Cloud Security
Cloud Security (299)
Compliance (71)
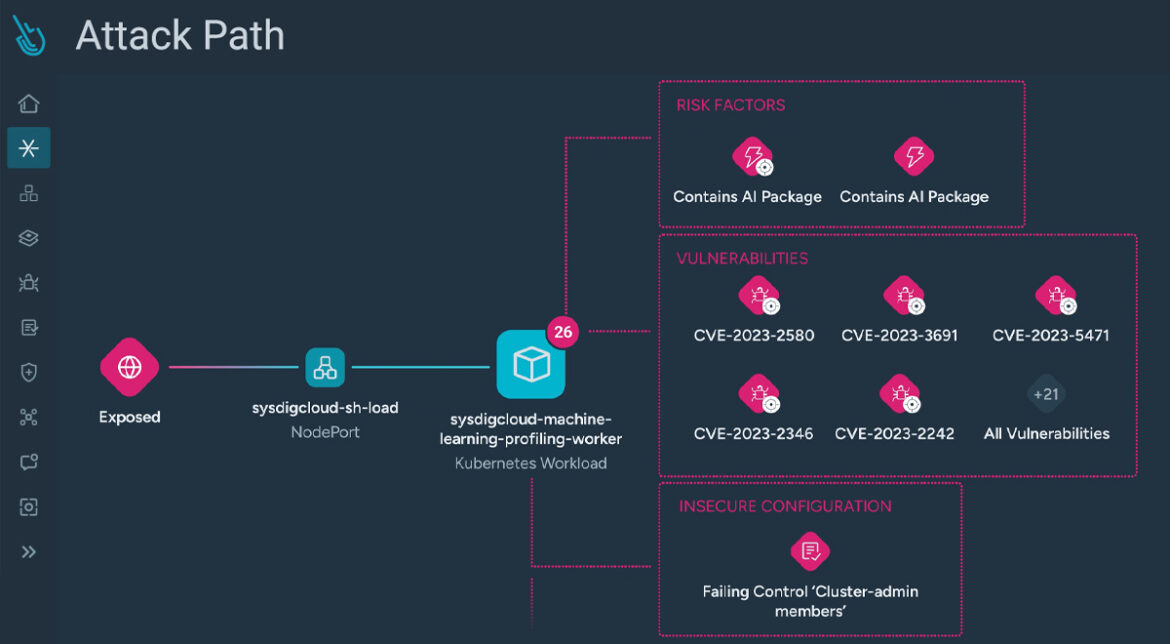
Kubernetes & Container Security (222)
Monitoring (99)
Open Source (89)
Sysdig Features (164)
Threat Research (102)
Filter By:
Showing 25-36 of 292