“What’s New in Sysdig” is back with the May and June 2023 edition!
Happy Mother’s Day! Feliz Cinco de Mayo! Merry Memorial Day! Happy Asian American & Pacific Islander Heritage Month! Happy Fathers Day! Happy Juneteenth! Happy Pride Month!
I am Sudha Duvvuri, Sr. Customer Solutions Engineer based in Texas and I am excited to share with you the latest feature releases from Sysdig.
June : This month, Sysdig has released Process Tree which enriches the Events feed for workload-based events. This helps with identifying all the processes that led up to the offending process. This is in technical preview status. Sysdig has also released Sysdig Secure Live. Secure Live (Preview) is a powerful tool that assists in the response and investigation into security events, vulnerabilities, and misconfigurations in your infrastructure under one pane of glass, with a simple way to scope on the part of the infrastructure you are investigating. On Sysdig Monitor, we introduced the new Rancher Kubernetes Control Plane (API Server, cAdvisor, Controller Manager, Scheduler, CoreDNS) integrations.
May : This month, Sysdig announced the release of a Vulnerability Management Landing Page. This is designed to support users looking to see trends, priorities, and top action items on the vulnerability risks in their environment. Also, a dedicated Accepted Risk page (Preview) has been added under the Policies UI in Sysdig Secure.
Stay tuned for more updates from Sysdig and let’s get started!
Sysdig Monitor
Change Alerts
Sysdig introduces a new alert type, Change Alerts, to help you receive alerts when a metric dynamically changes over time. Change Alerts detect cases such as sudden spikes in network traffic or a sharp fall in the number of healthy nodes.
Change Alerts have advantages over alerts based on static threshold in the following scenarios:
- Distributed infrastructure that has varying levels of traffic across different regions. In regions with significant activity, you may need to set different static thresholds for your alerts compared to the regions with lower levels of traffic. Change Alerts allow you to configure a more generic alert and to be notified when the database disk usage decreases 20% over the last 1 hour compared to the last 24 hours.
- Static thresholds can be less useful when dealing with seasonal traffic patterns. In such cases, it is effective to focus on monitoring changes rather than relying on fixed thresholds.
Group Mapping Settings API
Sysdig introduced a configuration API for Group Mapping. The API allows you to define how the Group Mapping will behave when the user has no groups or when conflicting groups exist. For example, several groups place the user in the same team with a different role. For more information, see the Group Mapping API documentation.
The feature is Generally Available.
Enhanced Agent Licenses Management API
Sysdig is pleased to announce the availability of updated Agent Licenses Management API. The API allows you to define limits, reservations, team ownership, and metadata for each access key. For more information, see Manage Access Keys.
The feature is Generally Available.
Silence by Alert
Silence rules have been enhanced by introducing the ability to silence alert notifications by alerts in addition to alert silences by scope. For more information, see Silence Alert Notifications.
Service Limit for Alerts
Service limits are the usage thresholds to help ensure that your Sysdig Monitor environment stays healthy and performs optimally. Alerts that exceed service limits will result in alert deactivation. For the conditions and service limits, see Service Limits.
Monitoring integrations
Integrations
- Introduced the new Rancher Kubernetes Control Plane (API Server, cAdvisor, Controller Manager, Scheduler, CoreDNS) integrations
- Added support for Redis Cluster option in the Redis integration
- Enhanced the Windows Prometheus bundle
- Added PromQL filters and troubleshooting metrics to Kubernetes Control Plane integrations
- Modified the configuration for Prometheus integrations jobs that use pod discovery to scrape running pods
IBM Cloud Integrations
- IBM Cloud VMware shared
- IBM Cloud VPC VSI
Dashboards and Alerts
- Added timecharts for CPU and Memory usage in Cluster Capacity Planning dashboard
- Added alert for Sysdig Monitor entitlement
- Added go_info metric to the Go integration
For more information, see Integration Library.
Sysdig Secure
Process Tree Visualization in Events Feed (Preview)
We are pleased to announce the Technical Preview release of the Process Tree feature in the Sysdig Secure events feed . This feature visually unveils the context in which the process was launched. It displays process lineage for security practitioners in a familiar EDR format to help users easily understand the relationships and dependencies between processes to accelerate incident response.
This feature requires Sysdig agent v12.15 and must be manually enabled.
Investigate Rule Change Details
In addition to the Updated badge that is now appended to Threat Detection rules, you can now also use a comparison panel to review the precise changes that were made. This applies to changes made to managed rules sets by the Sysdig Threat Detection team, as well as customizations made by users.
Improved AWS Cloud Account Onboarding
Sysdig has launched an improved onboarding experience for AWS Cloud Accounts, enabling users to specify their installation preferences regarding type, method, and desired features. Sysdig then guides you through the installation process step-by-step, ensuring a seamless and personalized experience.
In addition, Sysdig’s agentless CDR now supports threat detection on AWS CloudTrail, eliminating the need for additional computational resources. By leveraging Falco and its constantly updated rules managed by the Sysdig Threat Research Team, as well as custom rules tailored to specific environments and security requirements, users can connect their AWS accounts and organizations effortlessly while benefiting from robust event processing.
Sysdig Secure Live – Preview
What Is It? Secure Live is a powerful tool that assists in the response and investigation into security events, vulnerabilities, and misconfigurations in your infrastructure under one pane of glass, with a simple way to scope on the part of the infrastructure you are investigating.
How Does It Work?
Secure Live presents the last 24 hours of your infrastructure by scopes based on the hierarchy, such as cluster, namespace, and workloads. Selecting one of these scopes presents existing data from different parts of Sysdig Secure in a curated set of panels and tabs that are specific to that scope. As this feature evolves, more panels and “Live” views will be added, such as Posture Tab and Cloud Live.
What are the Benefits? Sysdig Secure Live provides a number of benefits, including:
- Increased visibility: Secure Live provides a unified view of your infrastructure, making it easier to identify and respond to security threats
- Improved efficiency: Secure Live can help you to automate many of the tasks involved in security operations, freeing up your team to focus on more strategic work
- Reduced risk: Secure Live can help you to reduce the risk of security breaches by providing you with the information you need to identify and address vulnerabilities before they are exploited.
What are the Limitations? Sysdig Secure Live is still under development, so there are a few limitations to be aware of:
- Limited data retention: Secure Live only stores data for the last 24 hours
- No customization: The scopes, panels, and tabs in Secure Live cannot be customized at this time
What’s Next? Sysdig is committed to continuously improving Sysdig Secure Live. In the future, we plan to add new features and functionality, such as:
- Support for more cloud providers: Sysdig Secure Live currently supports AWS, Azure, and GCP. We plan to add support for more cloud providers in the future.
- Integrations with other security tools: Sysdig Secure Live can be integrated with other datasources from Falco, such as Okta & Github. This will allow users to get a more comprehensive view of their overall cloud native security
Go to the documentation to enable the feature and get started!
Accept Risk Feature Updated
Sysdig is pleased to announce the update of the Accept Risk feature for Vulnerability Management. This update enables users to extend risk acceptance in several customizable ways to allow for more controlled acceptance scope.
Previously, accepted risk scopes for a CVE, image, or host were either global or per individual asset.
Improvements
Added support to apply image-based accepts for:
- All versions of an image
- Images in a specific registry and repo
- Images that contain strings for customized subsets of the environment
Runtime Events Dashboards
Sysdig is excited to introduce the technical preview of the Runtime Events Dashboards in Sysdig Secure. The dashboards provide a summary view as well as a trend view of all events in your infrastructure. They highlight security hotspots, while the filtering capabilities allow you to focus on a specific part of the infrastructure.
With this release, the following dashboards are available: Events Overview, Kubernetes Events, Cloud Events, and Host and Container Events.
NOTE: Only teams that are scoped to the entire infrastructure will see the dashboards.
Posture: Standalone Install Available for Linux and Docker Hosts
While Helm is the recommended installation method for Kubernetes clusters, if you want to scan a host that is not running Kubernetes, we also offer a stand-alone analyzer for compliance violations on Linux hosts.
OOTB Policy Content Updates
We are happy to announce the update of the following policies:
- CIS Google Cloud Platform Foundation Benchmark v2.0.0 (latest)
- CIS Microsoft Azure Benchmark v2.0.0 (latest)
- ISO/IEC 27001:2022 (latest)
- Lockheed Martin Cyber Kill Chain
Sysdig Secure Coverage Improvement for AWS
Sysdig Secure Posture control library has been expanded to improve its AWS resources coverage. The control library now includes new controls for the following resource types:
- Amazon Elastic Container Service (ECS)
- ECS Cluster
- ECS Service
- ECS Fargate Service
- ECS Fargate Task Definition
- Amazon Elastic Kubernetes Service (EKS)
- EKS Cluster
- EKS Fargate Profile
Sysdig Secure Coverage Improvement for GCP
Sysdig Secure has been expanded to improve its GCP resources coverage adding a total of 229 new resource types for the following services:
- AI and Machine Learning
- Cloud TPUs
- Dialogflow
- Document AI
- Speech-to-Text
- Vertex AI
- API Management
- API Gateway
- Cloud Healthcare API
- Compute
- Compute Engine
- Containers
- Artifact Registry
- Container Engine
- Container Registry
- Google Kubernetes Engine (GKE)
- Data Analytics
- BigQuery
- Cloud Composer
- Cloud Data Fusion
- Dataflow
- Dataplex
- Dataproc
- Pub/Sub
- Databases
- Cloud SQL
- Cloud Bigtable
- Cloud Spanner
- Database Migration Service
- Datastream
- Firestore
- Memorystore
- Hybrid and Multicloud
- Anthos
- Management Tools
- Deployment Manager
- Google Cloud Billing API
- Service Management API
- Media and Gaming
- Game Servers
- Transcoder API
- Networking
- Cloud Domains
- Cloud Intrusion Detection System (IDS)
- Google Cloud Virtual Network
- Network Connectivity
- Network Management
- Network Services
- Service Directory
- Operations
- Cloud Logging
- Security and Identity
- Assured Workloads
- BeyondCorp Enterprise
- Certificate Authority Service
- Cloud Data Loss Prevention
- Cloud Key Management Service (KMS)
- Cloud Resource Manager
- Secret Manager
- Serverless Computing
- App Engine
- Cloud Functions
- Cloud Run
- Workflows
- Storage
- Filestore
- Additional Google Products
- Eventarc
- Integration Connectors
- Managed Service for Microsoft Active Directory (Managed Microsoft AD)
- Organization Policy API
VM Registry Scanner 0.2.39 Supports .Net Packages and Centos OS
We are pleased to announce the release of our updated registry scanner 0.2.39 with chart 1.0.12 with the following features:
- Allowing internal ENV var to allow pageSize setup on the Artifactory client (v0.2.39)
- Registry scanning library bump, to add vulnerability management support for .Net packages and Centos OS (v0.2.38)
Please be aware that by incorporating this new source, you may discover previously unidentified vulnerabilities in assets that have already been scanned.
Vulnerability Management Landing Page for Trends
Sysdig is happy to announce the release of a Vulnerability Management Landing Page. This is designed to support users looking to see trends, priorities, and top action items on the vulnerability risks in their environment.
WHAT?
- Enable Vuln Managers easy identification of changes in vulnerability Risk Posture (trends), Most Pervasive vulnerabilities, Newest Released Vulns, and Infrastructure Segments with the most vulns
- Enable Program Managers easy insight into Policy posture on findings
- Enable Architects easy access to data regarding to the scan counts and adoption rates
WHY?
- Give a VM team an easy place to start to prioritize and manage Vulnerabilities at a program level.
Additional Notes:
- All widgets enable a workflow to take action or export data to the user’s native information security tool ecosystem
- Coming soon: addition of zones, native integration to ticketing, more sophisticated prioritization through Image Genealogy
Sysdig Secure Coverage Improvement for AWS
Sysdig Secure Posture control library has been expanded to improve its AWS resources coverage. The control library now includes new controls for the following services:
- Account
- Amazon EC2 Auto Scaling
- AWS CloudFormation
- Amazon CloudFront
- AWS CodeBuild
- Amazon Elastic Container Service (ECS)
- Amazon Elastic Load Balancer (ELB)
- Amazon ElastiCache
- Amazon Elasticsearch Service
- AWS Identity and Access Management (IAM)
- AWS Key Management Service (KMS)
- AWS Lambda
- Amazon OpenSearch Service
- Amazon RDS
- Amazon Redshift
- AWS Secrets Manager
- Amazon Simple Notification Service (SNS)
Inventory Now Supports Git Integrations
IaC code resources, supported by our Git-integrated scanner, are now available in Sysdig Secure’s Inventory:
- Easily differentiate your code from your deployed resources with our updated resource cards;
- Search and filter for IaC resources using attributes like Resource Origin, Source Type, Location, Git Integration and Repository;
- Access a 360-view of each code resource, which includes:
- resource metadata
- configuration details
- posture violations that can be remediated with automated workflows.
- Query the Secure API to get a list of multiple IaC resources or retrieve a single one.
OOTB Policy Content Updates
We are happy to announce the update of the following policies:
- CIS Docker Benchmark v1.5.0 (latest)
- CIS Amazon Elastic Kubernetes Service (EKS) Benchmark v1.2.0 (latest)
- CIS Google Kubernetes Engine (GKE) Benchmark v1.4.0 (latest)
- CIS Azure Kubernetes Service (AKS) Benchmark v1.3.0 (latest)
Registry Scanner 0.2.32 Update Available
Fixes
- Added support for http protocol registries
- Changed to honor maxRepositoriesPerRegistry on aws.org
In chart 1.0.5
Sysdig Secure Vulnerability Management Rules Improvement
We would like to inform you of an important update to Sysdig Secure’s default set of rules for vulnerability management Severe vulnerabilities with a Fix. We identified that the necessary condition “has a fix” was previously missing from one of these rules, which might have impacted the accuracy of identified policy violations. This issue has now been corrected.
Please note that as a result of this improvement, some vulnerabilities previously marked as policy violations may no longer be considered as such.
Groups Page added to CIEM
The Groups page provides numerous ways to sort, filter, and rank the detected group information to quickly remediate identity risks associated with the group’s users and policies.
Least Permissive Policy Suggestions for a group take into account all of the group’s attached user’s activity within the scope of all attached policies. Utilizing Sysdig’s Optimized Policy Suggestion can enable you to create one policy for the group that is Least Permissive.
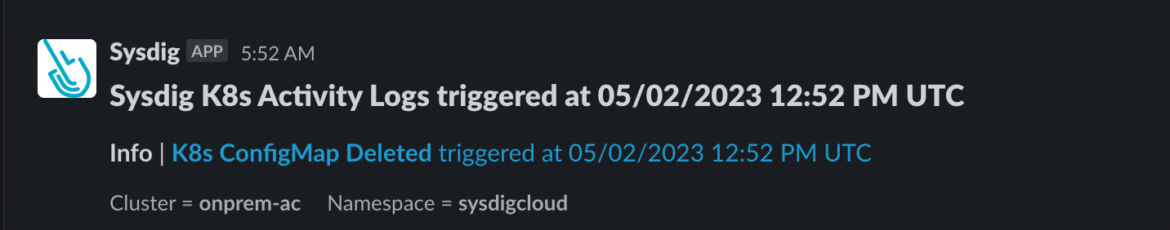
Notification Formats Updated
The notification format for the Slack and MS Teams notification channels were simplified for ease of use. The notifications now contain just the rule, policy name and context information about where the event took place. When available, a Runbook Link and Action Taken are displayed.
The user can click the link to reach the event with full details in the Sysdig UI.
Threat Detection Policy and Rule Pages Show Update Badge
Badges are now displayed on the Runtime Policies and Rule Library pages to indicate that a rule has been added or updated in the past 7 days. This includes updates performed by Sysdig’s threat research team as well as customization added by users, e.g., when specifying exception values.
Sysdig Agents
12.15.0 June 28, 2023
Feature Enhancements
Process Tree
This version of the Sysdig Agent adds support in Sysdig Secure for the Process Tree visualization which enriches the Events feed for workload-based events. This helps with identifying all the processes that led up to the offending process.
To enable this feature:
- Modify the agent ConfigMap and set enrich_with_process_lineage=true.
- Log in to Sysdig Secure as administrator and select Settings | Sysdig Labs to toggle the feature on.
The process tree will be visible in the Events detail pane for the events related to workloads that are triggered from that point on.
Added Support for Java 7
In Sysdig Agent versions 12.10.0 to 12.14.1, a Java dependency was upgraded to a version that didn’t support Java 7. As a result, those versions cannot run the Java process which collects JMX metrics on any Java 7 JDKs/JREs. This release downgrades the dependency back to a version that supports Java 7.
Added Support for Node Cost Metrics
Sysdig Agent now supports node cost metrics when using the thin cointerface.
Vulnerability Fixes
Addressed CVE-2023-0286 by upgrading the OpenSSL version in the agent to 1.1.1t.
Defect Fixes
Metrics Parity Between Secure and Secure Light Modes
The Sysdig Agent will now report the same set of metrics in both secure and secure_light modes, which means that the program metrics in secure mode will also be restricted to the dragent process or container.
Enhanced Execution Time Accounting
Fixed system execution time accounting for certain events which would cause incorrect reporting of agent I/O metrics.
Support for s390x for Ubuntu
Recent s390x Linux distributions, including Ubuntu v20.04, require the compiler to support the -march=z13/-mtune=z15 flags when building kernel modules. The gcc version used in agent-kmodule image for the s390x platform has been upgraded to gcc-12, which supports the required flags.
12.14.1 May 16, 2023
This hotfix release provides the following enhancements:
Added Support for Kernel Version 6.3
The kernel module has been updated to support Linux kernel version 6.3.
Fixed Vulnerabilities
Resolved CVE-2023-28840 in promscrape.
Fixed Probe Build Errors on RHEL6
Fixed probe build errors on RHEL6 hosts
12.14.0 May 08, 2023
Feature Enhancements
Enhanced Console Logging
The console log messages sent to stderr have been restricted to warning or higher priority only. All the lower priority console log messages are sent to stdout.
Optimize Filtering
- When using the Falco rules optimizer, remove the following redundant elements:
evt.type/evt.dir fieldsevt.arg.res = 0 checks
- When using the rules optimizer, remove the redundant
container.id != hostfield from conditions while indexing.
Improved Drift Detection in Sysdig Secure
With agent 12.14.0, drift detection is improved in Sysdig Secure. Drift detection requires a minimum kernel version of 3.18 and drift prevention requires a minimum kernel version of 5.0.
For the drift feature (both detection and prevention) to work in the 12.14 agent release, set the following in:
- The agent config file:
drift_killer:
enabled: trueCode language: Perl (perl)- Helm, add:
--set agent.sysdig.settings.drift_killer.enabled=trueCode language: Perl (perl)Added Logging to Detect Incorrect Collector Endpoints
Added detection for invalid HTTP responses on connection.
Enabled Default Scraping of Docker Containers
Sysdig Agent now supports scraping Prometheus metrics from Docker containers by default. Scraping is based on container labels.
Dependencies
- Add fmt Library: Added the fmt library to the Agent dependencies. The agent currently does not use this library.
- Upgrade Library TBB: The TBB (Intel’s Threading Building Blocks) library has been upgraded to oneTBB v2021.8.0.
- Upgrade Boost Library: The Boost library used by Sysdig Agent has been upgraded to v1.81.0.
Known Issues
- Agent not compatible with GKE Autopilot running Kubernetes v1.26
- Agent not compatible with Kernel v6.3
Defect Fixes
Restarting the Agent No Longer Causes Premature Process Termination
The SysV init script for RPM-based distributions now takes agent shutdown time into account, avoiding premature SIGKILL.
PID tracking is now enabled for systemd-sysv-generator.
Exclude JVM from Monitoring
Agent can now exclude some JVM’s from being monitored.
A set of exclusion rules can be defined in the Agent’s config. Each rule is a property/pattern pair: when the value of the given Java property matches the pattern, a process of that JVM is excluded from being monitored. For example, the following configuration will exclude OpenJ9-based JVMs from being monitored:
jmx:
jvm_exclude:
- property: java.vm.name
pattern: .+OpenJ9.+Code language: Perl (perl)Previously, this functionality was hardcoded to reject OpenJ9, but this is no longer the case. If you observe heap dumps when monitoring OpenJ9, you should add the configuration above to your dragent.yaml.
Recover from Handshake Errors Between Agent and Collector
Fixed an issue causing the agent not recovering from a bad protocol handshake.
SDK, CLI, and Tools
Sysdig CLI
v0.7.14 is still the latest release. The instructions on how to use the tool and the release notes from previous versions are available at the following link:
https://sysdiglabs.github.io/sysdig-platform-cli/
Python SDK
v0.16.6 was released.
[SP-748] Fix get_team method in #239
Terraform Provider
There is a new release v1.9.0
Documentation – https://registry.terraform.io/providers/sysdiglabs/sysdig/latest/docs
GitHub link – https://github.com/sysdiglabs/terraform-provider-sysdig/releases/tag/v1.7.0
Terraform Modules
- AWS Sysdig Secure for Cloud has been updated to v10.0.9.
- GCP Sysdig Secure for Cloud remains unchanged at v0.9.10.
- Azure Sysdig Secure for Cloud has been updated to v0.9.5.
Falco VSCode Extension
v0.1.0 is still the latest release.
https://github.com/sysdiglabs/vscode-falco/releases/tag/v0.1.0
Sysdig Cloud Connector
Sysdig Cloud Connector has a new release of v0.16.39.
Admission Controller
Sysdig Admission Controller remains unchanged at v3.9.21.
Documentation: https://docs.sysdig.com/en/docs/installation/admission-controller-installation/
Sysdig CLI Scanner
Sysdig CLI Scanner has been updated to v1.5.0.
Documentation: https://docs.sysdig.com/en/docs/sysdig-secure/vulnerabilities/pipeline/
Sysdig Secure Inline Scan Action
The latest release remains unchanged at v3.5.0.
https://github.com/marketplace/actions/sysdig-secure-inline-scan
Sysdig Secure Jenkins Plugin
There is a new release of the Sysdig Secure Jenkins Plugin, v2.3.0.
https://plugins.jenkins.io/sysdig-secure/
Prometheus Integrations
Integrations:
- Fix: Modify any Prometheus Integrations job configs which use pod discovery to only scrape running pods
- Feat: New Integration: Rancher – Kubernetes Control Plane (API Server, cAdvisor, Controller Manager, Scheduler, CoreDNS)
- Feat: PoC of an application instrumented with OTEL sending metrics to Sysdig
- Fix: Elasticsearch template in the chart
- Support: Update the syntax for Windows Prometheus Bundle process collector
Dashboards and alerts:
- Fix: Windows service dashboard is not working correctly
- Fix: Broken panels in Calico for more than one cluster
- Feat: Hide legacy MongoDB dashboard when there are no metrics for it
- Feat: Add timecharts for CPU and Memory usage in Cluster Capacity Planning dashboard
- Feat: Rename time series usage dashboard
- Fix: GCP Compute Engine dashboard has errors on some panes
Terraform EKS Blueprints Sysdig Addon
New release of v0.0.5.
https://github.com/sysdiglabs/terraform-eksblueprints-sysdig-addon
Sysdig On-premise
On-prem release v6.2.1 is now available.
- Sysdig now provides the Vulnerability Management Scanning engine for all on-premises users. This scanning engine was released in April 2022 and brings the latest vulnerability features and improvements.
Falco Threat Detection Rules Changelog
Several versions of the rules have been released in the last couple of months. Below are the release notes for the most recent.
https://docs.sysdig.com/en/docs/release-notes/falco-rules-changelog/
- Updated the IoCs Ruleset with new findings.
- Added exception for the following rules:
- Launch Privileged Container
- Launch Excessively Capable Container
- Launch Sensitive Mount Container
Open Source
Falco
Falco 0.35 is now available.
https://falco.org/blog/falco-0-35-0/
Release Highlights
- Modern eBPF probe Support
- Improving Falco performance – Adaptive syscalls
- New Falco metrics
- Falco images signing
- Improving plugins SDK
- Test infra revamp
New Website Resources
Blogs
KeePass CVE-2023-32784: Detection of Processes Memory Dump
Stop Cloud Breaches in Real Time and Accelerate Investigation and Response with Sysdig CDR
Sysdig Enriched Process Trees, an Innovative Approach to Threat Detection
Respond Instantly to Kubernetes Threats with Sysdig Live
Look both ways: Preventing suspicious behavior with end-to-end detections
CSPM, CIEM, CWPP, CNAPP: Guess who in cloud security landscape
Track Risk Trends in your Container Images with Sysdig Risk-based Vulnerability Management
Did Your Datadog Bill Explode?
Day 2 Falco Container Security – Tuning the Rules
Cloud Security: Turns Out We Needed Another Acronym (CNAPP)
Top metrics for Elasticsearch monitoring with Prometheus
Webinars
How mx51 manages security and risk without impacting innovation and efficiency
Lessons from the Trenches: Maintaining Effective Security in Cloud
Navigating Cloud and Container Security Risk
Shift Cloud Security Left and Right with CNAPP, Powered by Runtime Insights
Sysdig Education
Windows Monitoring (hands-on lab) – https://learn.sysdig.com/windows-monitoring
Intro to Secure (video) – https://www.youtube.com/watch?v=jJv4_HTxwVI
Intro to Monitor (video) – https://www.youtube.com/watch?v=SyD_4sNadAQ
Vulnerability Management Landing Page (video) – https://www.youtube.com/watch?v=1_uPQnVKZAI
Sysdig Live – https://www.youtube.com/watch?v=bo1D-jQssw8
Process Trees – https://www.youtube.com/watch?v=wqf_ZY_cqwQ


