Welcome to another monthly update on what’s new from Sysdig! Happy 4th of July to our American audience, and bonne Bastille to our French friends. It’s been heating up in the northern hemisphere, so we hope you’ve all been managing to stay cool and safe.
Our team continues to work hard to bring great new features to all of our customers, automatically and for free! The big news this month is our
intent to acquire Apolicy, which has everyone full of excitement. We’re already looking forward to the integrations!
As always, please go check out
our own Release Notes for more details on product updates, and ping your local Sysdig contact if you have questions about anything covered in here.
Sysdig Secure
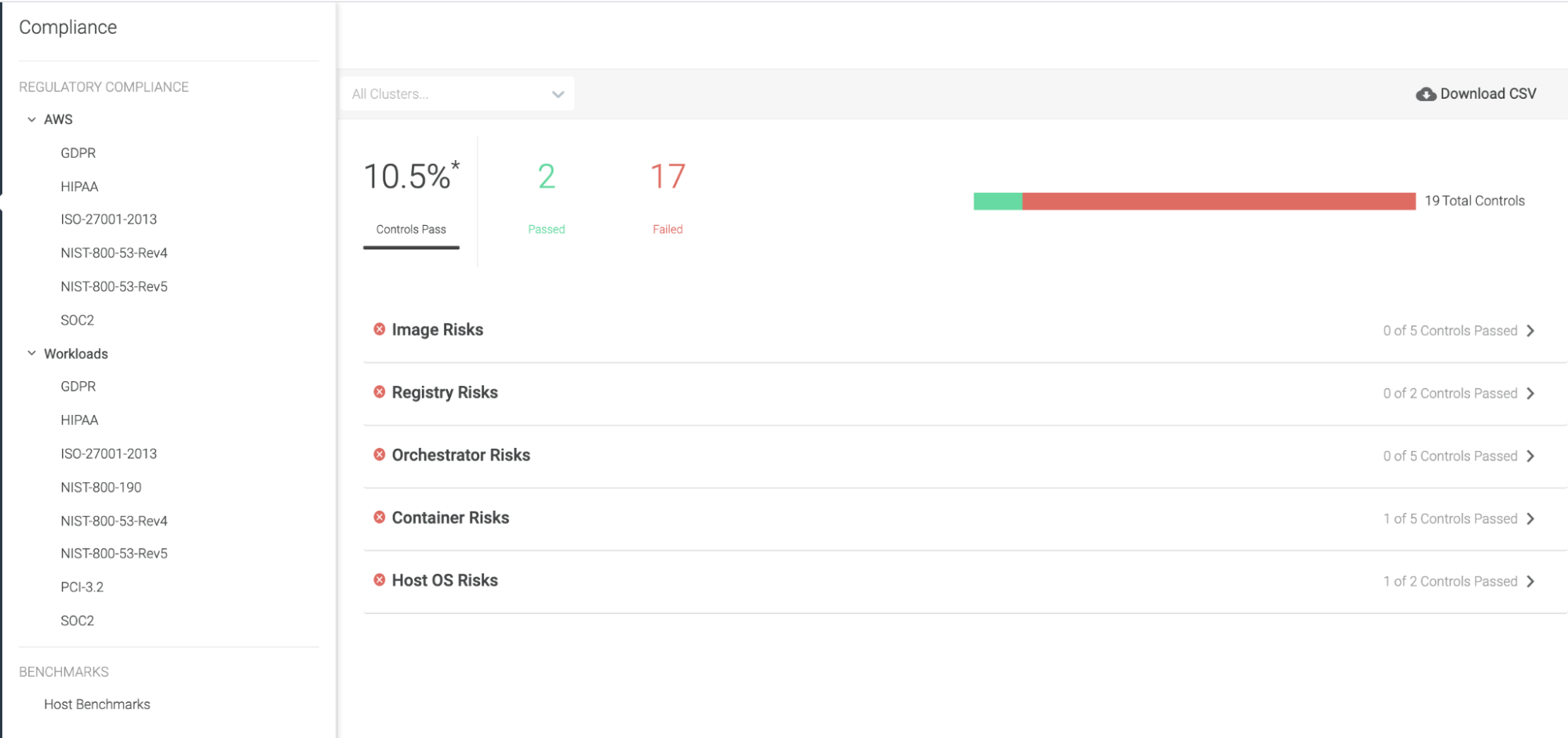
Compliance Enhancements
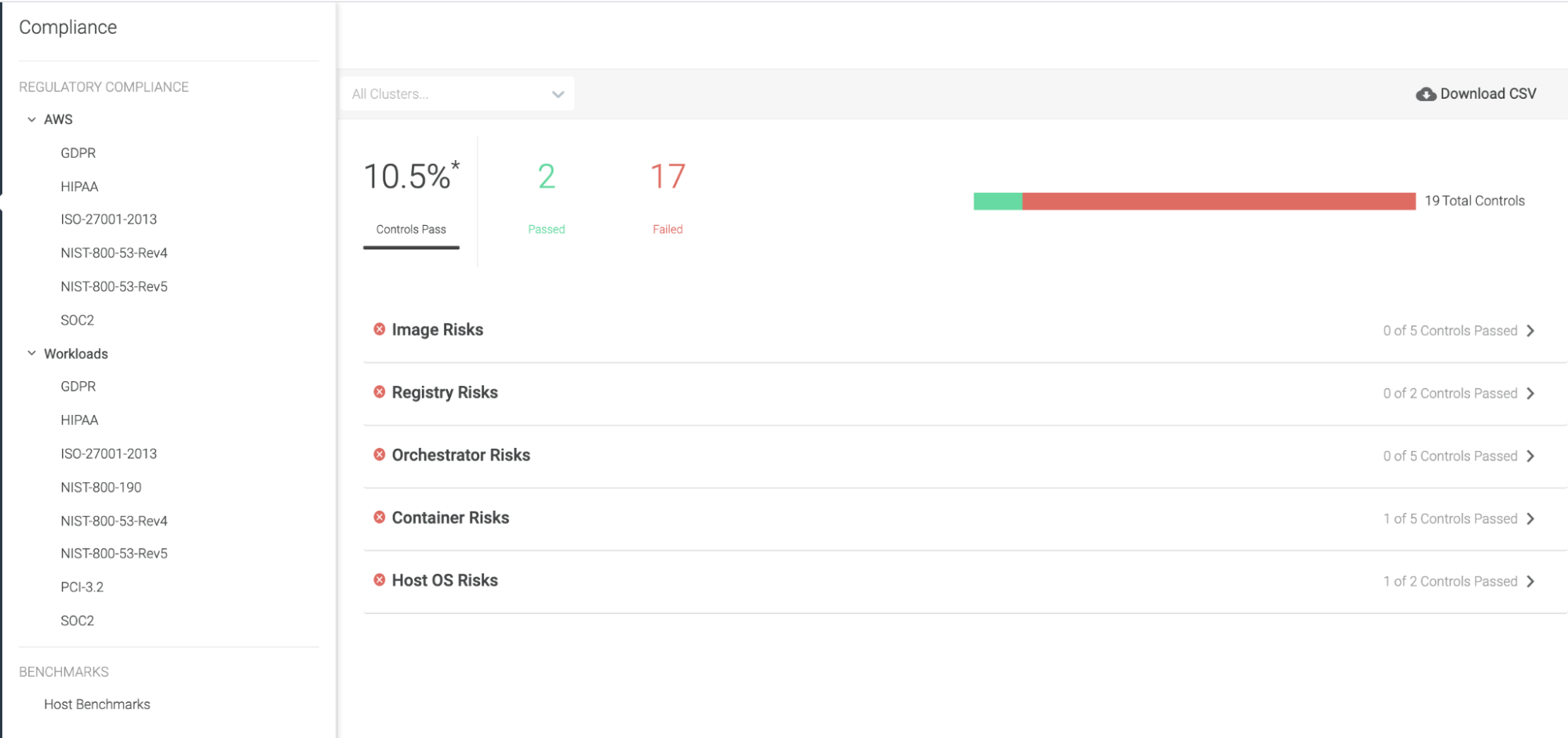
See also:
Compliance.
Extended Existing Compliance Standards to AWS
For the following existing compliance standards, we have added rules for AWS cloud provider:
- NIST 800-53 rev4 for AWS
- NIST 800-53 rev5 for AWS
- ISO 27001:2013 for AWS
- SOC2 for AWS
- HIPAA for AWS
Added New Compliance Standards
We have also added the following new compliance standards to Sysdig Secure’s offerings:
- GDPR for AWS
- GDPR for workload
- NIST 800-190 for workload
Trimmed Excess Rules from Some Standards
Certain rules have been re-evaluated and were removed because they did not significantly contribute to the security posture:
Logged in without Using MFA (merged with Console Login Without MFA)Interpreted procs outbound network activityLaunch Suspicious Network Tool in ContainerAll K8s Audit Events
CIS RedHat OpenShift Container Platform v4 Benchmark
Support for
CIS RedHat OpenShift Container Platform v4 Benchmark has been added to Sysdig Secure.
As part of this release, Sysdig is allowing you to scan and validate compliance with 112 controls included in the CIS Bencmark requirements.
See also:
Benchmarks
Falco Rules
v0.22.0 is the latest version. Below is a diff of changes from
v0.20.1, which
we covered last month.
Once again, we have a lot of changes and improvements during these versions as we continue to bring you more cloud security rules and improve our container security rules. This includes:
- Various improvements to GCP Rules handling Google Cloud Logs.
- Additional changes made to use exceptions for easier exception handling.
Check the full scope of these updates
on the Falco rules changelog.
Sysdig Agents
Sysdig Agent
The latest Sysdig Agent release is
11.3.0. Below is a diff of updates since
11.2.1, which we covered in our
last update.
In addition to the below improvements, the Sysdig Agent can also now be
installed in AWS ECS Anywhere!
Feature Enhancements
- Console Logging: Introduced per-component-level console logging feature. See Manage Console Logging for Agent Components.
- Slim Agent for eBPF Probes:
agent-kmodule and agent-kmodule-thin can now be used to build eBPF probes.
- Replication Controller Fields: Added missing replication controller fields to the aggregator Actions.
- Non-Delegated Agents Retrieve Less Data From the API Server: Use Kubernetes leases to better control the load on the Kubernetes API Server. This is disabled by default.
Defect Fixes
- Agent No Longer Generates Core Dumps on Java: Prevents java process core dumps caused by the Sysdig agent while trying to access
/tmp directory.
- Support Container Action on Containerd: Container actions are now properly supported on
containerd (CRI-O and other CRI engines that already had support). Actions for unsupported container engines are now properly reported to the Sysdig backend and a warning message is logged in the agent logs.
- Recovery During Agent Shutdown: Introduced a detection and recovery mechanism for hangs during agent shutdown.
- Promscrape V2 Termination No Longer Causes Agent Crash: Fixed a problem causing the agent to crash after
promscrape_v2 is terminated.
- Agent No Longer Restarts in Kubernetes Environment: The agent tries to fetch the metadata of the AWS instance in which it is running in order to tag metrics generated with the information unique to the AWS instance. If the metadata structure is not as expected, the agent continuously restarts due to an error in fetching such metadata. This issue has been fixed.
- Profiling Works as Expected: Fixed an issue that disabled support for performance profiles in the agent.
Sysdig Serverless Agent
The latest Sysdig Serverless Agent release is
2.0.0. Below is a diff of updates since
1.0.1, which we covered in our
last update.
New Features
- Captures Available: Announcing the availability of the Captures feature in Fargate.
Defect Fixes
- Fixed/Enabled Policy Scoping on Instrumented Fargate Tasks: At this time, only container-related scope labels, such as
container.id or container.name, are supported.
- Delay Event Source Startup by Default: The system now waits for policies to be available before launching the instrumented task, to fully secure workloads.
- Fixed Exit Codes for Faulty Workloads: The exit codes of the instrumented tasks are now faithfully propagated.
- Better Handling of cmd and entrypoint Errors: Log more informative errors when
cmd and/or entrypoint are not available for serverless agent instrumentation.
- Fixed S3 Bucket Error: Fixed an issue in the serverless agent installer that caused a failure while attempting to create an S3 bucket in us-east-1 region.
Sysdig Agent – Helm Chart
The Helm Chart
1.12.7 is the latest version. Below is a diff of updates since
v1.12.1, which we covered in our
last update.
- Update agent to 11.3.0
- Some bug fixes regarding the new Node Analyzer deployment parameters
https://charts.sysdig.com/
Changelog:
https://github.com/sysdiglabs/charts/blob/master/charts/sysdig/CHANGELOG.md
Node Analyzer
Version
0.1.12 is still the latest release, which we covered in our
last update.
v0.1.13 is the latest release. Below is a diff of updates since
v0.1.12, which we covered in our
last update.
Fixed
- Fixed a GKE- and ContainerID-specific bug where the node image analyzer couldn’t scan the image due to missing blobs.
- Implemented a few-second pause at startup to allow for Istio sidecars to complete the initialization before creating connections.
New
- We use the Universal Base Image (UBI) Sysdig-approved image as the base, ensuring the highest patch level approved by our security team.
Node image analyzer can be installed as part of the Sysdig Agent install:
https://docs.sysdig.com/en/scan-running-images.html
Inline Scanning Engine
v2.4.3 is the latest release. Below is a diff of updates since
v2.4.2, which we covered in our
last update.
Change
- Updated base image to get updated security fixes (June 2021).
Fixed
- Fixed incorrect version detection for Apache Struts 2 packages, which was leading to false positives.
See also:
Integrate with CI/CD Tools.
Admission Controller
v3.4.0 is the latest release. Below is a list of the top features from the most recent releases as we haven’t featured it in these updates before.
- Allow the use of wildcards for namespaces.
- Don’t send Activity Audit requests on attach.
- Mark k8s audit onboarding check.
- Allow to set the log level.
- Publish
kubectl exec events on Sysdig Secure Activity Audit.
- Fix
ka.req.binding.subjects to return only the list of names.
- Handle error when image is not found.
- Handle errors when evaluating according to configuration.
- Improve messages giving more context about the evaluation results.
- Make sure we trim the trailing slash from the URL.
- Add rule reloader based on the
RetryAfter parameter from the backend.
- Add a feature flag to enable K8s audit detections.
- Include build info in the logger.
- Add runtime detections with Falco K8s audit rules.
https://docs.sysdig.com/en/admission-controller.html
SDK, CLI and Tools
Sysdig CLI
v0.7.12 is the latest release. Below is a diff of updates since
v0.7.11, which we covered in our
last update.
- Add update-json option on dashboards.
https://github.com/sysdiglabs/sysdig-platform-cli/releases/tag/v0.7.12
https://sysdiglabs.github.io/sysdig-platform-cli/
Python SDK
v0.16.2 is the latest release. Below is a diff of updates since
v0.16.1, which we covered in our
last update.
- New
sdcclient.secure.ActivityAuditClientV1 to query Activity Audit events.
- This deprecates the
SdSecureClient.list_commands_audit() and SdSecureClient.get_command_audit() methods that use an old API endpoint. The methods are kept to maintain backwards compatibility in old on-prem installations, but will be removed over time.
https://github.com/sysdiglabs/sysdig-sdk-python/releases/tag/v0.16.2
Terraform Provider
v0.5.15 is the latest release. Below is a diff of updates since
v0.5.14, which we covered in our
last update.
- Enhanced error reporting from the API: Before, some API errors were reported as “422 Unprocessable Entity” without more information. Now, the provider tries to retrieve the message from the API and shows it to the user for more context on what’s wrong in the resource.
- Ignore 404 errors while removing resources: If a resource is being removed but was previously removed through the UI or other client, we can safely ignore this error.
- Documented the type parameter for the
sysdig_secure_policy resource.
- Added extra_headers documentation to the provider (for IBM users or extra headers needed for proxies).
- Updated some resource attributes documentation, mainly to report that all of them export the ID after the creation.
- Clarify team name documentation indicating that teams created in Monitor cannot be the same as the ones existing in Secure. This was confusing for some customers.
Documentation
Falco VS Code Extension
v0.1.0 is still the latest release.
https://github.com/sysdiglabs/vscode-falco/releases/tag/v0.1.0
Sysdig Cloud Connector
v0.7.13 of the
Sysdig Cloud Connector was released, we covered
v0.7.8 last month.
Here are some highlights of the diff between these versions:
New Features
- Enhanced compatibility with Falco.
- Added benchmarks to the evaluator.
- Publish images on Quay.io.
- Azure rule for not allowing SSH inbound connection to a VM.
- Azure rules for detecting function, blob, and container operations.
- Azure rules for database services, logging and monitoring, and networking.
- Updated validator for
gcp_auditlog rules.
Bug Fixes
- Don’t ship
auditlog rules.
- Don’t send the containerID and hostname right now.
- Ensure we are using a paginator to retrieve logs from CloudWatchlogs.
- Register gcp account.
- (
ingestor/eks) Don’t lose ticks when processing takes more time than interval.
Check
the full list of changes to get the full details.
Sysdig Secure Inline Scan for Github Actions
v3.0.2 is still the latest, which we covered
last month:
https://github.com/marketplace/actions/sysdig-secure-inline-scan
Sysdig Secure Jenkins Plugin
v2.1.9 is still the latest, which we covered
last month:
https://plugins.jenkins.io/sysdig-secure/
New Website Resources
Blogs
Webinars
Other Resources
 See also: Compliance.
See also: Compliance.


