Falco Feeds extends the power of Falco by giving open source-focused companies access to expert-written rules that are continuously updated as new threats are discovered.

The fifth annual Sysdig Cloud-Native Security and Usage Report digs into how Sysdig customers of all sizes and industries are using and securing cloud and container environments. We examined the data and found some interesting trends this year that may help you as you work to develop best practices for securing and monitoring your cloud-native environments.
This year's report has new data on cloud security, container vulnerabilities, and Kubernetes capacity planning. Read on to see how you stack up!
How We Got Our Data
Because our software monitors cloud security, container security, and container usage, we have a unique view of how people are using cloud services, Kubernetes, registries, alerts, and applications in cloud-native environments. This real-world, real-time data provides insight into the usage of millions of containers that a subset of our customers are running every day and billions of unique containers from the past year. The report includes a detailed look at security risks, container usage, and services deployed.
Let's take a look at some of this year's highlights. Download the full report for more.
Patchable Vulnerabilities
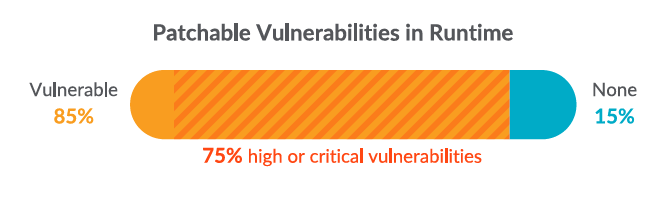
Looking at our data, we found that 75% of images contain patchable vulnerabilities of "high" or "critical" severity. Tens of thousands of vulnerabilities are discovered by Sysdig in customer environments every day. It's impossible to fix every single one. However, organizations must consider the tradeoff between delaying deployments to fix the problems or accepting security risks to release the software faster.
Dig into the data with our interactive infographic
Cloud Accounts

Configuration mistakes appear not only at the cloud account level, but also with respect to the specific resources that are provisioned. We found that 73% of cloud accounts contained exposed S3 buckets which could be putting data at risk. The amount of risk associated with an open bucket varies according to what kind of data is stored there, but this is something to watch out for.
Container Runtime
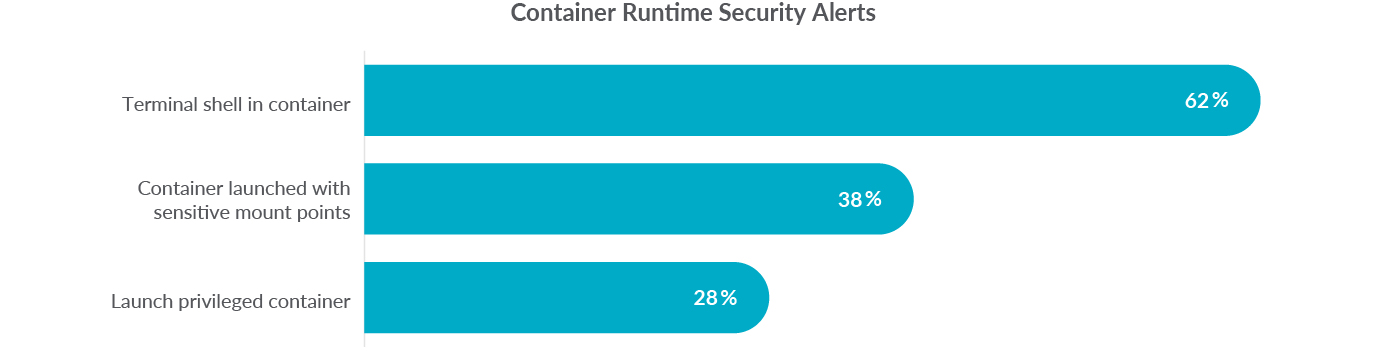
Security monitoring of containerized workloads aims to discover and impede malicious actors, as well as to identify risky exposures and reduce the attack surface. Sysdig customers regularly receive Falco security alerts indicative of poor security hygiene in these environments. We found that 62% of organizations detected a terminal shell in a container, indicating that these workloads are not being treated as immutable and increasing the risk of tampering.
Container Security

While teams understand the need to scan for vulnerabilities, they may not be scanning for common configuration mistakes. What we see is that 76% of images ultimately run as root, allowing for privileged containers that can be compromised. Part of the problem could be simply that developers did not remember to configure permissions correctly before the image was pushed to production. This is a 31% increase from last year.
Kubernetes Capacity Planning
In an ephemeral, dynamic environment like Kubernetes, capacity management and planning are inherently difficult. We found that 50% of containers have no limits defined. In environments where developers are allowed to choose their own capacity needs can lead to over allocation and these are rarely audited/rightsized. This can lead to performance problems and wasteful spending.
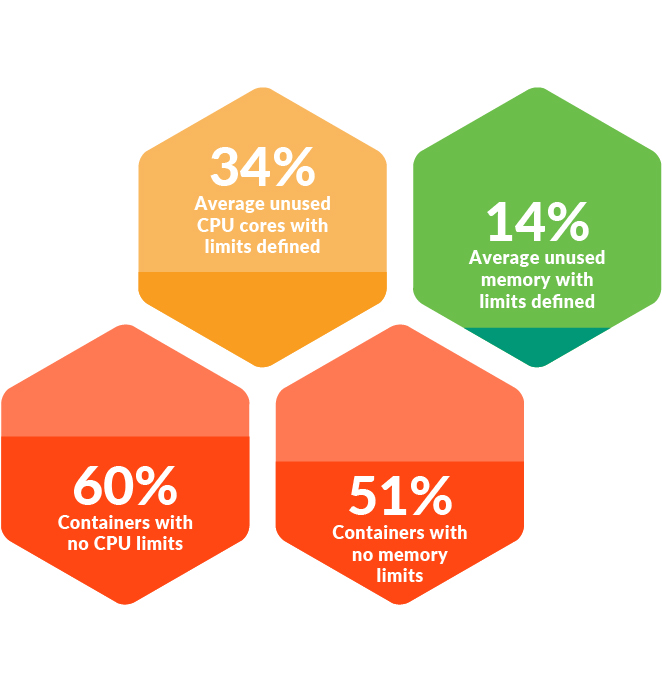
Of those clusters that did have CPU limits, an average of 34% of CPU cores were unused. Without knowing the utilization of their clusters, organizations can be wasting money due to overallocation or causing performance issues by running out of resources.
Custom Metrics
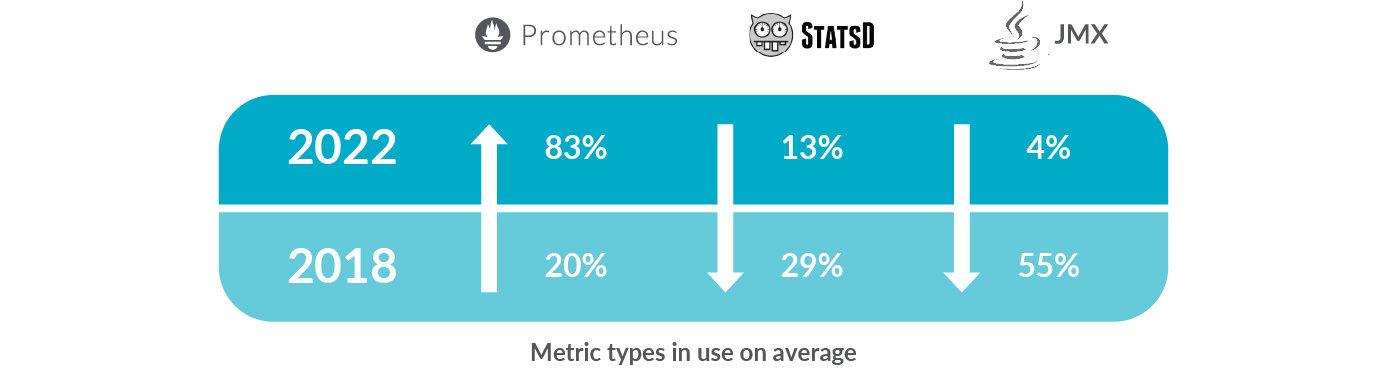
Custom metric solutions give developers and DevOps teams a way to instrument code to collect unique metrics for their applications. Year-over-year, Prometheus metric use increased to 83% compared to 62% last year. It is clear that with the strong connection between Prometheus and Kubernetes, more organizations are adopting Prometheus metrics as a standard, open source way to support cloud-native architectures.
Conclusion
Cloud technologies continue to expand their role in transforming how organizations deliver applications. With security becoming a growing concern among DevOps teams, it is good to see that teams are implementing security during the build process. However, more work is needed to secure both containers and cloud services to prevent possible vulnerabilities from entering production. Here are some best practices to follow:
- Organizations should manage access based on data sensitivity and specific use case, while abiding by the principle of least privilege.
- As organizations mature their cloud-native capabilities, they should strive to eliminate or reduce the insecure behaviors that lead to excessive alerts.
- Organizations should remember to set limits on their containers where appropriate and monitor Kubernetes resources carefully.
- Use Prometheus for custom metrics to avoid vendor lock-in.
Want more? Download the full Sysdig 2022 container security and usage report now for all the details. You can also find our past reports here.
Innovation Insight for CNAPP: 2021 Gartner® Analyst Report
Scale up your cloud security with the CNAPP framework.
The Gartner Innovation Insight for Cloud-Native Application Protection Platforms report covers the Cloud Native Application Protection Platform (CNAPP) framework and offers practical recommendations and best practices to secure your cloud native workloads and applications – from development to production – with an integrated approach. Download the report now!


