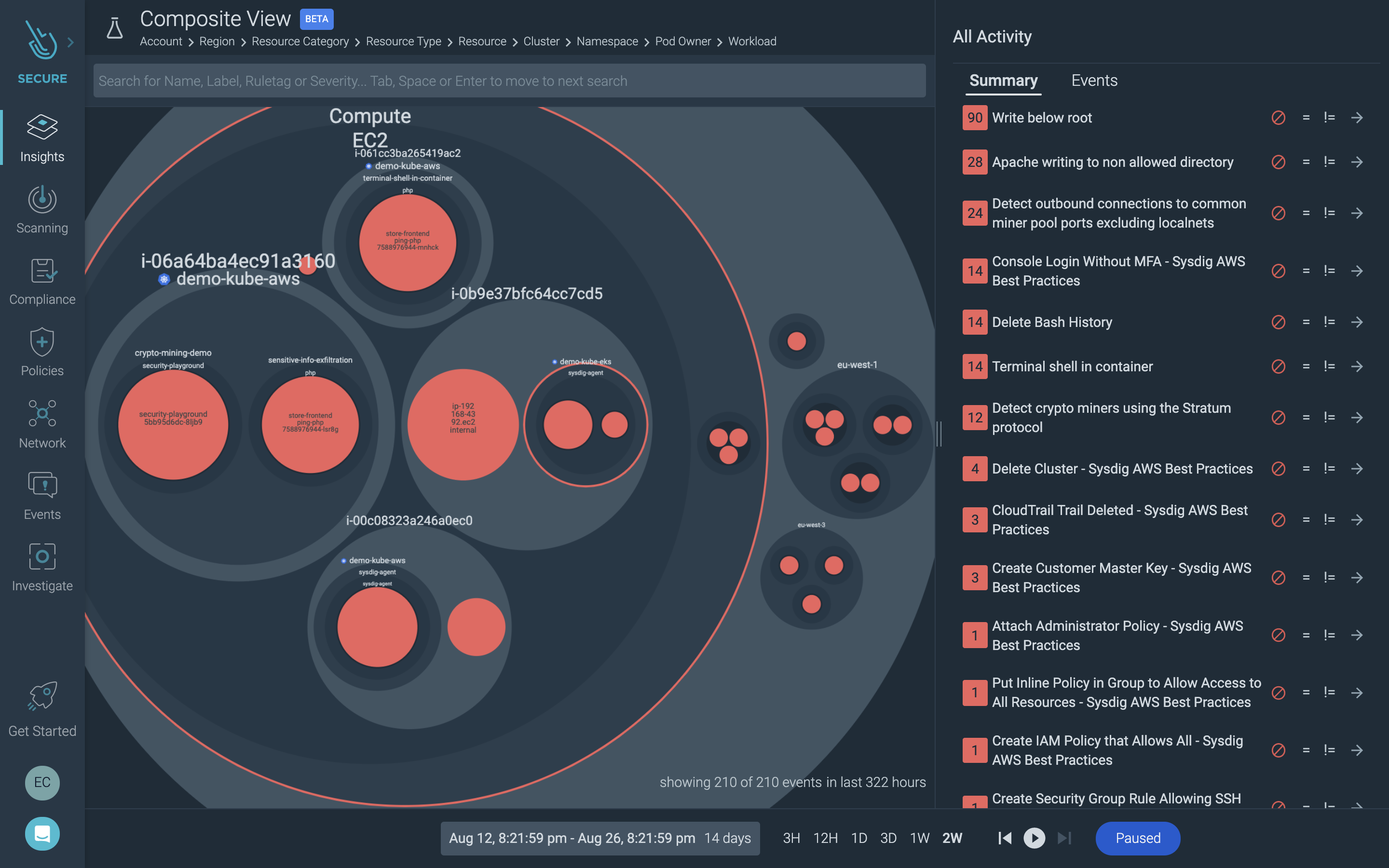
Visibility into container, Kubernetes, and cloud activity
Out-of-the-box policies and a runtime rules library let you dial in detections and alert on threats across your environments. With it, you can, for instance, spot an intrusion into sensitive data via a container running on EKS Anywhere. But you can also understand if there was concurrent suspicious access in your AWS account or were misconfigurations that possibly contributed to the breach. (Read more about our AWS CloudTrail integration here).
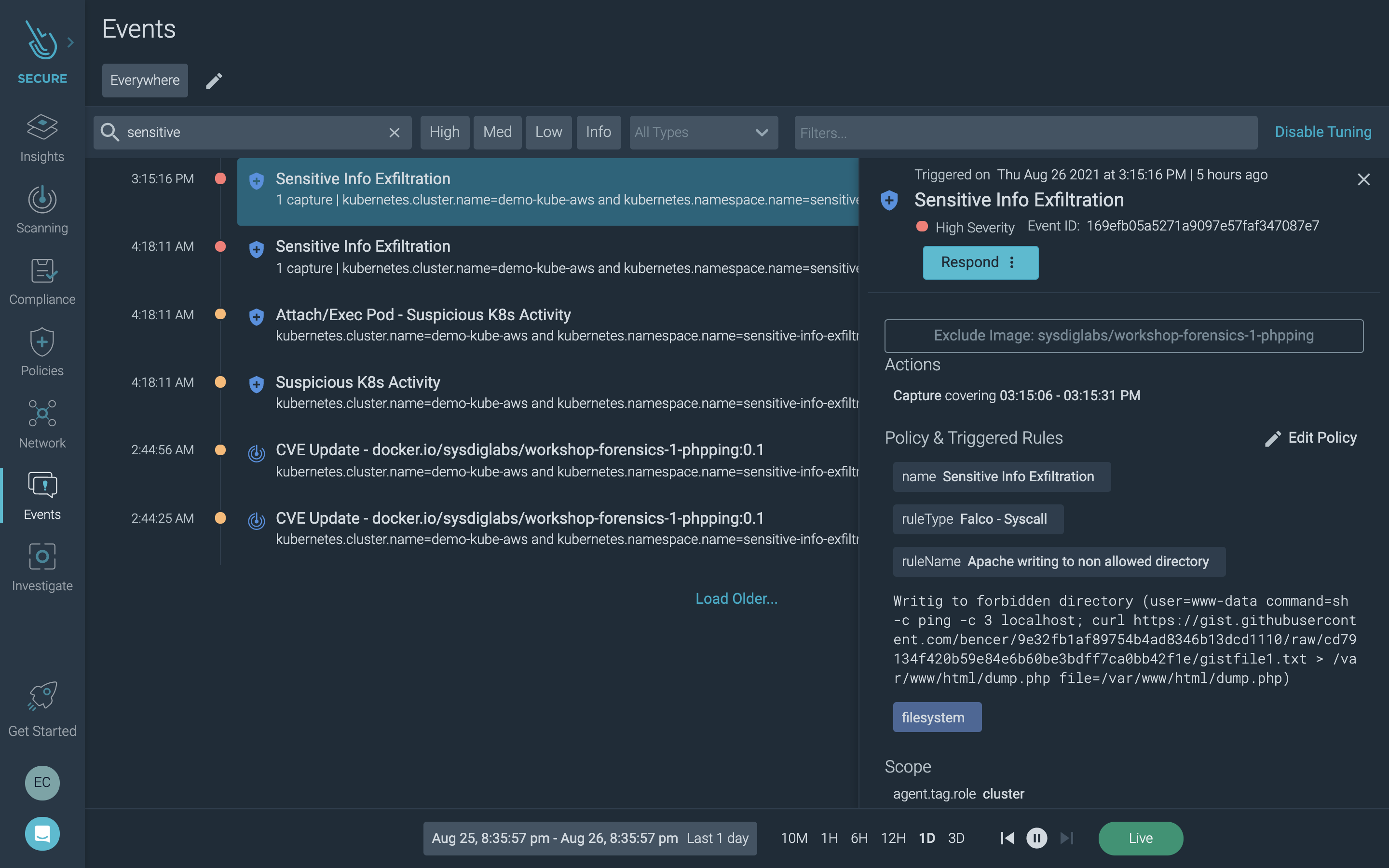
Security event investigation
One of the key values for EKS Anywhere is to provide consistent operations for cloud and on-prem so customers can free themselves from disparate operational models. Similarly, Sysdig helps alleviate the need to support different security and monitoring tools. Correlating a broader set of telemetry and event information with Kubernetes and cloud context makes the triage of incidents far more effective and less time-consuming.
Continuous compliance with EKS Anywhere
One of the drivers for EKS Anywhere adoption is compliance. In fact, customers in regulated industries have had to avoid managed services to meet mandates for strict ownership of infrastructure and data. The hybrid approach offered by EKS Anywhere lets you keep custody of containers and data locally, but still leverage a consistent AWS management experience. Consequently, you can adhere to on-prem ownership requirements while taking advantage of EKS.
Sysdig Secure supports your compliance initiatives with compliance-specific policies, as well as checks that you can turn on or off to help you meet requirements for standards such as PCI, NIST, SOC 2, GDPR, and HIPAA.
For example, you can apply image scanning policies built around compliance best practices. This maps vulnerability detections to standards like NIST and PCI to help you meet compliance requirements during the build process.
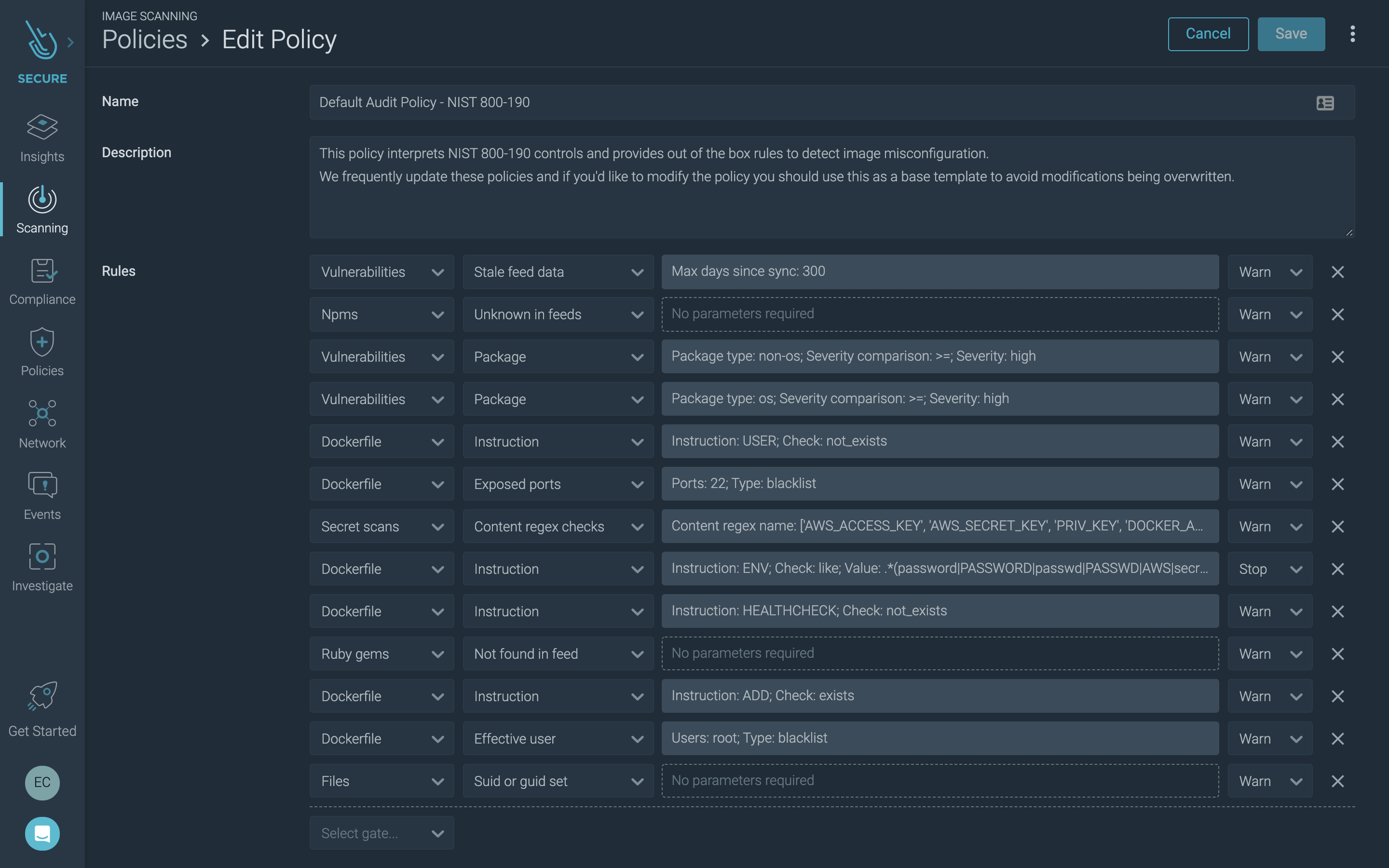
Image Scanning Audit Policy – NIST 800-190
Using Sysdig, you can also validate the compliance posture of your EKS infrastructure and workloads. For example, CIS benchmarks and other included checks help you measure progress against your compliance goals.
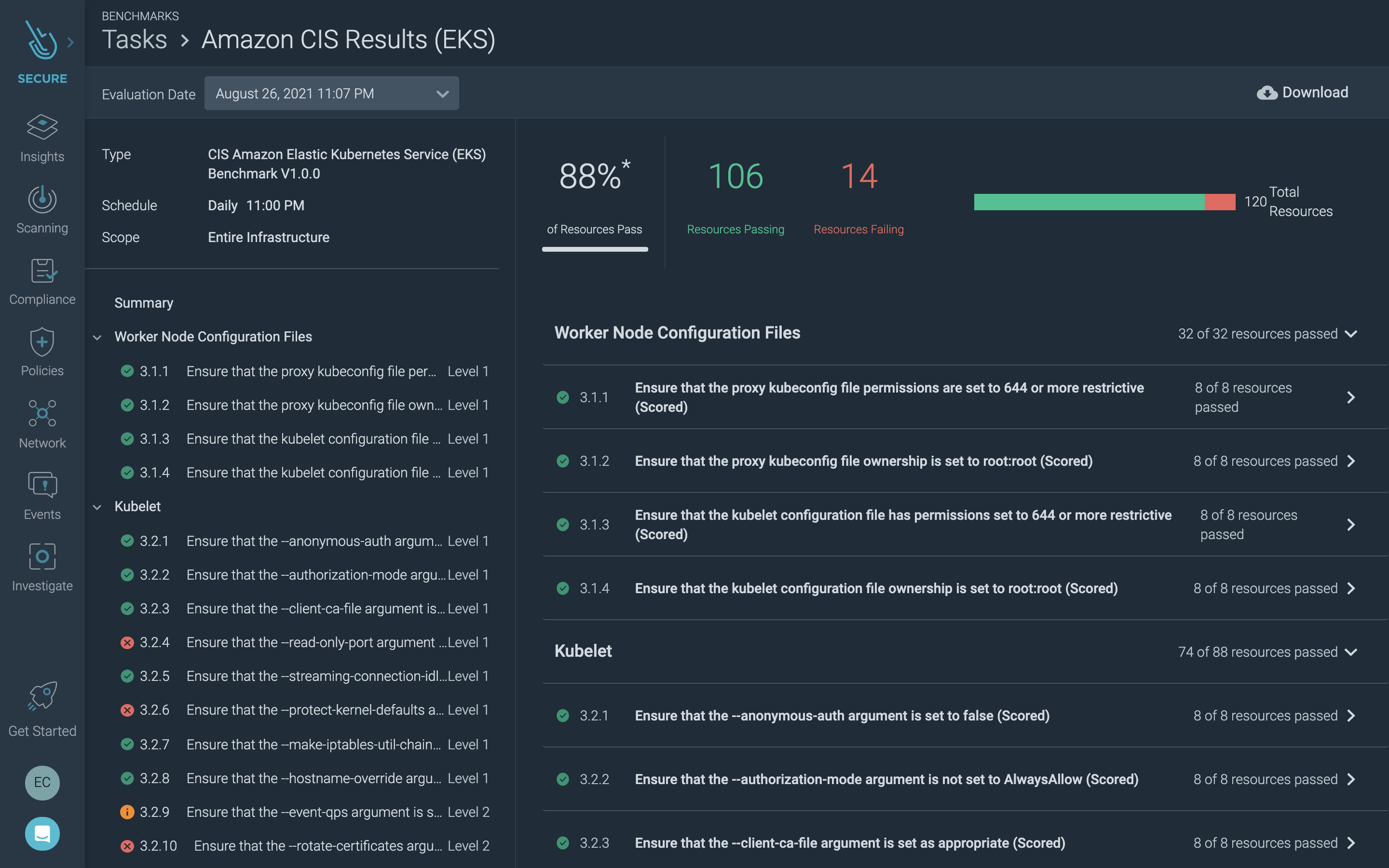
CIS benchmark for EKS
Sysdig detection rules, based on Falco, are mapped to compliance frameworks to help you implement the appropriate controls. Using this capability, you can, for instance, address File Integrity Monitoring (FIM) requirements to meet compliance standards, such as PCI DSS.
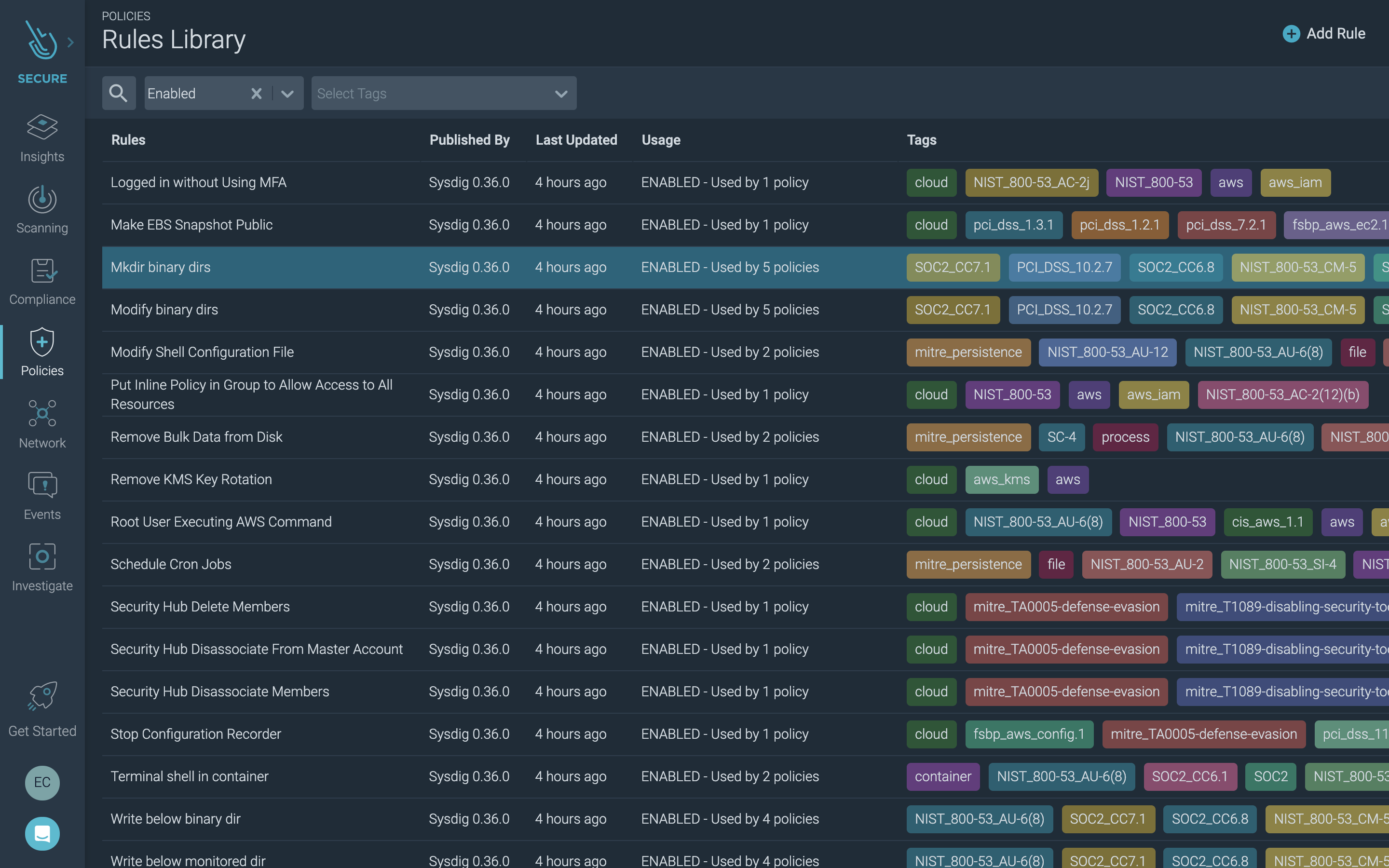
Runtime security rules tagged for compliance standards
Read more about Kubernetes security best practices in our Kubernetes Security Guide.
Conclusion
We're thrilled that EKS Anywhere is now available as a GA solution from AWS. In short, AWS is helping its customers expand their application infrastructure beyond the public cloud. Both within the cloud and in your own data center, security is something that should be carefully planned and executed. We're here to help.
Our collaboration with AWS to support all of the available deployment models means you can confidently run containers anywhere that makes sense for your business. If you'd like to check out the Sysdig product, you can get started for free! Just click here.
Amazon EKS Anywhere is a deployment option for Amazon Elastic Kubernetes Service that lets you create and operate Kubernetes clusters on-premises. With it, you can run containerized workloads in whatever location best serves your business. Carefully considering what's needed for security will help you reduce risk and safeguard against potential threats. We have validated the Sysdig Secure DevOps Platform with EKS Anywhere, ensuring AWS customers have the security and visibility needed to confidently run containers anywhere with EKS.
In this article, we'll take a look at how Sysdig works with EKS Anywhere. In addition, we'll highlight several use cases for securing and monitoring your hybrid cloud.
Running containers in a hybrid cloud model with EKS Anywhere
EKS Anywhere provides an installable software package for creating and operating Kubernetes clusters on-premises. It simplifies Kubernetes setup and management with automation tooling for cluster lifecycle support. EKS Anywhere is built on the strengths of Amazon EKS Distro (the same Kubernetes that powers EKS on AWS). Moreover, it runs upstream Kubernetes, so you can easily migrate your standard Kubernetes applications without refactoring your code.
With EKS Anywhere, you'll have a consistent AWS management experience to simplify cluster installation. To this end, it includes default configurations for OS, container registry, logging, monitoring, networking, and storage.
With the GA launch of EKS Anywhere, AWS now makes a full spectrum of deployment options available for EKS. Here's a view of the various ways you can run EKS and a mapping of who is responsible for each aspect.

Instead of contending with the management of the various components that make up the Kubernetes stack, you can take advantage of EKS Anywhere for consistent cluster deployments across locations, tested and supported by AWS. Given the pace at which most DevOps teams operate, a solution like EKS Anywhere that frees up valuable engineering time can help you get apps into production faster.
You can learn more about getting started with EKS Anywhere in this AWS blog.
Using Sysdig to secure and monitor EKS Anywhere
Sysdig is well suited for securing and monitoring EKS Anywhere. Our platform is built on an open-source stack to provide insight into Kubernetes, containers, and cloud. Sysdig's instrumentation inspects and filters Linux syscalls to help you understand the actual behavior of your containerized microservices. It also integrates with the Kubernetes API to provide context for the behavior of your workloads (e.g., which cluster/namespace/pod/container) and alert on suspicious orchestrator activity as reported by your Kubernetes audit logs.
If you're using EKS Anywhere to deploy a hybrid-cloud application environment, you'll be able to observe and secure all of your clusters from a single point. You can deploy the Sysdig agent instrumentation anywhere you need to implement security and monitoring. Regardless of whether EKS is on VMware vSphere, bare-metal, AWS Outposts, or in the AWS Cloud, you can see and manage your entire estate from one place.
To get started, you can run the agent container as a Kubernetes pod. If you use the Kubernetes DaemonSet feature, it will ensure the Sysdig agent is present on each node in your environment. Sysdig will then automatically monitor all of your hosts, apps, pods, and services, and connect to the Kubernetes API server to pull relevant metadata about the environment. If you prefer, additional install automation mechanisms are also available, such as using a Helm chart or a CloudFormation template.
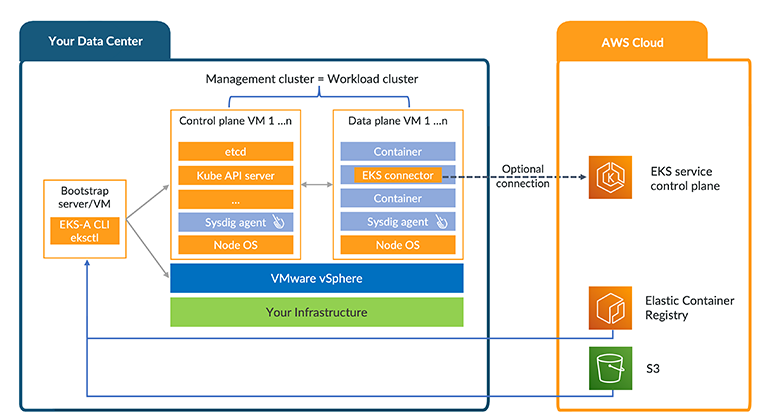
EKS Anywhere deployment with Sysdig agent
Securing EKS Anywhere
The Sysdig Secure DevOps Platform is built on a number of open-source projects, including Falco, the cloud-native runtime security project. We've unified a range of security and compliance capabilities that you can apply to your AWS and EKS Anywhere environment – from the time you're building applications through production. This includes, for example:
- Image scanning to identify vulnerabilities pre-production and at runtime
- Runtime security to detect threats across containers, CaaS (like Fargate), and cloud services
- Network security to apply microsegmentation using Kubernetes-native network policies
- Compliance to control and validate adherence to regulatory standards like PCI and NIST
- Cloud security posture management to flag misconfigurations and detect suspicious activity
- Incident response and forensics to understand security breaches and recover quickly
Let's look deeper at the runtime security and compliance use cases.
Runtime security with EKS Anywhere
Sysdig's runtime security based on Falco provides container-level and cloud activity visibility, leveraging syscalls, k8s audit logs, and cloud logs to help you understand the behavior of your container applications and cloud infrastructure.
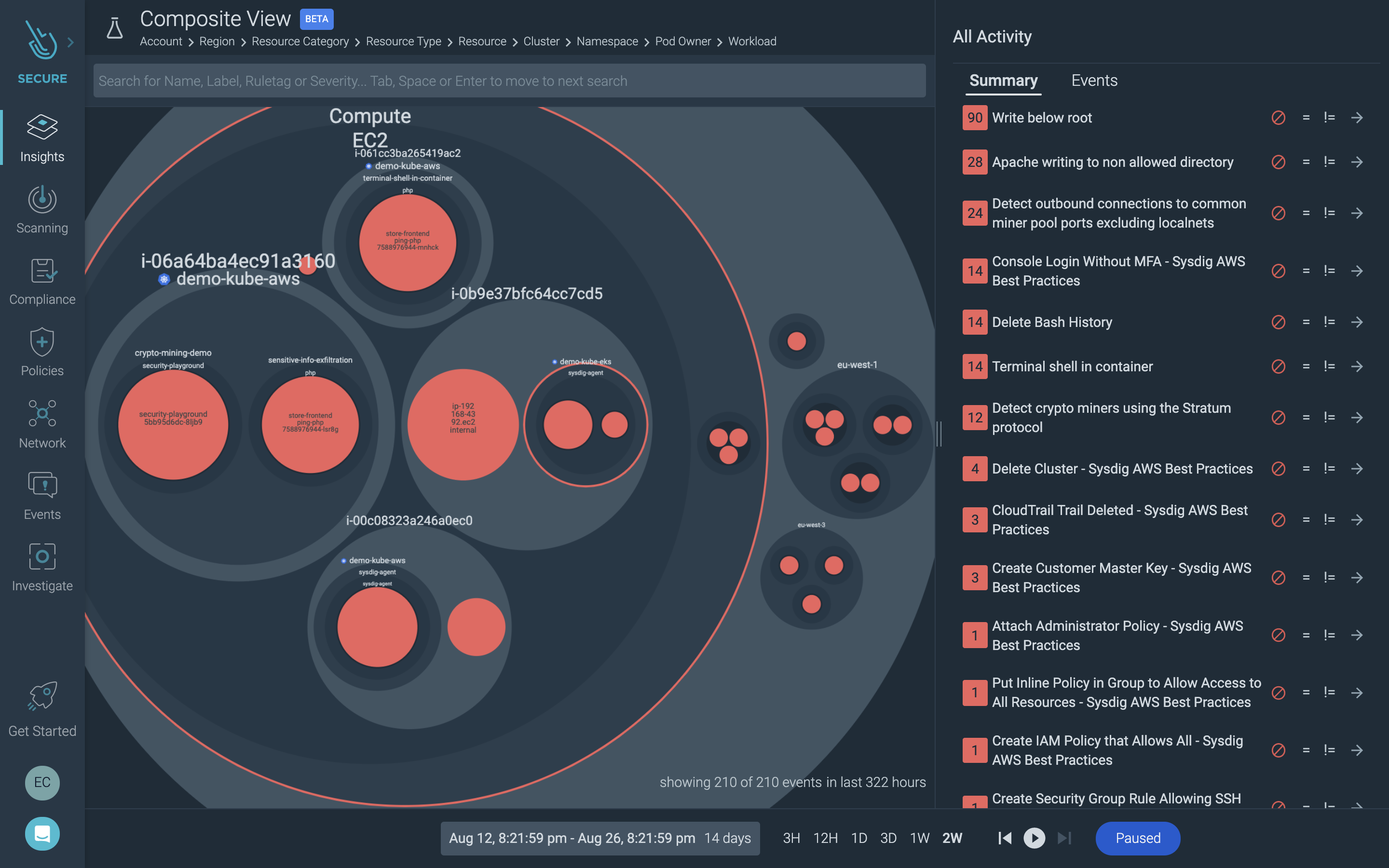
Visibility into container, Kubernetes, and cloud activity
Out-of-the-box policies and a runtime rules library let you dial in detections and alert on threats across your environments. With it, you can, for instance, spot an intrusion into sensitive data via a container running on EKS Anywhere. But you can also understand if there was concurrent suspicious access in your AWS account or were misconfigurations that possibly contributed to the breach. (Read more about our AWS CloudTrail integration here).
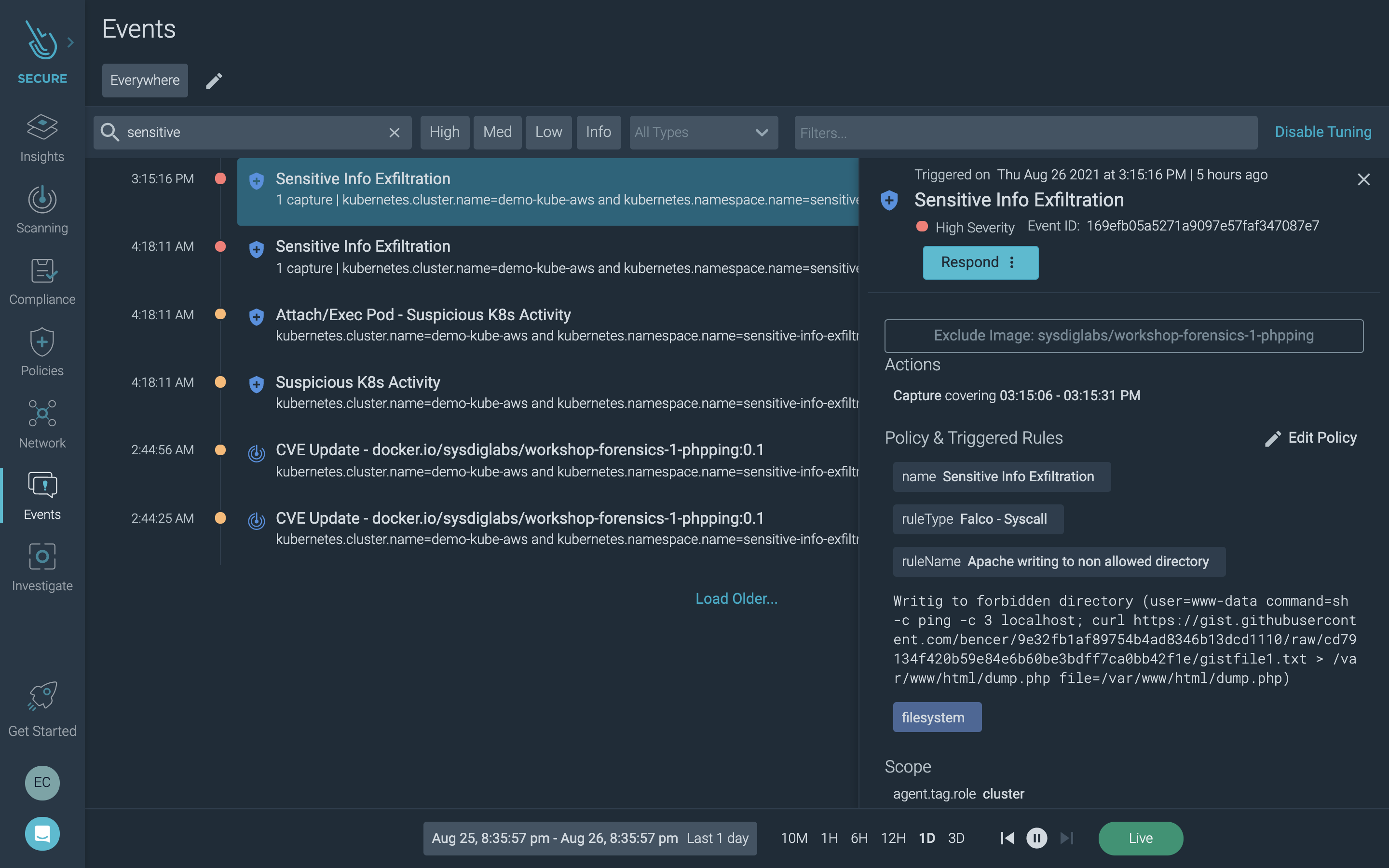
Security event investigation
One of the key values for EKS Anywhere is to provide consistent operations for cloud and on-prem so customers can free themselves from disparate operational models. Similarly, Sysdig helps alleviate the need to support different security and monitoring tools. Correlating a broader set of telemetry and event information with Kubernetes and cloud context makes the triage of incidents far more effective and less time-consuming.
Continuous compliance with EKS Anywhere
One of the drivers for EKS Anywhere adoption is compliance. In fact, customers in regulated industries have had to avoid managed services to meet mandates for strict ownership of infrastructure and data. The hybrid approach offered by EKS Anywhere lets you keep custody of containers and data locally, but still leverage a consistent AWS management experience. Consequently, you can adhere to on-prem ownership requirements while taking advantage of EKS.
Sysdig Secure supports your compliance initiatives with compliance-specific policies, as well as checks that you can turn on or off to help you meet requirements for standards such as PCI, NIST, SOC 2, GDPR, and HIPAA.
For example, you can apply image scanning policies built around compliance best practices. This maps vulnerability detections to standards like NIST and PCI to help you meet compliance requirements during the build process.
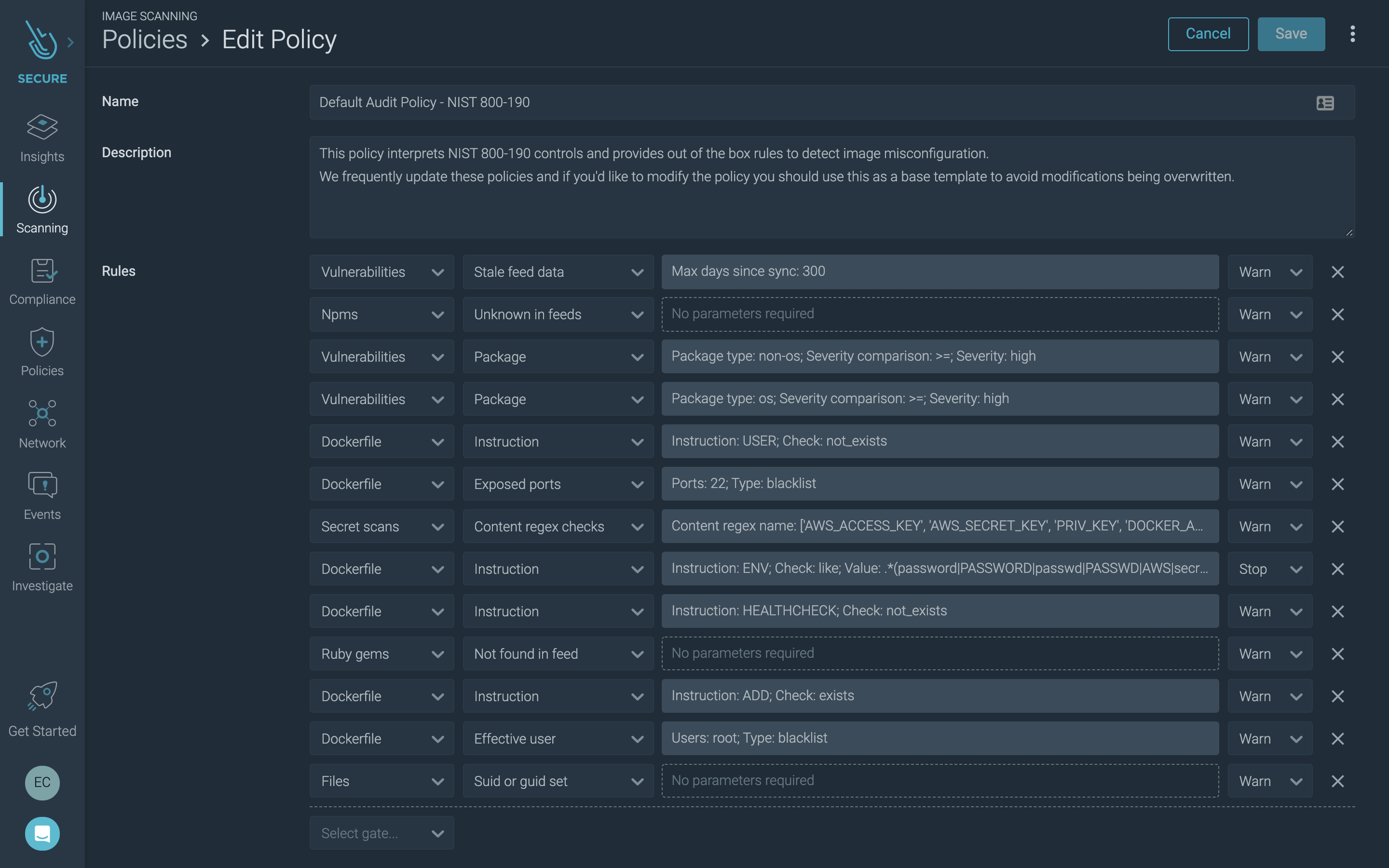
Image Scanning Audit Policy - NIST 800-190
Using Sysdig, you can also validate the compliance posture of your EKS infrastructure and workloads. For example, CIS benchmarks and other included checks help you measure progress against your compliance goals.
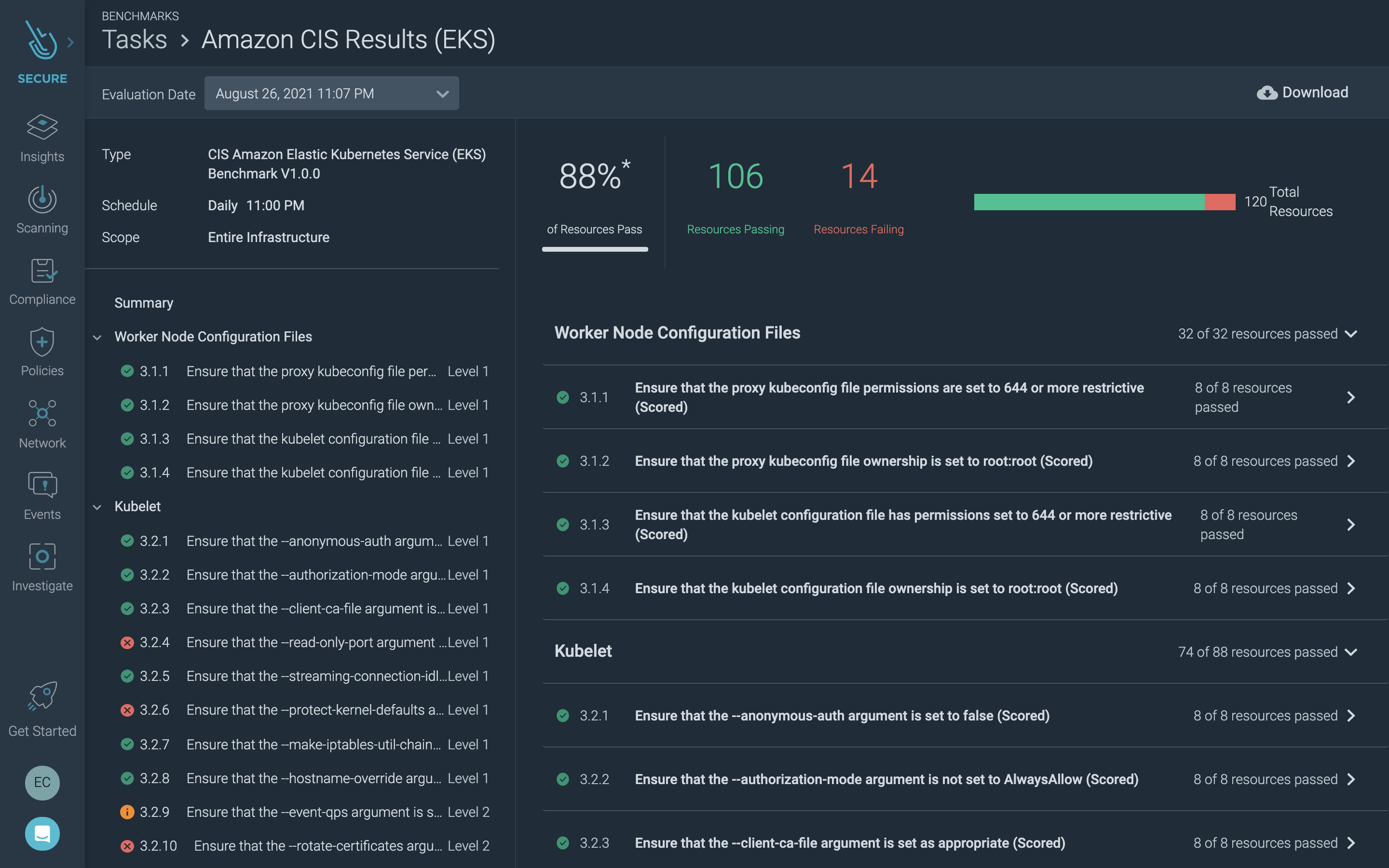
CIS benchmark for EKS
Sysdig detection rules, based on Falco, are mapped to compliance frameworks to help you implement the appropriate controls. Using this capability, you can, for instance, address File Integrity Monitoring (FIM) requirements to meet compliance standards, such as PCI DSS.
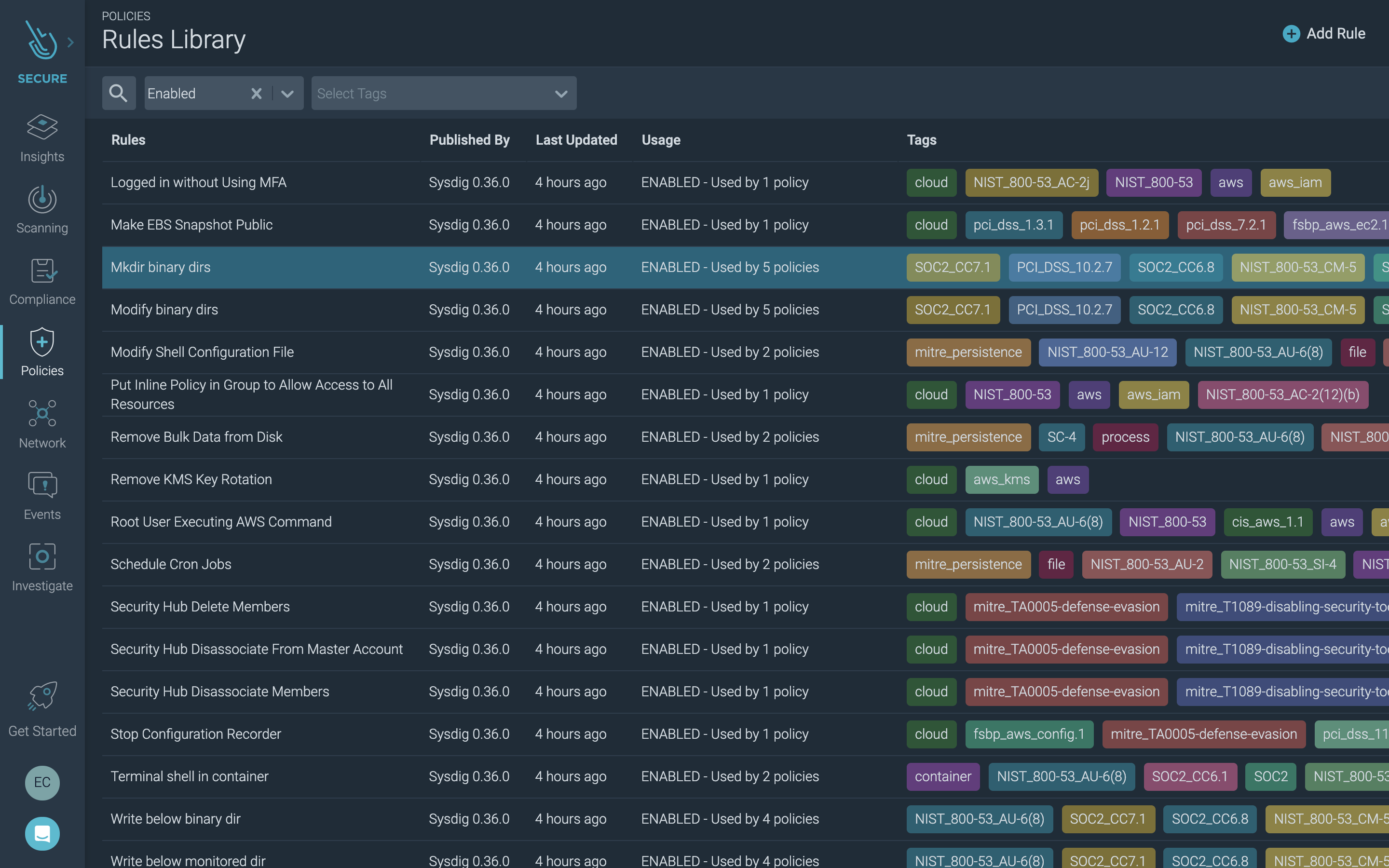
Runtime security rules tagged for compliance standards
Read more about Kubernetes security best practices in our Kubernetes Security Guide.
Conclusion
We're thrilled that EKS Anywhere is now available as a GA solution from AWS. In short, AWS is helping its customers expand their application infrastructure beyond the public cloud. Both within the cloud and in your own data center, security is something that should be carefully planned and executed. We're here to help.
Our collaboration with AWS to support all of the available deployment models means you can confidently run containers anywhere that makes sense for your business. If you'd like to check out the Sysdig product, you can get started for free! Just click here.


