Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

With today's announcement of the Wiz/SentinelOne partnership and other recent launches, like Orca/ThreatOptix, we are seeing cloud security players publicly validate that they can no longer compete without a compelling runtime security solution. Agentless technology enabled young companies to solve the low-hanging fruit problem of periodic cloud security assessment. Side scanning and API-based methods provide a solid starting point for cloud security visibility of configurations and vulnerabilities, but full, layered defense cannot be achieved without runtime telemetry and real-time threat detection and response.
In short, runtime security requires an agent, and building a good agent is difficult. Vendors who have ignored threat detection requirements thus far are now scrambling to address this need.
How did we get here?
To date, cloud security has been fragmented. It's been built from many different categories, with different acronyms, which has been challenging for teams trying to navigate their cloud-native security needs. The market category setting out to solve the end-to-end cloud security problem is known as Cloud-Native Application Protection Platforms (CNAPP). CNAPP evolved from the combination of Cloud Security Posture Management (CSPM) and Cloud Workload Protection Platform (CWPP) because neither provided sufficient security coverage by itself.
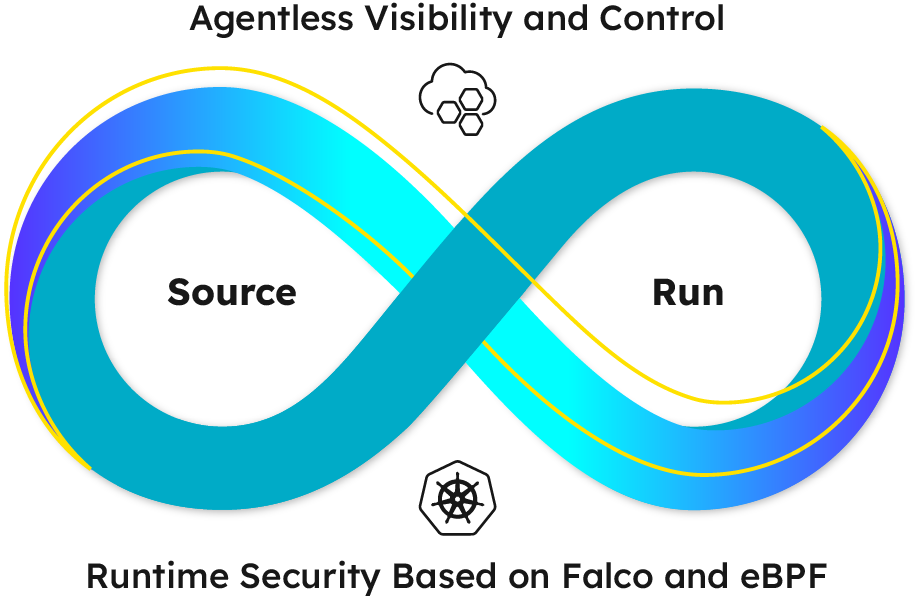
A CNAPP must address use cases including securing cloud configurations across production and infrastructure as code (IaC) source, vulnerability management, identity and access management, and threat detection and response. This full lifecycle approach is what we refer to as "shift left and shield right." CSPM tools like Wiz do a poor job of the "shield right" aspect because it requires an agent. Our fundamental position is that you need both.
I cannot stress enough, a CNAPP solution must provide real-time threat detection. Without agents, detections are delayed by hours or days, which is like not having security at all. In an era where a public S3 bucket or an exposed database is discovered in minutes, a static scan and the resulting risk posture will not prevent attacks. Given the various tools in cloud environments, detections must be enriched with context coming from a variety of sources.
No pain-free solution to adding agent-based workload protection
When a product is missing a substantial required capability, the company can choose to either build it, buy it, or partner to fill the gap. Partnering is the fastest option in terms of getting some minimal functionality into your customers' hands as soon as possible. However, partnerships, if rushed, can result in quick wins that end up as poorly integrated, loosely coupled products down the line. It's tough on customers and supporting teams.
From the perspective of EPP/EDR players, an entry into cloud-native security is not easy either. These legacy security products were not designed to handle the scale or velocity of the cloud, and simply have no way to address many cloud-native constructs like containers, serverless functions, infrastructure-as-code, or the ability to seamlessly slot into developer workflows. Moreover, securing cloud-native architectures requires correlation across user activity and workload anomalies. These capabilities must be unified under one platform, not bolted on.
A key benefit of CNAPP is the ability to aggregate risk around an application throughout its entire lifecycle. A product built from the ground up with that goal in mind to create invaluable correlations and orchestrate deep insights across otherwise siloed or disconnected components. A full-featured CNAPP does require both pre-deployment assessment and production runtime security capabilities, but duct-taping an EPP and CSPM together does not make a CNAPP.
I find today's news to be very validating for Sysdig because our approach is to use runtime insights to help our customers shift left and shield right. We solved the hard part of cloud security first, cloud-native runtime security, and over the last few years, we have covered the use cases from prevention through to detection and response. We've done this with a wide spectrum of telemetry, the use of both agent and agentless, and a complete approach to detection techniques. In a world where customers are consolidating toolsets to reduce cost and overhead, we invite them to check out the power of the Sysdig platform before adding more complexity to their program.


